SocksEscort Cybercrime Proxy Network Taken Down in Operation Lightning, Tens of Servers and Domains Seized
- Global Coordination: Law enforcement dismantled the SocksEscort proxy network via Operation Lightning, seizing servers and domains in seven countries.
- Financial Impact: The infrastructure facilitated tens of millions of dollars in residential proxy fraud, leveraging the AVRecon botnet to compromise SOHO routers.
- Asset Seizure: Authorities successfully froze $3.5 million in cryptocurrency linked to the operation, severely disrupting the threat actors' financial operations.
The SocksEscort proxy network was dismantled in an international law enforcement initiative dubbed Operation Lightning, which resulted in the seizure of 34 domains and 23 servers across seven countries. This intervention also resulted in the freezing of approximately $3.5 million in illicit cryptocurrency assets, as per Europol.
Federal investigators attribute tens of millions of dollars in global financial losses directly to the exploitation of this proxy network.
SocksEscort Residential Proxy Fraud
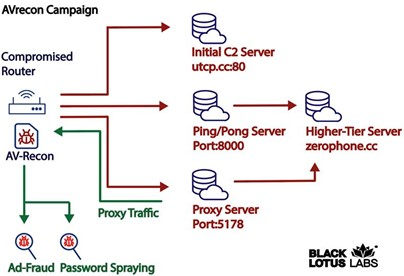
SocksEscort operated by hijacking small-office and home-office (SOHO) routers utilizing the AVRecon botnet. Threat actors deployed this malware to remotely control compromised devices and route malicious traffic through legitimate residential internet connections, according to a U.S. Justice Department (DOJ) press release.
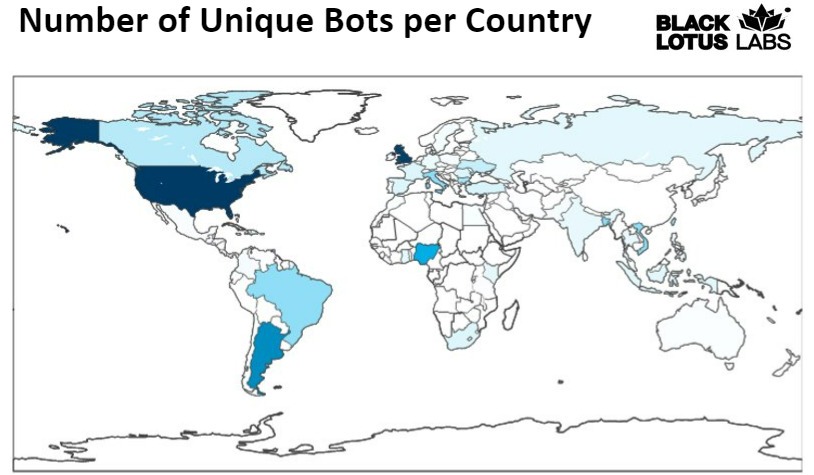
By selling access to roughly 369,000 unique IP addresses since 2020, the operators facilitated extensive residential proxy fraud. As of February 2026, the SocksEscort application listed approximately 8,000 infected routers for sale, of which 2,500 were in the U.S.
“The compromised devices were infected through a vulnerability in the residential modems of a specific brand, " according to Europol.
The DOJ said the cybercrime network, dismantled by authorities from the FBI, alongside partners in Austria, France, and the Netherlands, previously maintained a customer base of approximately 124,000 users who used the infrastructure to obscure their true locations during malicious online activities that affected thousands of U.S. persons, businesses, and financial institutions.
This illicit routing architecture enabled downstream criminals to execute takeovers of U.S. bank and cryptocurrency accounts, fraudulent unemployment insurance claims, ransomware, DDoS attacks, and the distribution of child sexual abuse material (CSAM), Europol said. Examples of victims defrauded include:
- A customer of a cryptocurrency exchange who lived in New York was defrauded of $1 million worth of cryptocurrency.
- A manufacturing business in Pennsylvania was defrauded of $700,000.
- Current and former United States service members with MILITARY STAR cards were defrauded out of $100,000.
Critical Cybersecurity Implications for Enterprise Hardware
The proliferation of illicit proxy services relies heavily on outdated or unpatched consumer-grade routers, highlighting persistent vulnerabilities within edge networking equipment. To mitigate the risk of hardware co-optation by botnets like AVRecon – a Remote Access Trojan (RAT) – Lumen security professionals advise:
- Corporate network defenders to monitor for attacks on weak credentials and suspicious login attempts and protect cloud assets from communicating with bots that are attempting to perform password spraying attacks.
- Consumers with SOHO routers to leverage properly configured and updated EDR solutions, reboot routers, and install security updates and patches.
In other recent news, the KadNap botnet hijacked Asus routers to serve as malicious proxies, comprising over 14,000 devices. Reports early last month suggested SystemBC infections exceed 10,000, including systems linked to government hosting.