WPML WordPress Plugin Site Hack and Warning Spam
- WPML users received an alarming warning message, urging them to ask for their money back.
- The hacker claims he is an irritated customer, but WPML explains it’s a former employee.
- WPML users must now reset their passwords on the platform, as the intruder has access on their account credentials.
This weekend, users of the WPML plugin for the WordPress platform have received emails that warned them about the safety and security risks that come with using the particular piece of software. The message was sent through a legit WPML address, while the official website of the plugin was compromised as well. WPML is used by more than half a million people, helping them add multilingual support in their website, so the people who received these warning messages are quite a lot.
The email message contained the following among others: “WPML came with a bunch of ridiculous security holes which allowed the most important two of my websites to be hacked. I’m able to write this here because of the very same WPML flaws are present on wpml.org too. Make backups do not store sensitive information in the database, use only the features that you really need, or ask for your money back.”
https://twitter.com/retlehs/status/1086745752930463745
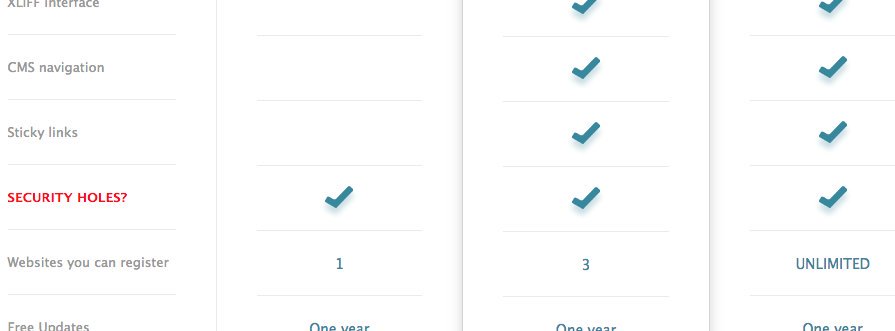
The hack on the website includes the same message published as a blog post, and a particularly funny addition of “security holes” in the features summary, ticked on all payment plan tier boxes. While the person behind this act claims to be a fed-up dissatisfied customer that has repeatedly warned the WPML team of the vulnerabilities and got ignored, the official explanation by the WPML developers is that it’s a former employee who left a backdoor on the platform and used it for retribution for his dismissal.
Image Credits: Donnacha MacGloinn
WPML explains that the hack did not take advantage of any exploits in the plugin or the platform, but instead, it relied on the use of an old SSH password. This means that no customer payment information was compromised, but a user password reset is still the suggested practice now until the developers update their users' community with a more complete summary in the upcoming week. The four main clarification points given by the team are the following:
- WPML plugin running on your site does not contain this exploit.
- Your payment information was not compromised (we don’t store it).
- The intruder does have your name and email and might have access to your account at WPML.org.
- The intruder indeed stole the sitekeys, but they are of no use. The sitekeys allow your site to get updates from wpml.org. The intruder cannot push any changes to your site using these keys.
Are you using WPML on your websites? Have you received the above warning message? Let us know in the comments below, and don’t forget to subscribe on our socials on Facebook and Twitter, so you never miss out on fresh tech news.