Cyberattack on German Democratic Socialist Party Die Linke, Claimed by Qilin Ransomware
- Ransomware extortion threat: The Russian-speaking Qilin ransomware group claimed the Die Linke cyberattack, threatening to publish stolen internal data unless a ransom is paid.
- System infrastructure shutdown: Following the breach, party officials intentionally disabled segments of their IT infrastructure to mitigate further network compromise and data exfiltration.
- Democratic institution risks: This German political party data breach represents a severe escalation in targeted hybrid warfare tactics designed to destabilize democratic structures.
The Russian-speaking Qilin ransomware group has claimed responsibility for the recent compromise of the German democratic socialist party Die Linke's IT infrastructure, threatening to release sensitive operational data unless its financial demands are met. Party officials confirmed that a severe network breach occurred in late March and suspected Qilin of being behind it.
Qilin Ransomware Extortion Threats
The Qilin ransomware group, active since 2022, added Die Linke to its dark web extortion portal following the network compromise, according to several reports. While the party confirmed its core membership database remains secure, the threat actors likely accessed internal organizational files and the personal data of headquarters personnel.
“Such digital attacks, and especially the use of ransomware, are often part of hybrid warfare and an attack against critical infrastructure,” the Die Linke announcement said (auto-translated).
In response to the Die Linke cyberattack, administrators immediately deactivated vulnerable system segments to contain the infection and initiated a formal criminal investigation with German federal authorities.
This incident constitutes more than standard financial extortion; it underscores the severe cybersecurity risks facing critical democratic infrastructure. Party representatives categorized the intrusion as an element of broader hybrid warfare aimed at weakening state institutions.
Cybersecurity Risks to Democratic Institutions
This German political party data breach aligns with a troubling pattern of state-aligned threat actors targeting European political entities. Prior attacks on the Christian Democratic Union (CDU) and the Social Democratic Party (SPD), with the latter possibly orchestrated by APT28, demonstrate a sustained campaign to disrupt electoral processes and compromise sensitive political communications.
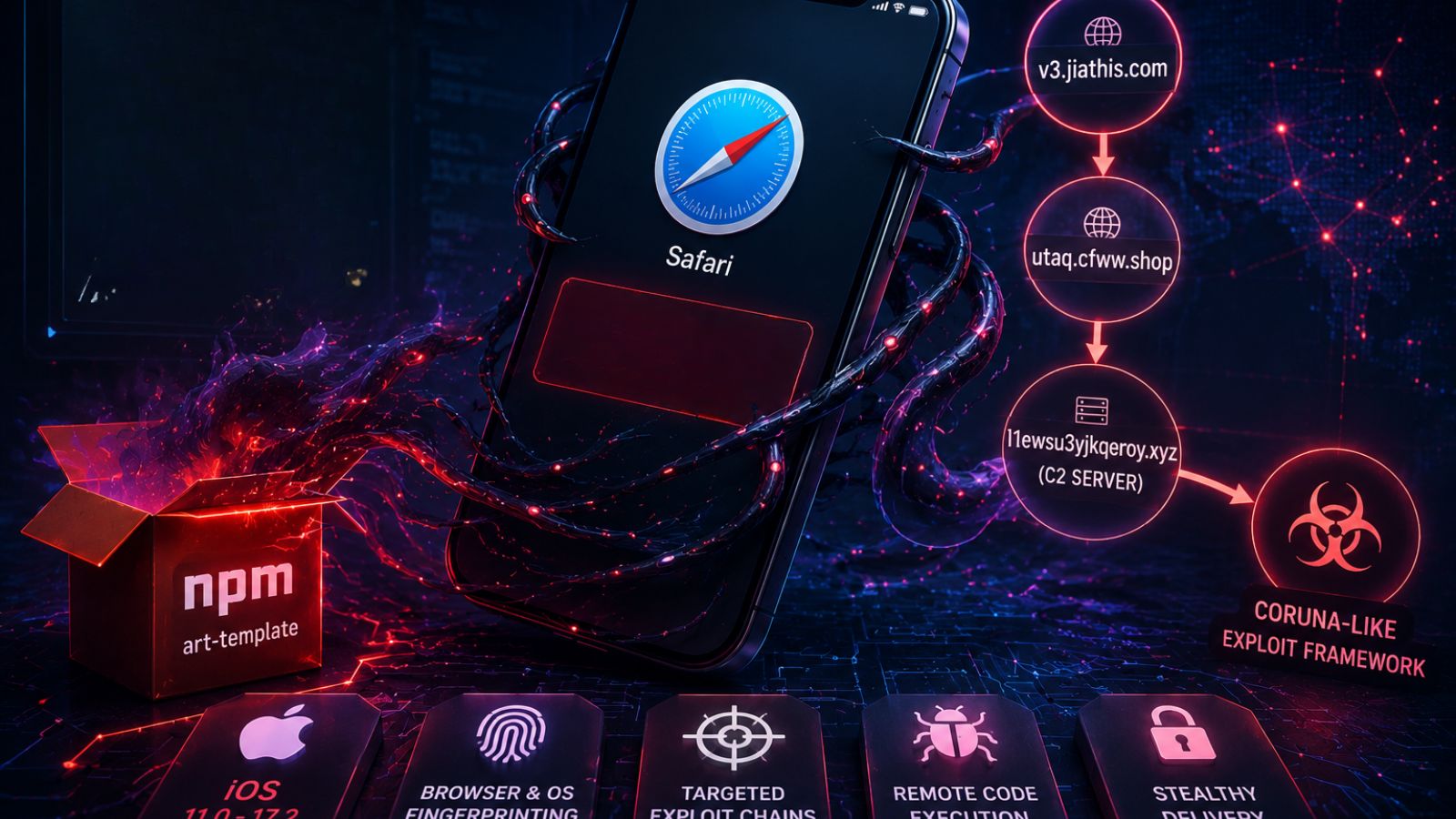
An October 2025 Cisco Talos report highlighted that Qilin's evolving methods include leveraging VPN credentials that were exposed on the dark web. One month later, the City of Santa Paula was hit by a disruptive ransomware attack claimed by Qilin.
In February, APT28 (Fancy Bear, Forest Blizzard), a Russian state-sponsored threat group linked to the Russian GRU’s 85th Main Special Service Center (Unit 26165), was reported to deploy macro malware in a browser-based exfiltration operation targeting Europe.
In other recent news, Germany revealed the name of the alleged REvil Ransomware and GandCrab leader Daniil Maksimovich Shchukin (UNKN).