Russian Hacking Campaign Targeting Ukraine and NATO, Attributed to APT28
- Massive data breach: A Russian hacking campaign compromised hundreds of email inboxes between September 2024 and March 2026.
- Security infrastructure failure: Cybersec researchers discovered the APT28 espionage operation after threat actors inadvertently left their server completely exposed.
- Another campaign: CERT-UA also announced cyberattacks targeting local government and municipal healthcare institutions from March to April 2026.
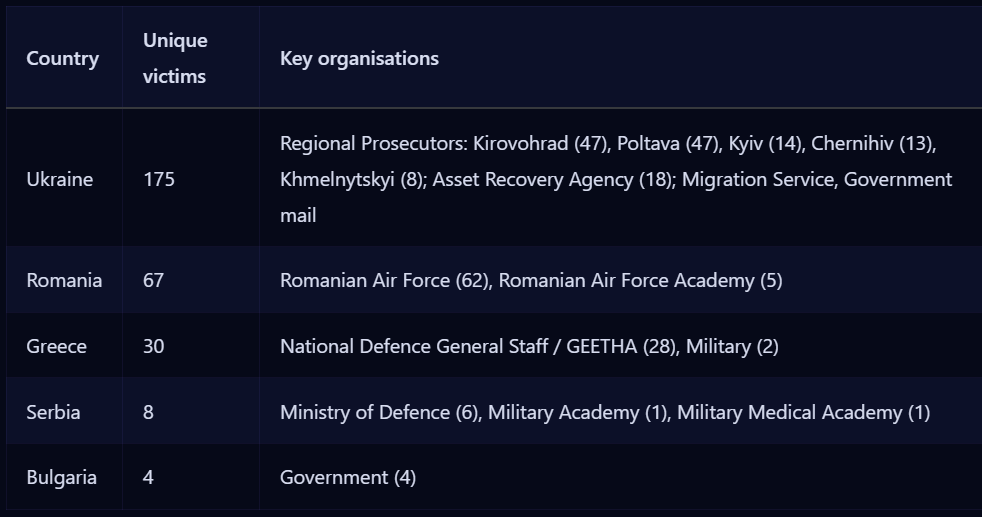
A Russian hacking campaign has successfully compromised the email accounts of over 280 officials in Eastern Europe. The breach occurred after threat actors inadvertently exposed their own server data on the public internet, revealing a vast espionage network that operated between September 2024 and March 2026 and targeted Ukraine, Romania, Greece, and Bulgaria.
The threat actors tied to Moscow systematically targeted specific government and military institutions likely to monitor ongoing anti-corruption efforts. Meanwhile, CERT-UA recorded an intensification of cyberattacks against local government and municipal healthcare institutions, such as clinical and emergency hospitals, from March to April 2026.
Ukrainian Investigators Targeted by Espionage Operations
Cyber threat research collective Ctrl-Alt-Intel discovered the leak and attributed the attacks to the well-known military hacking squad APT28, classifying it as an espionage operation. The exposed server logs provided researchers with an unprecedented view into the mechanics of modern state-sponsored cyber operations.
The primary focus of this hacking campaign centered on Kyiv, as over 170 accounts belonged to prosecutors and law enforcement personnel. With Ukrainian investigators targeted, the hackers gained access to the Specialized Prosecutor's Office in the Field of Defense and the Asset Recovery and Management Agency.
The compromised data included 67 email accounts within the Romanian Air Force and 28 inboxes managed by Greece's Hellenic National Defense General Staff. Furthermore, the attackers infiltrated local government officials in Bulgaria and military academics in Serbia.
The operation also infiltrated specialized anti-corruption offices, likely aiming to monitor investigations into Russian collaborators and gather intelligence on high-ranking officials, Reuters has suggested.
Expanding Cybersecurity Risks
The espionage operation extended well beyond Ukraine, creating severe cybersecurity risks for neighboring NATO countries and Balkan allies. Although some independent researchers dispute the exact group attribution, the consensus confirms the operation is directly tied to Moscow.
The threat actor, tracked as FancyBear by CrowdStrike, APT28 by Mandiant, Forest Blizzard/STRONTIUM by Microsoft, and Sednit by ESET, is considered to be a Russian state-sponsored threat group linked to the GRU’s 85th Main Special Service Center (Unit 26165).
The IP address associated with the 2026 OPSEC open-directory blunder was previously observed by CERT-UA on two separate occasions:
- CERT-UA#10859 - FancyBear exploiting Roundcube (CVE-2023-43770)
- CERT-UA#11689 - FancyBear using ClickFix
Last week, APT28 exploited vulnerabilities in SOHO routers, affecting 200 organizations and 5,000 consumer devices globally.
In February, APT28 was observed employing macro malware in a browser-based exfiltration operation targeting Europe. Researchers warned in May 2025 that the APT28 campaign against Western firms was intensifying to gather intelligence on aid to Ukraine.