Aqua Security Works with Sygnia to Remediate Trivy Supply Chain Attack Leveraging CI/CD Vulnerabilities that Expanded to Compromised Docker Images
- Credential compromise: A Trivy supply chain attack leveraged compromised GitHub Action tokens to execute a sophisticated open-source security breach.
- Malicious release: Threat actors modified existing version tags and published a malicious release of Trivy v0.69.4 to extract sensitive data.
- Enterprise isolation: Aqua Security confirmed its commercial products remain completely unaffected by the CI/CD pipeline compromise impacting open-source tools.
Aqua Security engaged the global incident response firm Sygnia to conduct forensic analysis and validate remediation efforts regarding the recent sophisticated Trivy supply chain attack that compromised widely used GitHub Actions environments. Threat actors exploited a misconfiguration of the open-source security scanner to extract privileged access tokens, enabling them to infiltrate repository automation and deployment processes to steal sensitive developer data.
Executing the Malicious Release
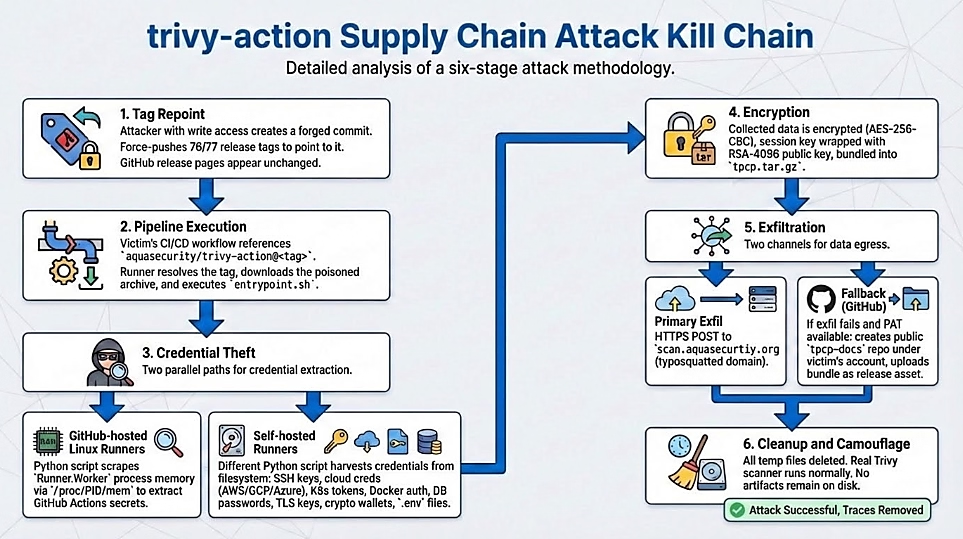
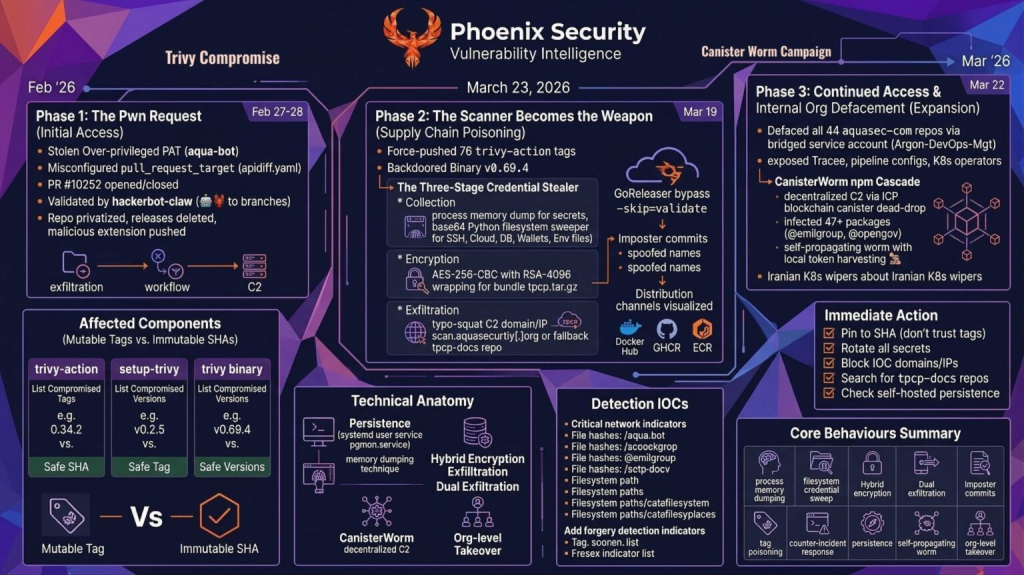
The attackers employed a stealthy approach as part of a six-stage attack methodology that started late February 2026. They force-pushed malicious commits over existing, trusted version tags within the aquasecurity/trivy-action and setup-trivy repositories.
The compromised aqua-bot service account triggered the automated distribution of a malicious release designated as Trivy v0.69.4 on March 19, 2026, at around 17:43 UTC. The compromised workflows executed normally without alerting developers to the underlying code changes.
During this silent execution, the malicious payload actively collected and exfiltrated sensitive information. Targeted data included API tokens, cloud credentials (AWS, GCP, Azure), SSH keys, Kubernetes tokens, Docker configuration files, Git credentials, and other secrets in CI/CD systems. Phoenix Security also noted the campaign debuted around February 26, 2026.
On March 22, Socket's threat research team identified additional compromised Trivy artifacts published to Docker Hub, following the GitHub Actions compromise of the aquasecurity/trivy-action repository, which Paul McCarty disclosed on the same day.
Socket noted that newly published Trivy Docker images 0.69.4, 0.69.5, and 0.69.6 were pushed to Docker Hub without corresponding GitHub releases and contained infostealer IOCs associated with the same TeamPCP observed earlier in this campaign.
The following open source components were affected and should be treated as potentially compromised:
- Trivy binary release: v0.69.4
- GitHub Action aquasecurity/trivy-action: 76 of 77 version tags force-pushed to malicious commits (only v0.35.0 was unaffected, protected by GitHub’s immutable releases feature)
- GitHub Action aquasecurity/setup-trivy: multiple version tags compromised
- Any CI/CD workflow that referenced these actions via a mutable version tag, or that downloaded:
- trivy v0.69.4, between approximately 18:22 UTC and 21:42 UTC on March 19, 2026,
- trivy-action v0.69.4, between approximately 17:43UTC UTC on March 19, 2026, and 05:40 UTC on March 20, 2026,
- setup-trivy, between approximately 17:43 UTC and 21:44 UTC on March 19, 2026.
The latest update stated that the company's commercial enterprise products operate on an architecturally isolated platform and remain unaffected by the breach. “The malicious Trivy v0.69.4 release was never incorporated into the commercial environment, and the GitHub-based attack path does not apply to the commercial build system,” the company said.
Attack Timeline
Here is the Trivy attack timeline, according to Aqua Security:
- Late February 2026: Attackers exploited a misconfiguration in Trivy’s GitHub Actions environment, extracting a privileged access token and establishing a foothold in repository automation and release processes.
- March 1, 2026: The Trivy team disclosed the earlier incident and executed credential rotation. Subsequent investigation revealed the rotation was not fully comprehensive, allowing the threat actor to retain residual access via still-valid credentials.
- March 19, 2026 (~17:43 UTC): The attacker force-pushed 76 of 77 version tags in the aquasecurity/trivy-action repository and all 7 tags in aquasecurity/setup-trivy, redirecting trusted references to malicious commits. Simultaneously, the compromised aqua-bot service account triggered release automation to publish a malicious Trivy binary designated v0.69.4.
- March 19, 2026 (~20:38 UTC): The Trivy team identified and contained the attack, removing malicious artifacts from distribution channels.
- March 20, 2026: Safe versions, user guidance, and indicators of compromise published for defenders.
Mitigating the CI/CD Pipeline Compromise
The Trivy maintenance team immediately executed comprehensive containment protocols. Aqua Security deleted all malicious artifacts across GitHub Releases, Docker Hub, GHCR, and ECR, locked down automated actions, service accounts, and tokens, and repointed hijacked version tags to verified, safe commits.
Aqua Security’s commercial products were not impacted by this incident, including Trivy as delivered within the Aqua Platform. However, users of open source Trivy components outside the Aqua Platform should follow the remediation steps. Security experts recommend open-source users:
- Audit Trivy versions and GitHub action references,
- Rotate all potentially exposed secrets immediately,
- Look for repositories named tpcp-docs in your GitHub organization,
- Review your network firewalls, SIEM, and GitHub audit logs for the indicators of compromise,
- Pin GitHub Actions to immutable commit hashes to prevent future exploitation.
The latest Trivy supply chain attack follows a separate compromise affecting the Aqua Trivy VS Code extension distributed via OpenVSX, in which injected code attempted to exploit local AI coding agents. Aqua Security is an Israeli-American cloud security company founded in 2015.