XWorm RAT Dominates the Malware-as-a-Service Landscape with 174% Increase in Detections
- Rapid threat growth: XWorm RAT has surged to become the third most prevalent global threat, with enterprise detections up 174% over the past year.
- Stealth techniques used: The malware employs Living-off-the-Land tactics, abusing legitimate Microsoft utilities to execute malicious payloads in-memory.
- Exploit-driven attacks: Operating within a MaaS model, XWorm exploits critical path-traversal vulnerabilities to bypass traditional security defenses and facilitate data exfiltration.
XWorm RAT recently became the third most-detected global threat, as this highly modular tool is aggressively outpacing legacy remote access trojans (RATs), cybersecurity researchers say. By offering advanced enterprise-scale disruption capabilities at a low acquisition cost, XWorm entirely redefines the modern malware-as-a-service (MaaS) marketplace.
In-Memory Execution and Evasion Tactics
XWorm operates as a highly lightweight, modular, and stealthy malware, a recent Trellix analysis revealed. In 2025, XWorm detections were 4.3x higher than the year before, now accounting for a significant share of the 2 million+ sandbox sessions analyzed annually by security researchers.
XWorm saw a staggering 174% surge in detections over the last year, while legacy tools like Remcos and AgentTesla dropped to the 7th and 10th place, respectively, Trellix said, citing the ANY.RUN 2025 Threat Report.
Recent infection chains weaponize ZIP/RAR path-traversal vulnerabilities, such as the WinRAR CVE-2025-8088 exploit, frequently delivered through platforms like Discord via deceptive archives.
Upon initial access, the malware initiates a complex, multi-stage deployment utilizing "Living off the Land" (LOTL) techniques. The primary mechanism abuses trusted system binaries, specifically Aspnet_compiler.exe, through reflective DLL injection. By allocating space within the memory of a legitimate process, the core payload runs entirely without touching the disk, effectively neutralizing standard signature-reliant endpoint protections.
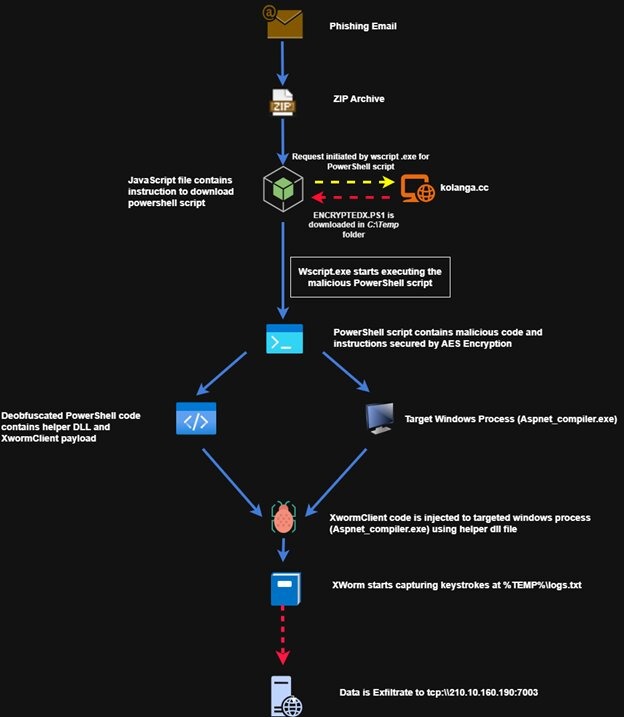
Trellix analysis mentions a 7-stage execution flow:
- Initial access: Phishing email with a ZIP attachment, such as "MFEQuotation Work request for NCSOCSO.zip".
- The JavaScript dropper: Opening the enclosed .JS file triggers wscript.exe and attempts to connect to a remote server (e.g., kolanga[.]cc).
- Encrypted PowerShell staging: The downloaded PowerShell script, which serves as a secure container, has a large block of encrypted data and a hardcoded AES decryption key.
- LOTL: The script executes with the -nop and -ep bypass switches to evade safety checks and launches the trusted Microsoft application Aspnet_compiler.exe.
- In-Memory execution: The script performs Reflective DLL Injection to insert the XWormClient Payload.
- Data capture: The malware captures every keystroke and saves it to a hidden log file in the %TEMP% folder.
- Data exfiltration: At regular intervals, the encrypted logs are sent to the attacker's command-and-control (C2) server.
Escalating Cybersecurity Threats
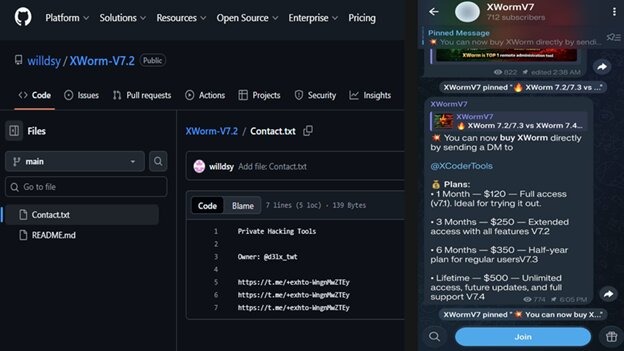
The capabilities of this RAT include password harvesting, unauthorized process modifications, coordinated DDoS attacks, and monitoring files, registry, screen, web browser tabs, webcams, and microphones. Because XWorm successfully combines advanced persistent threat (APT) deception tactics with extreme commercial accessibility (averaging a $500 lifetime subscription), network defenders must:
- transition toward proactive, behavior-based security postures.
- Identify unauthorized process hollowing.
- Accelerate vulnerability patching.
Earlier this year, the ANY.RUN report outlined that Lumma and XWorm led malware family rankings, and CloudSek reported a trojanized version of the XWorm RAT builder spread through GitHub, Telegram, and file-sharing platforms to compromise over 18,000 devices globally.
In 2025, the new Brazilian malware Caminho Loader employed steganography in an October global campaign deploying Remcos RAT, XWorm, and Katz Stealer, and UAC-0173 deployed DCRAT and XWORM Stealer against Ukrainian notaries in February.