VanHelsing Ransomware-as-a-Service Emerges as a Significant Cybersecurity Threat
- A new RaaS operation named VanHelsing rose fast this month, aggressively targeting several victims.
- It has multi-platform compatibility and exploits Server Message Block services to propagate across network drives and shared systems.
- Cybersecurity experts say the model shows partial feature implementation and has file extension issues.
VanHelsingRaaS (Ransomware-as-a-Service) launched on March 7, 2025, providing a structured platform for affiliates to launch ransomware attacks efficiently, significantly lowering the barrier of entry into the ransomware market.
Since its launch, VanHelsingRaaS has infected at least three known victims in under two weeks. Investigations by Check Point Research (CPR) highlight its aggressive and fast-paced evolution, with two ransomware variants discovered just five days apart.
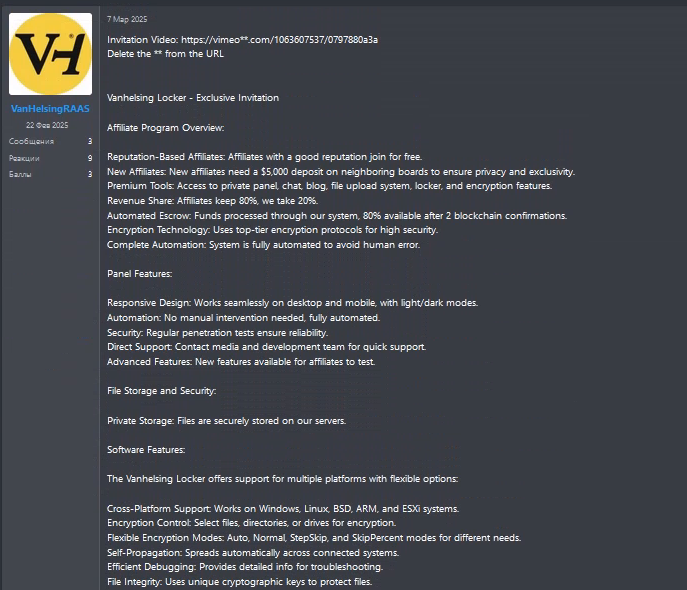
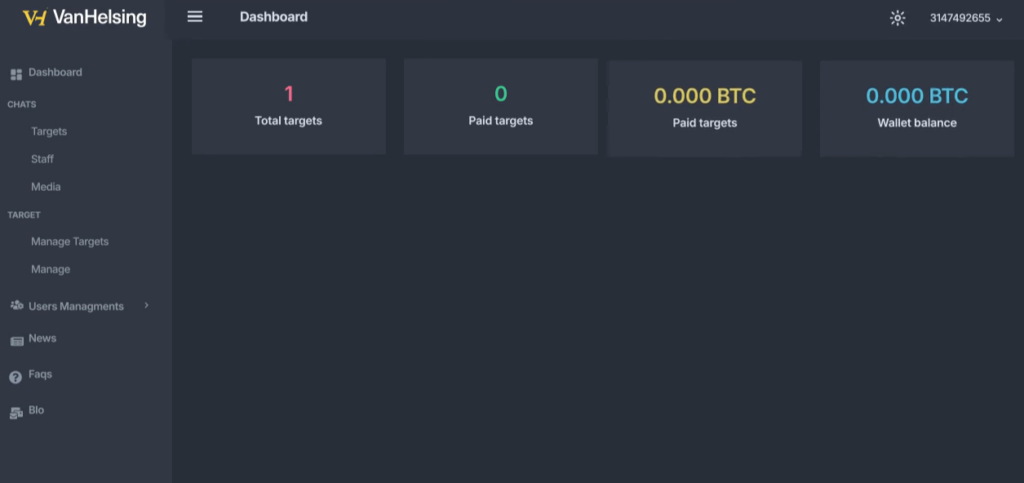
VanHelsingRaaS employs a straightforward affiliate model. Participants pay an initial $5,000 deposit to join (waived for experienced affiliates). The service offers an 80/20 revenue split, with 80% of ransom payments going to the affiliated attackers and 20% retained by the core operators.
The program provides affiliates with a user-friendly control panel to execute attacks, alongside versatile ransomware "locker" software. This locker targets not just Windows systems but also additional platforms like Linux, BSD, ARM, and ESXi environments, making VanHelsing particularly dangerous.
During negotiations, affiliates typically demand ransom payments of $500,000 in Bitcoin. However, VanHelsing enforces a notable limitation. Affiliates are prohibited from encrypting systems in Commonwealth of Independent States (CIS) countries, a common restriction observed in ransomware operations associated with Eastern Europe.
The newer variant introduced enhanced features via additional command-line arguments to customize encryption behaviors and further streamline attack execution.
The VanHelsing ransomware is written in C++ and includes advanced capabilities such as:
- Command-line Configuration: Fine-tunes encryption processes with commands to target specific drives, directories, or files and supports flags to evade detection, limit local file encryption, or prioritize execution.
- Silent Encryption Mode: Hides activity during encryption to evade security tools and encrypts files first and changes file extensions later, further masking its activities.
- Multi-Platform Compatibility: Targets not just systems running Windows, but also Linux and VMware ESXi servers, broadening the attack surface.
- Integrated SMB Spread: Attempts to propagate across network drives and shared systems by exploiting Server Message Block (SMB) services.
- Shadow Copy Deletion: Deletes Windows Volume Shadow Copies, leaving victims unable to restore their data through system backups.
Despite its cutting-edge features, the ransomware contains some operational flaws. The actual encrypted file extension, .vanhelsing, does not align with its expected .vanlocker extension, disrupting file association functions. Certain functionalities, such as propagating through VMware vCenter servers, remain incomplete placeholders.
VanHelsingRaaS achieves what many similar platforms have aimed for – but at unparalleled speed and scale.