Traffic Violation Scams Targeting US Residents Adopt QR Code Phishing Tactics
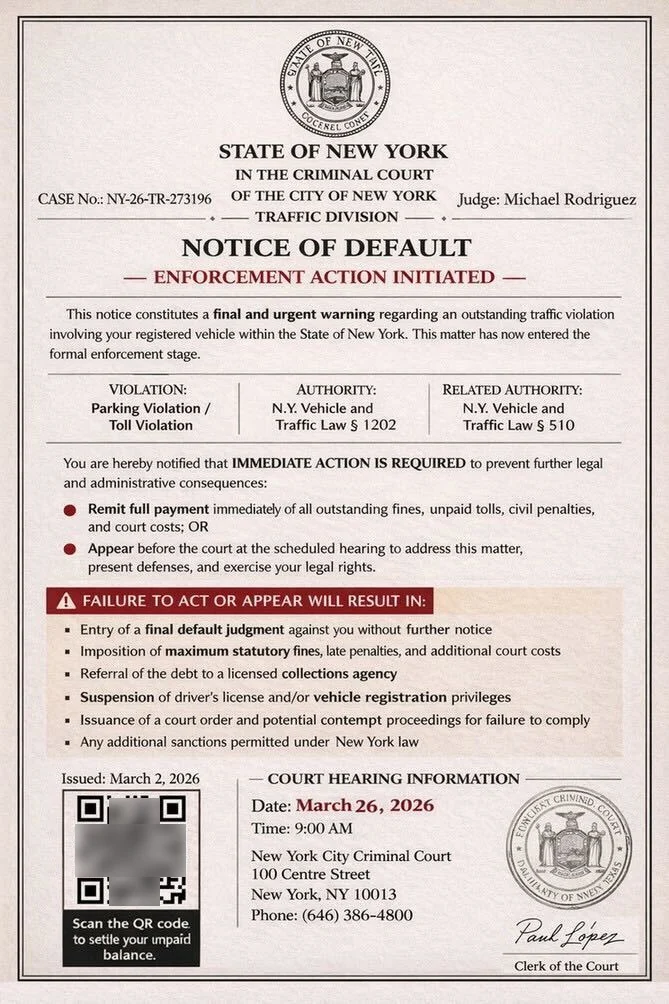
- Fraudulent notices: Threat actors deploy SMS-based social engineering campaigns impersonating state judicial systems, alleging outstanding traffic violations requiring immediate payment.
- QR code attack: These phishing operations use fabricated official documentation with embedded QR codes instead of conventional URL-based delivery mechanisms.
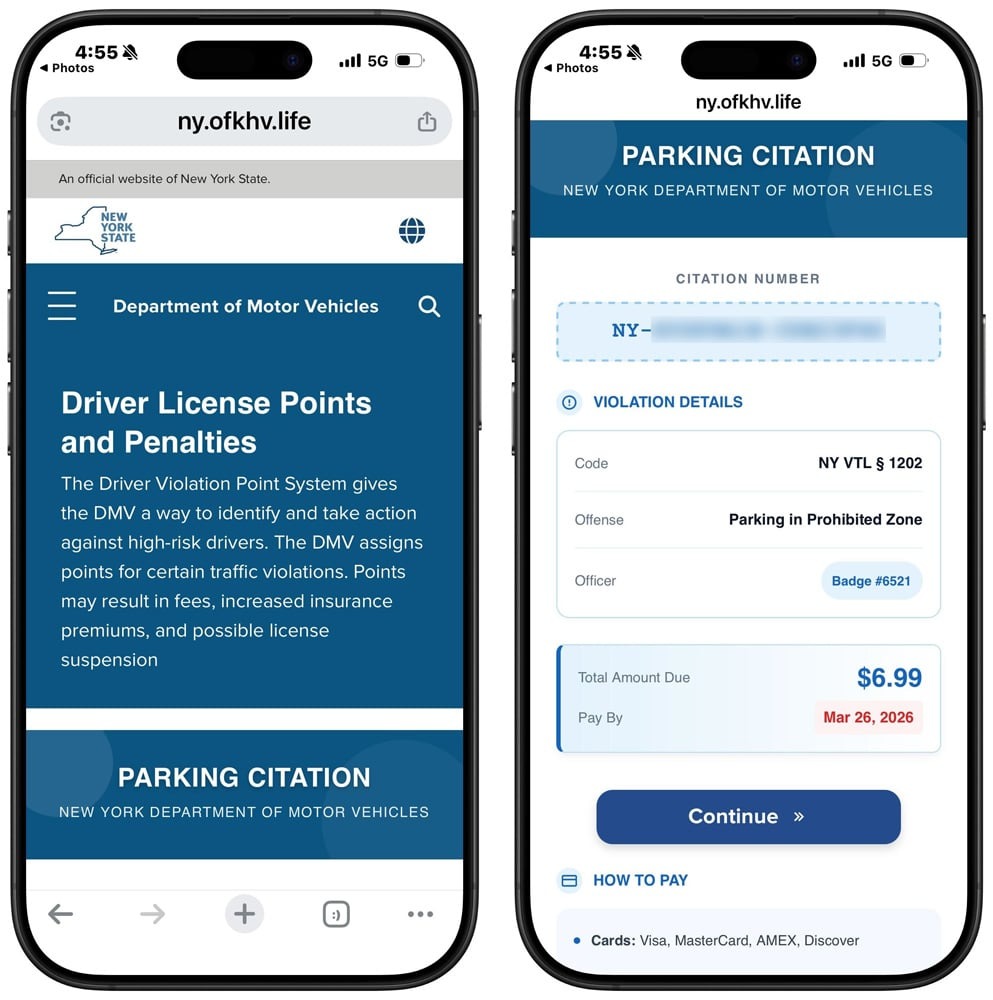
- Stealing data: Code scanning redirects targets to malicious municipal domain spoofs engineered to exfiltrate personally identifiable information and payment card data.
A traffic violation fraud campaign distributes fake "Notice of Default" documents via SMS to residents across US jurisdictions, including New York and California. The phishing campaign impersonates state judicial institutions, using urgency-based social engineering to compel immediate financial remittance or face judicial enforcement action.
This campaign demonstrates a tactical evolution in SMS-based phishing operations.
How QR Code Phishing Bypasses Security Infrastructure
Unlike preceding toll violation fraud campaigns that used direct URL embedding, these contemporary scams incorporate images of falsified court documentation with embedded QR codes.
Upon code scanning, the attack infrastructure redirects targets to intermediary domains that require CAPTCHA validation to establish human verification. After a successful CAPTCHA completion, the QR code phishing vector redirects victims to domains that masquerade as the local Department of Motor Vehicles (DMV) or equivalent municipal authorities.
The fraudulent infrastructure demands a $6.99 settlement for the fake violation. When entering payment details, threat actors immediately exfiltrate comprehensive PII, including name, residential address, phone number, email address, and payment card data.
Protecting Sensitive Data Assets
This specific methodology enables threat actors to circumvent automated security detection systems and network traffic analysis protocols, effectively obfuscating the ultimate destination of malicious infrastructure.
Government entities consistently emphasize that legitimate municipal judicial systems do not utilize SMS communications for sensitive information solicitation or final payment notifications.
In January 2025, smishing scams impersonating toll roads were on the rise, with phishing attempts targeting US E-ZPass toll payment systems surging in April. In August 2025, a Gmail voicemail phishing scam used malicious CAPTCHA on fake websites to steal credentials.