Perseus Malware Based on Phoenix and Cerberus Predecessors Initiates Android Device Takeovers, Targets Users’ Personal Notes
- Notes targeted: The Perseus malware specifically scans note-taking applications to extract sensitive financial data and recovery phrases.
- Remote control: Attackers achieve full Android device takeover by abusing Accessibility Services for real-time monitoring and interaction.
- Evasive tactics: This threat highlights mobile malware evolution through advanced anti-analysis measures that bypass standard security environments.
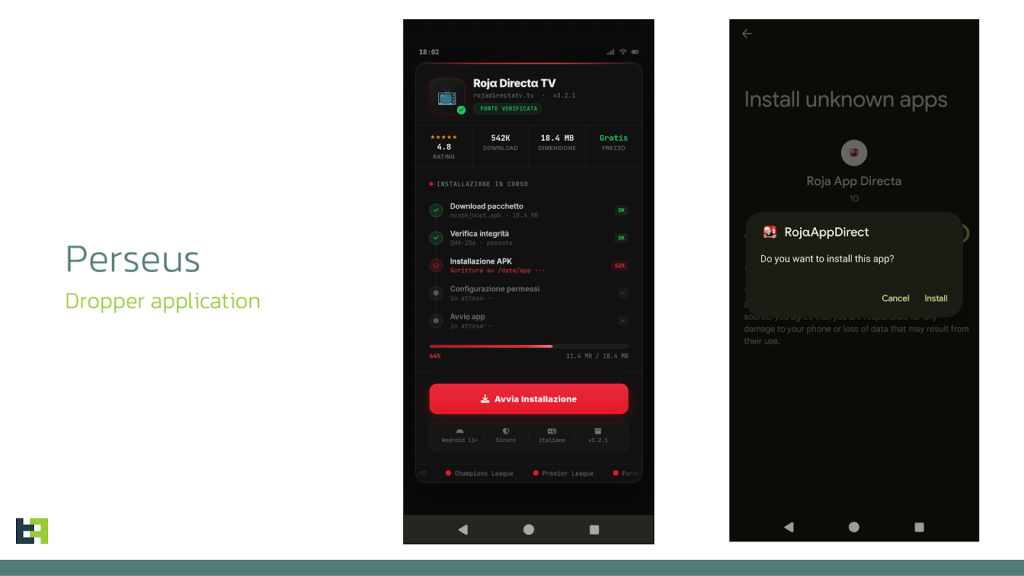
A sophisticated Android banking trojan dubbed Perseus actively hunts for user-generated content. It is disseminated through malicious IPTV applications, leveraging sideloading techniques to bypass Android 13 restrictions. Once installed, the malware requests extensive Accessibility Service permissions to initiate overlay attacks, capture keystrokes, and establish interactive remote control sessions.
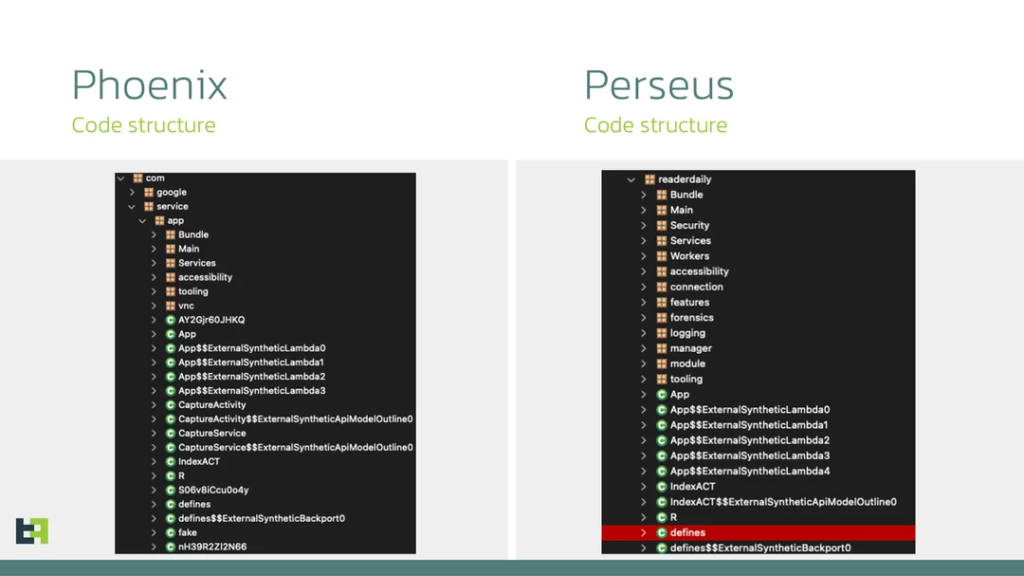
Threat intelligence researchers said this new framework builds upon the legacy of the Cerberus and Phoenix codebases to execute severe cybersecurity threats against mobile platforms and primarily targets users in Turkey and Italy.
Executing an Android Device Takeover
Perseus aggressively targets locally stored notes on Android devices, systematically opening applications like Google Keep and Evernote and scrolling through text to harvest cryptocurrency seed phrases, unencrypted passwords, and private financial details, according to the Threat Fabric Mobile Threat Intelligence Team.
Operators monitor the screen in real time and manipulate the interface to superimpose fake interfaces, capturing sensitive credentials with high accuracy. This ultimately translates to full device takeover and authorizing fraudulent transactions.
Furthermore, the malware implements stringent anti-analysis protocols. It actively scans for dynamic instrumentation frameworks such as Frida and Xposed, evaluates battery plausibility, and verifies hardware profiles to ensure it is not running on an emulator.
Mobile Malware Evolution
Perseus demonstrates a growing emphasis on evasion and operational resilience. While older trojans focused strictly on intercepting SMS messages or banking credentials, this targeted Perseus data collection marks a significant operational shift in the evolution of mobile malware.
“Its distribution through IPTV-themed droppers and its overlap with infrastructure used by other families, such as Medusa, underline how tools, delivery methods, and even codebases are reused across campaigns,” the report said.
Meanwhile, Android 17 recently restricted the accessibility API to prevent malware from requesting excessive permissions.