Pro-Ukrainian Bearlyfy Ransomware Group Attacks Target Russian Companies
- Attack escalation: The pro-Ukrainian hacker group Bearlyfy executed over 70 cyberattacks on Russian companies, demanding substantial ransom payments.
- Custom payload: The threat actors transitioned to deploying GenieLocker malware, a custom-built Windows encryption strain.
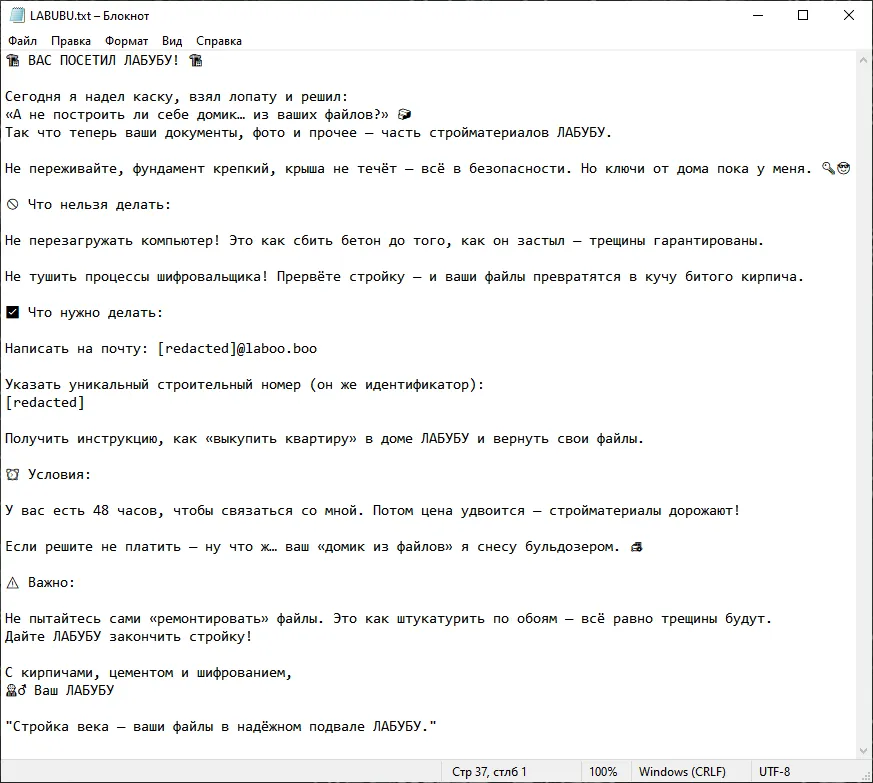
- Dual motivation: Bearlyfy ransomware attacks blend financial extortion with political sabotage, frequently featuring manually crafted ransom notes.
Suspected pro-Ukrainian Bearlyfy hacker group has reportedly escalated its digital offensive, executing more than 70 severe cyberattacks on Russian companies over the past year, according to a report by a Russian cybersecurity firm.
Initially emerging in January 2025 with modest technical capabilities and small ransom demands against regional businesses, the threat actor now systematically targets large corporate enterprises to inflict maximum operational disruption and extract substantial financial revenue.
Evolution of Bearlyfy Ransomware Attacks
Cybersecurity researchers at F6 (formerly part of Group-IB) indicate that the group has transitioned from amateur operations to highly sophisticated network intrusions, The Record recently reported.
Early campaigns relied heavily on existing tools derived from leaked source code, including the LockBit 3 Black builder and a modified Babuk variant for Linux environments.
However, a strategic shift occurred recently when the group introduced its proprietary encryption infrastructure to maximize operational impact.
Deployment of GenieLocker Malware
Since early March, Bearlyfy has actively deployed the GenieLocker malware, a custom-developed Windows ransomware strain whose cryptographic scheme and techniques are allegedly similar to those of the Venus and Trinity families. The threat actors added anti-debugging and anti-analysis tools and double integrity checking for encrypted data.
Analysts estimate that approximately one in five victims capitulates to the extortion demands, actively funding further operations.
"We're seeing Bearlyfy collaborating with other, more experienced pro-Ukrainian groups, such as Head Mare, but it has also maintained its own distinct identity from the very beginning,” said Anton Velichko, head of the F6 Digital Forensics Lab.
On the other side, the Russian state-sponsored hacking group Coldriver (formerly known as SEABORGIUM, also known as Star Blizzard, Callisto Group, TA446, TAG-53, and BlueCharlie), known for its persistent cyberespionage campaigns, developed and deployed a new suite of malware tools in October 2025.