GitHub Phishing Campaign Targets Developers with Fake VS Code Alerts that Urge the Patching of Fabricated CVEs
- Coordinated spam attack: A massive GitHub phishing campaign utilizes repository Discussions to target developers with fraudulent software security warnings.
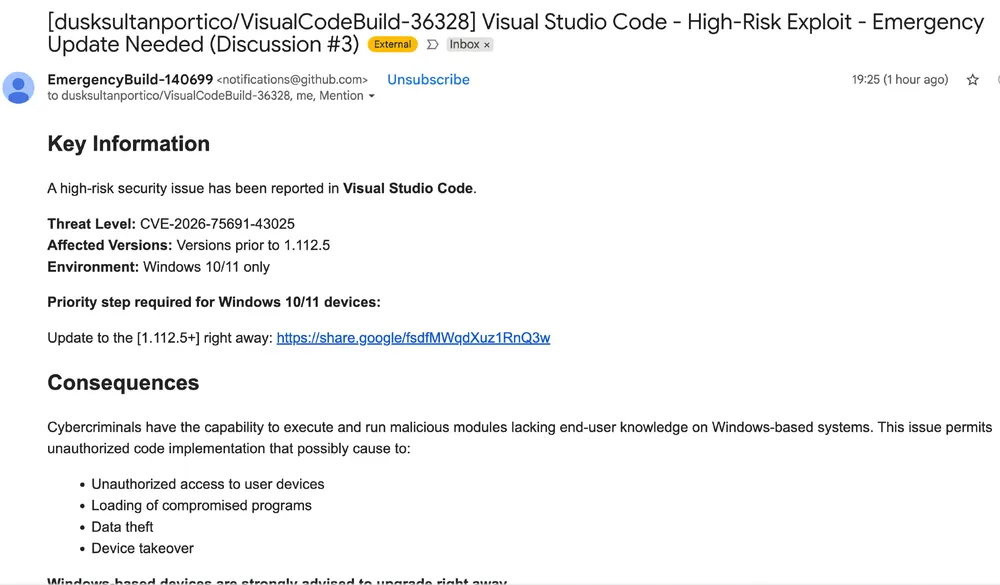
- Fake VS Code alerts: Attackers fabricate critical vulnerability warnings for Visual Studio Code, urging users to download malicious updates via external links.
- Malware distribution tactics: The ongoing attack on GitHub users employs tactics consistent with advanced traffic distribution systems.
A GitHub phishing campaign deploys fake Visual Studio Code (VSC) alerts to deceive users into accessing compromised network domains. The attackers are actively targeting software engineers by exploiting the platform's native collaborative infrastructure, generating thousands of fraudulent posts within GitHub Discussions.
By manipulating email notifications, these malicious advisories are delivered directly to developers' email inboxes, artificially establishing legitimacy and operational urgency.
Patching Fake CVEs
The attack mimics credible security advisories by fabricating CVE designations and claiming that severe vulnerabilities require immediate patching, similar to ClickFix campaigns. The fake VS Code alerts instruct users to download an updated software version from external file-sharing services (such as Google Drive), bypassing official distribution channels, according to Socket.
Variations of the same template include messages such as:
- “Visual Studio Code – Severe Vulnerability – Immediate Update Required”
- “Critical Exploit – Urgent Action Needed”
- “Severe Threat – Update Immediately”
When users interact with these links, they initiate a multi-stage redirection sequence that uses Google’s “share.google” endpoint as an initial distribution layer. The Google endpoint behaves differently depending on whether the request includes a Google cookie.
Valid sessions are redirected to an attacker-controlled command-and-control (C2) server, executing obfuscated JavaScript to harvest browser fingerprint data, including timezone, operating system platform, and automation signals without deploying a visible second-stage payload – consistent with a traffic distribution system (TDS).
Developer Cybersecurity
This incident represents a significant escalation in malware distribution techniques, as threat actors weaponize trusted repository environments. Developers should treat GitHub Discussions with caution, especially when they include:
- External download links
- Unknown or unverifiable CVEs
- Urgent instructions to install software
- Mass tagging of unrelated users
- Recently created or unfamiliar accounts posting advisories
Earlier this year, Evelyn Stealer targeted software developers via VSC extensions. In December 2025, a WebRAT GitHub campaign targeted researchers with repositories containing fake PoC exploits for legitimate vulnerabilities, and, one month earlier, TigerJack malware infected over 17,000 developers via malicious VSC extensions.