Sophisticated Phishing Campaign Exploits Trusted Cisco Domains, Impersonates JPMorgan, Targeting European Security Vendor
- Attack Chain Complexity: The Cisco phishing campaign utilizes a sophisticated multi-chain redirect attack to successfully bypass enterprise security filters.
- Trusted Infrastructure Exploited: Threat actors leverage legitimate services, including Cisco Secure Web, to systematically obscure their malicious phishing destinations.
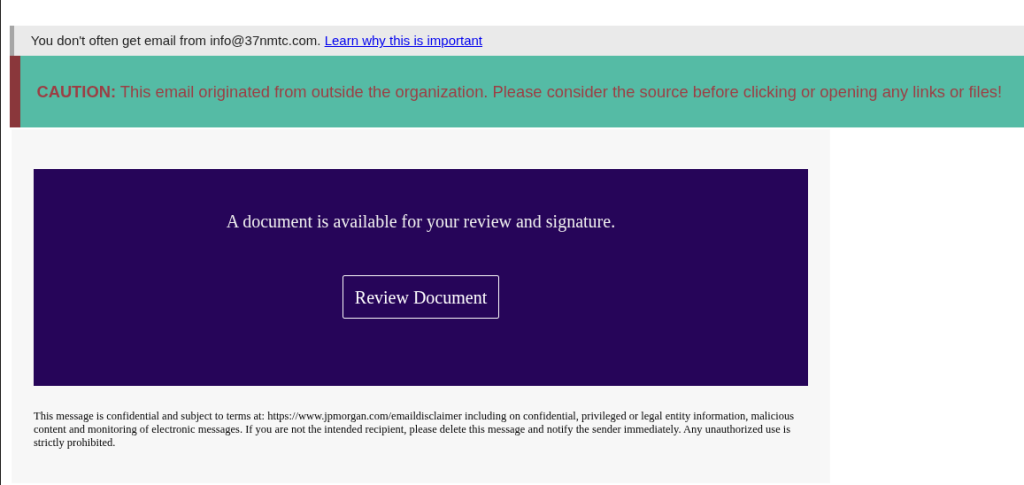
- Brand Impersonation: The initial lures were fake JPMorgan emails that suggested a document needed to be signed.
A highly sophisticated Cisco phishing campaign engineered to evade standard email security gateways begins with a deceptive email impersonating JPMorgan, alleging that a PDF document needs to be signed. The attack chains Cisco Secure, Nylas, re-registered domain redirects, and Cloudflare validation to ultimately steal credentials via a fake Microsoft login page.
By utilizing valid DomainKeys Identified Mail (DKIM) signatures from compromised infrastructure, the malicious messages successfully pass Domain-based Message Authentication, Reporting, and Conformance (DMARC) checks. This configuration ensures the email appears completely authenticated to modern mail protection systems.
Multi-Chain Redirect Attack
The multi-chain redirect phishing campaign fronting as Cisco that targeted an unnamed European security vendor was identified by threat intelligence analysts at Outpost24 on March 13, 2026. When a target clicked the embedded document link, the request was routed initially through the legitimate secure-web.cisco.com infrastructure.
Subsequently, the traffic traverses the Nylas email API platform, which provides services such as email synchronization, tracking, and automation for developers, was redirected through a compromised third-party server, and bounced across a specifically repurposed domain.
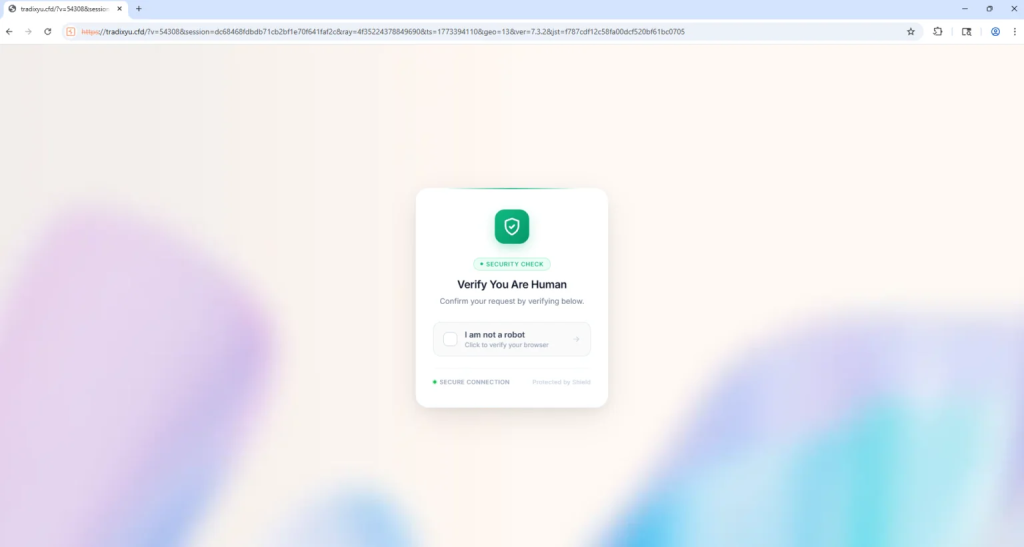
By chaining redirects through these widely trusted services, the attackers systematically prevent automated security scanners and reputation-based filters from blocking the malicious URLs. After a decoy PDF endpoint, the next redirect is to a re-registered domain that had existed for several years, first registered in 2017 by a Chinese entity.
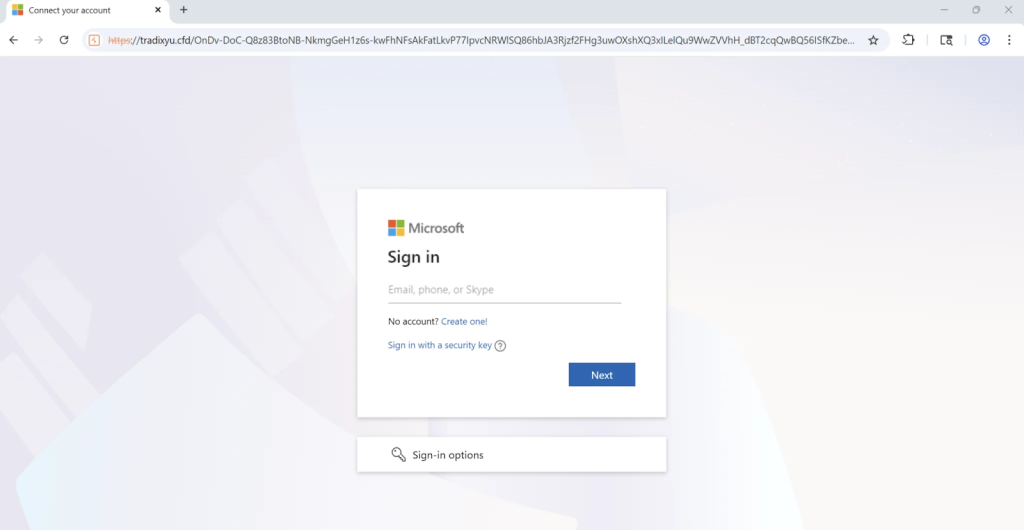
Lastly, the attackers enforce an anti-bot validation page hosted via Cloudflare, blocking automated analysis tools and sandbox environments from inspecting the site. Once validated, the system redirects the user to a fake Microsoft 365 login page designed to harvest credentials, likely leveraging Kratos, a relatively new Phishing-as-a-Service (PhaaS) kit.
Mitigation
This persistent threat demonstrates that standard password authentication provides inadequate defense against modern social engineering. To neutralize these vulnerabilities, organizations must implement comprehensive cybersecurity measures, such as deploying device-bound Zero Trust access.
“The idea that a password, or even a password plus a standard multi-factor authentication (MFA) prompt, is adequate defense against a persistent, well-resourced adversary is increasingly difficult to sustain,” said Martin Jartelius, Outpost24 Product Director.
Sneaky2FA phishing kit adopted Browser-in-the-Browser tactics in November 2025 to steal credentials via fake Microsoft login pages. In July 2025, aviation executives were targeted in a BEC phishing scam leveraging fake Microsoft 365 login pages.