Crunchyroll Data Breach Exposes Customer Information via Telus, Reports Say
- Third-party vulnerability: An unidentified threat actor exploited a compromised employee account at an outsourcing partner to infiltrate the platform's infrastructure.
- Substantial data exfiltration: The unauthorized intrusion resulted in the extraction of approximately 100 GB of sensitive corporate and user data.
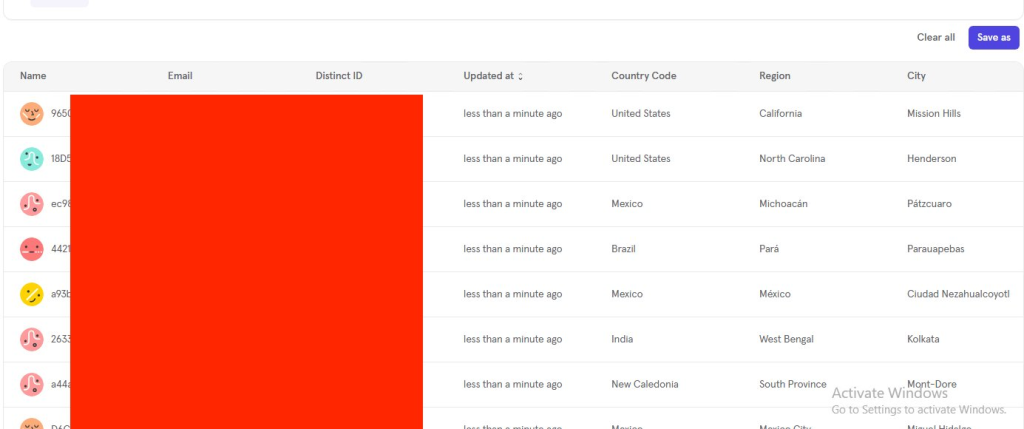
- Ongoing assessment: The alleged customer data compromise purportedly encompasses analytics repositories and ticketing system databases.
Crunchyroll was reportedly breached by an unnamed threat actor that carried out large-scale data exfiltration via a compromised account of its outsourcing partner, Telus. This cybersecurity incident resulted in the alleged exfiltration of ticketing system data and approximately 100 GB of personally identifiable user analytics data.
Technical Analysis of the Security Breach
According to International Cyber Digest, the compromised dataset encompasses comprehensive subscriber analytics, backend ticketing infrastructure records, and personally identifiable information (PII) repositories:
- IP addresses,
- Email addresses,
- Credit card details.
Reports say the adversaries compromised employee credentials belonging to the authorized outsourcing partner that maintained privileged access to Crunchyroll's systems.
Data Compromise Scope
This Crunchyroll data compromise story is still developing and maintains a preliminary verification status with an assigned ESIX score of 5.02. The data breach happened on March 12, 2026, and Crunchyroll revoked the unauthorized access after 24 hours, the hackers reportedly told International Cyber Digest.
Canadian telecommunications and business services firm Telus on March 16 confirmed a cybersecurity incident involving unauthorized access to some of its systems, with ShinyHunters claiming to have stolen at least 700 terabytes in a message to Reuters.
The gang also shared samples that suggested at least two dozen companies were affected and included PII, call data and recordings, FBI background check information, and source code spanning multiple business divisions. Reports say the Telus breach started at a third-party itself, Salesforce, as ShinyHunters reportedly found Google Cloud Platform credentials tied to Telus Digital.
Organizations must establish stringent access governance protocols and deploy continuous monitoring capabilities across external vendor ecosystems to mitigate supply chain attack vectors. Users should change their Crunchyroll passwords.