Palo Alto Networks Phishing Scam Targets Professionals
- Recruitment fraud: Attackers impersonate Palo Alto Networks talent acquisition staff to target senior-level professionals with highly personalized social engineering tactics.
- Manufactured crisis: The phishing campaign falsely claims a candidate's resume failed automated tracking system requirements to create artificial urgency.
- Financial exploitation: Threat actors charge victims up to $800 for fraudulent resume optimization services, representing a severe escalation in cybersecurity threats.
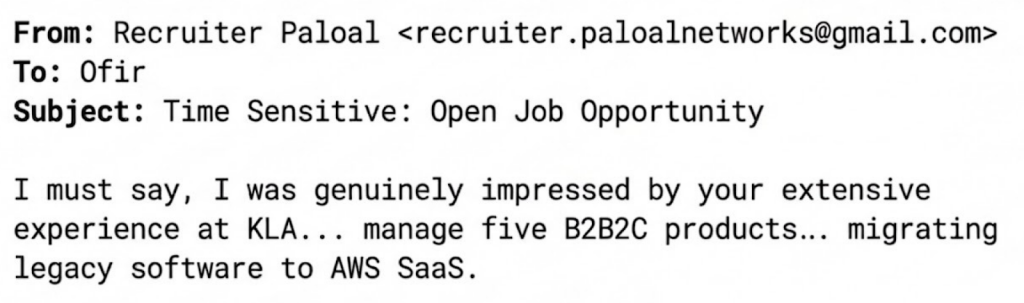
A Palo Alto Networks phishing scam is actively targeting senior industry professionals. Threat actors are impersonating official Palo Alto talent acquisition representatives to execute advanced recruitment fraud. By leveraging scraped data from professional networking platforms such as LinkedIn, the attackers craft highly personalized lures designed to exploit ambitious candidates.
Executing the Phishing Campaign
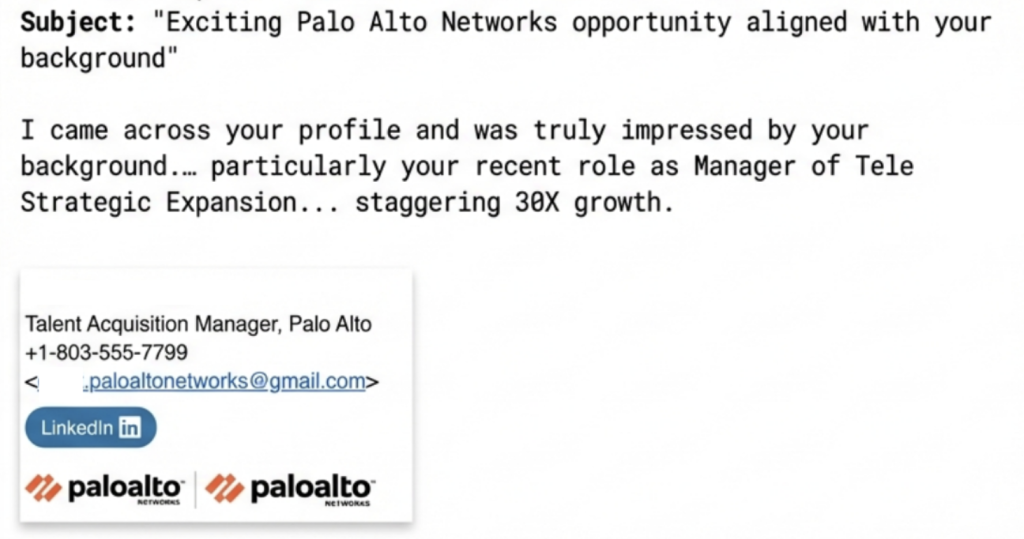
The core of this Palo Alto phishing campaign relies on manufacturing a bureaucratic barrier within the hiring process. Attackers initiate contact using seemingly legitimate email domains and legitimate corporate branding to establish credibility.
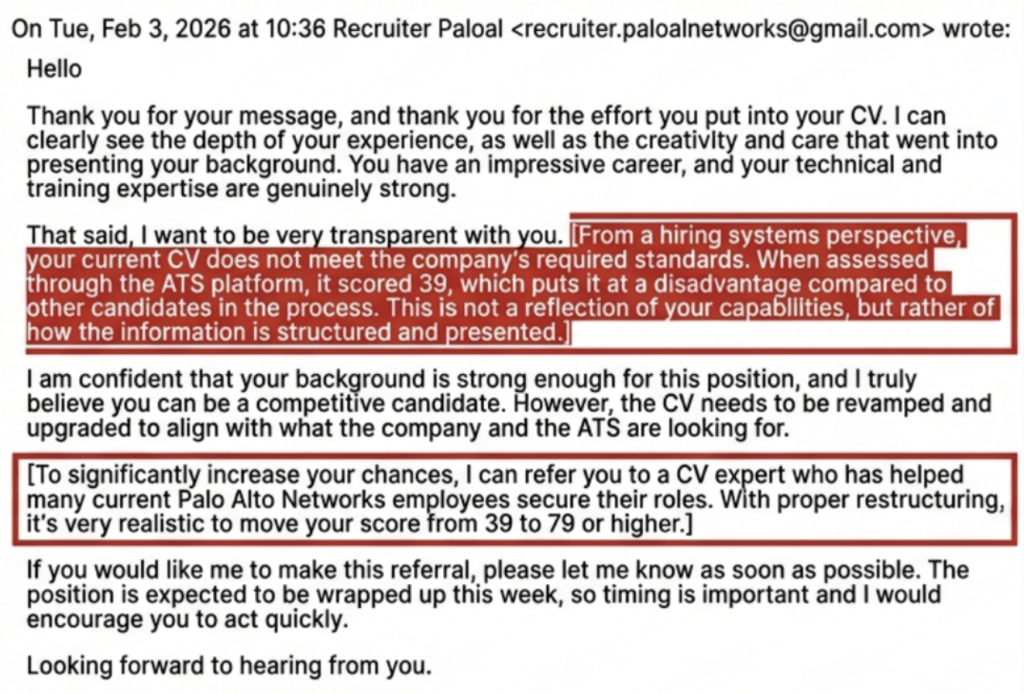
Once they build rapport, the threat actors inform the candidate that their curriculum vitae failed to meet the mandatory Applicant Tracking System (ATS) requirements, according to Palo Alto.
This psychological manipulation creates a false sense of urgency, pressuring the victim to resolve the technical issue quickly to secure the purported employment opportunity.
After establishing the fake ATS crisis, the fraudulent recruiter introduces a third-party expert to bypass the automated filters. The attackers demand direct payments ranging from $400 for basic alignment to $800 for an alleged comprehensive executive rewrite.
Analyzing the Cybersecurity Threats
This phishing campaign impersonating Palo Alto reflects a shift toward complex social engineering, in which adversaries weaponize standard corporate hiring procedures for immediate financial gain. Legitimate enterprises never require monetary payment or optimization fees during the talent acquisition process.
To mitigate this risk, security administrators advise professionals to:
- Verify the sender's domain.
- Request an official platform to continue the conversation.
- Zero-payment policy.
- Cross-reference the recruiter.
- Avoid suspicious attachments.
On the other side, North Korean operatives impersonate real professionals on LinkedIn. Earlier this month, Russian cybercriminals were seen targeting Signal and WhatsApp accounts of high-value individuals in a large-scale phishing operation.