Divine Skins Data Breach Exposes Data of Over 105,000 League of Legends Custom Skins Users, Anonymous Allegedly Behind It
- Data Compromise: The Divine Skins data breach exposed the usernames, email addresses, and purchase histories of registered platform users.
- Skins Deletion: An unauthorized third party breached the system infrastructure, subsequently deleting all League of Legends custom skins from the database.
- Incident Disclosure: Administrators confirmed the cybersecurity incident via Discord, and Have I Been Pwned recently added approximately 105,800 unique addresses.
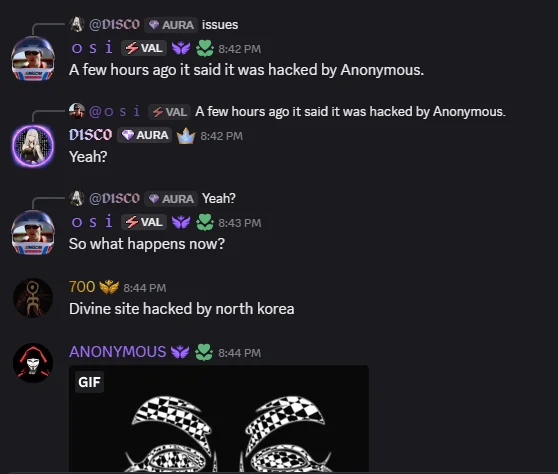
League of Legends custom skins provider, Divine Skins, suffered a targeted network intrusion on March 13, 2026. Service administrators formally disclosed the Divine Skins data breach through their official Discord server. On March 15, 2026, the stolen database records were officially aggregated in the Have I Been Pwned (HIBP) data breach notification service repository. Meanwhile, rumours say Anonymous orchestrated the intrusion.
LOL User Data Exposed
The Divine Skins incident confirmed that an unauthorized threat actor had gained access to part of its backend systems, which exposed highly sensitive user data from 105,814 individual accounts to unauthorized parties. Threat actors successfully exfiltrated critical account details, specifically targeting:
- Email addresses,
- Associated usernames,
- User purchases.
Third-party gaming modification platforms remain highly lucrative targets for cybercriminals because they process transactional data alongside standard login credentials. Best practices suggest immediate password resets across all external services that use identical credentials, and implementing strict monitoring for anomalous email communications.
The intrusion, which was disclosed via the service’s Discord server, also deleted all custom skin assets stored in the service's database. User reports on Reddit rumours include that Divine was hacked by Anonymous and North Korea.
Implications for Platform Users
Third-party gaming modification platforms remain highly lucrative targets for cybercriminals because they process transactional data alongside standard login credentials. Best practices suggest immediate password resets across all external services that use identical credentials, and implementing strict monitoring for anomalous email communications.
In September 2025, a cancer patient’s $32,000 treatment fund was stolen via a fake Steam game. Earlier last year, a Path of Exile 2 breach led to hacked player accounts and in-game item theft, and Valve removed a Trojan-infested game from Steam, advising users to reformat their systems.