Medusa Ransomware Group Exploits Zero-Day Vulnerabilities Within 24 Hours of the Breach
- Rapid attack execution: The Medusa ransomware group transitions from initial network access to data exfiltration and payload deployment within 24 hours.
- Zero-days targeted: Notably, the actors actively exploited CVE-2026-23760 in SmarterMail and CVE-2025-10035 in GoAnywhere MFT days before public disclosure.
- Cybersecurity risks escalate: These accelerated attacks heavily impact critical infrastructure, including healthcare facilities and municipal governments across the U.S.
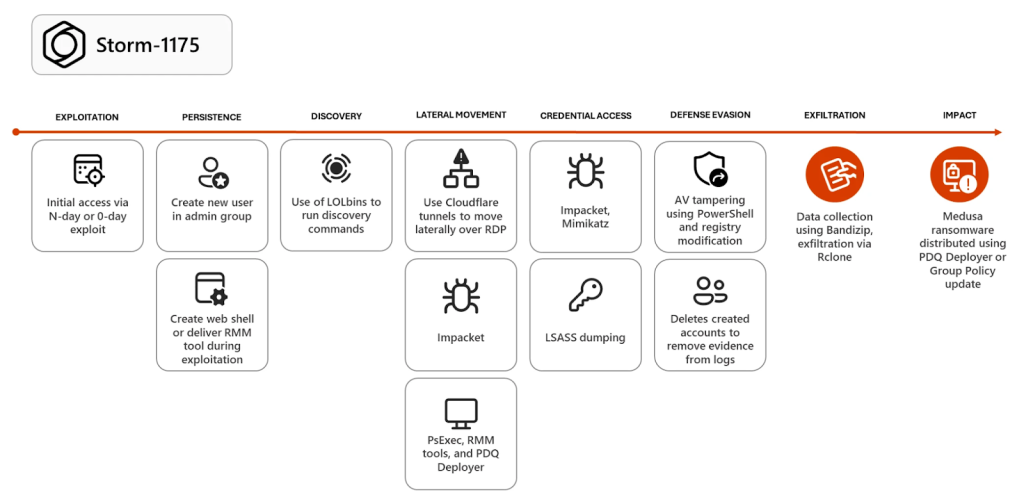
Recent analysis by Microsoft cybersecurity researchers reveals a concerning escalation in the operational tempo of the Storm-1175 group, known for Medusa ransomware deployment. This highly proficient threat syndicate is actively weaponizing zero-day vulnerabilities to compromise web-facing perimeters, drastically reducing the defense window for enterprise network administrators.
Exploiting Zero-Day Vulnerabilities
The Medusa ransomware group demonstrates a sophisticated ability to identify and exploit vulnerabilities days before patches are widely available. Remarkably, this group can execute full data exfiltration and deploy encryption payloads within 24 hours of the initial breach, Microsoft has warned.
Upon gaining initial access, the attackers immediately create unauthorized user accounts to ensure persistence. They subsequently leverage legitimate remote management software, including ConnectWise ScreenConnect, AnyDesk, and SimpleHelp, to navigate the compromised environment.
Since 2023, Microsoft Threat Intelligence has observed exploitation of over 16 vulnerabilities, including:
- CVE-2023-21529 (Microsoft Exchange)
- CVE-2023-27351 and CVE-2023-27350 (Papercut)
- CVE-2023-46805 and CVE-2024-21887 (Ivanti Connect Secure and Policy Secure)
- CVE-2024-1709 and CVE-2024-1708 (ConnectWise ScreenConnect)
- CVE-2024-27198 and CVE-2024-27199 (JetBrains TeamCity)
- CVE-2024-57726, CVE-2024-57727, and CVE-2024-57728 (SimpleHelp)
- CVE‑2025‑31161 (CrushFTP)
- CVE-2025-10035 (GoAnywhere MFT)
- CVE-2025-52691 and CVE-2026-23760 (SmarterMail)
- CVE-2026-1731 (BeyondTrust)
Escalating Global Cybersecurity Risks
The Medusa syndicate, believed to operate out of Russia due to its avoidance of Commonwealth of Independent States targets and its use of Cyrillic script, systematically targets critical infrastructure.
To mitigate these advanced threats, organizations must maintain rigorous visibility over their internet-facing assets and implement strict access controls to prevent rapid lateral movement within their networks.
Recent ransomware attacks attributed to this group have crippled significant entities, including the University of Mississippi Medical Center and Passaic County in New Jersey, as well as other healthcare institutions. Last month, a Bell Ambulance breach that exposed data of almost 240,000 patients was claimed by Medusa.