Key TakeawaysPixel VPN Quick Settings Update: Displays live connection status directly in tile, reducing taps and improving everyday usability.Version 2025.12.19.x…
News
Key TakeawaysNordVPN Threat Protection Pro Update: Integrates CrowdStrike Threat Intelligence to improve malicious site, phishing, and malware detection accuracy.Enterprise-Grade Threat…

Key TakeawaysNew Threat Vector: Microsoft researchers have detected a surge in "AI Recommendation Poisoning," a technique where attackers manipulate AI…
Key TakeawaysService Disruption: Russia's communication regulator, Roskomnadzor, confirmed it is deliberately slowing down Telegram, affecting nearly 90 million users across…

Key TakeawaysAbandonware Exploitation: Threat actors executed a subdomain takeover of a legitimate but discontinued Outlook add-in by registering its previously…

Key TakeawaysAttack Vector: Cybercriminals use social engineering to trick IT help desks, resetting employee passwords and MFA to gain account…

Key TakeawaysGuilty Plea: Peter Williams, the former boss of U.S. hacking tool firm Trenchant, pleaded guilty to stealing and selling…

Key TakeawaysZero-Click Vulnerability: A "zero-click" exploit tricks AI agents operating within messaging apps into exfiltrating sensitive data without user interaction.Attack…

Key TakeawaysNordVPN Birthday Deals: Up to 76% off two-year plans with three bonus months includedAmazon Voucher Offers: US, UK, CA,…
Key TakeawaysGuilty Plea: A 34-year-old U.S. Air Force Airman pleaded guilty to one count of receiving child pornography and faces…

Key TakeawaysThird-Party Breach: A data breach at HR outsourcing firm Conduent exposed the personal information of nearly 17,000 employees of…

Key TakeawaysCurrent Tactic: North Korean operatives are using verified LinkedIn profiles to impersonate professionals and establish trust with targets.Possible Goal:…
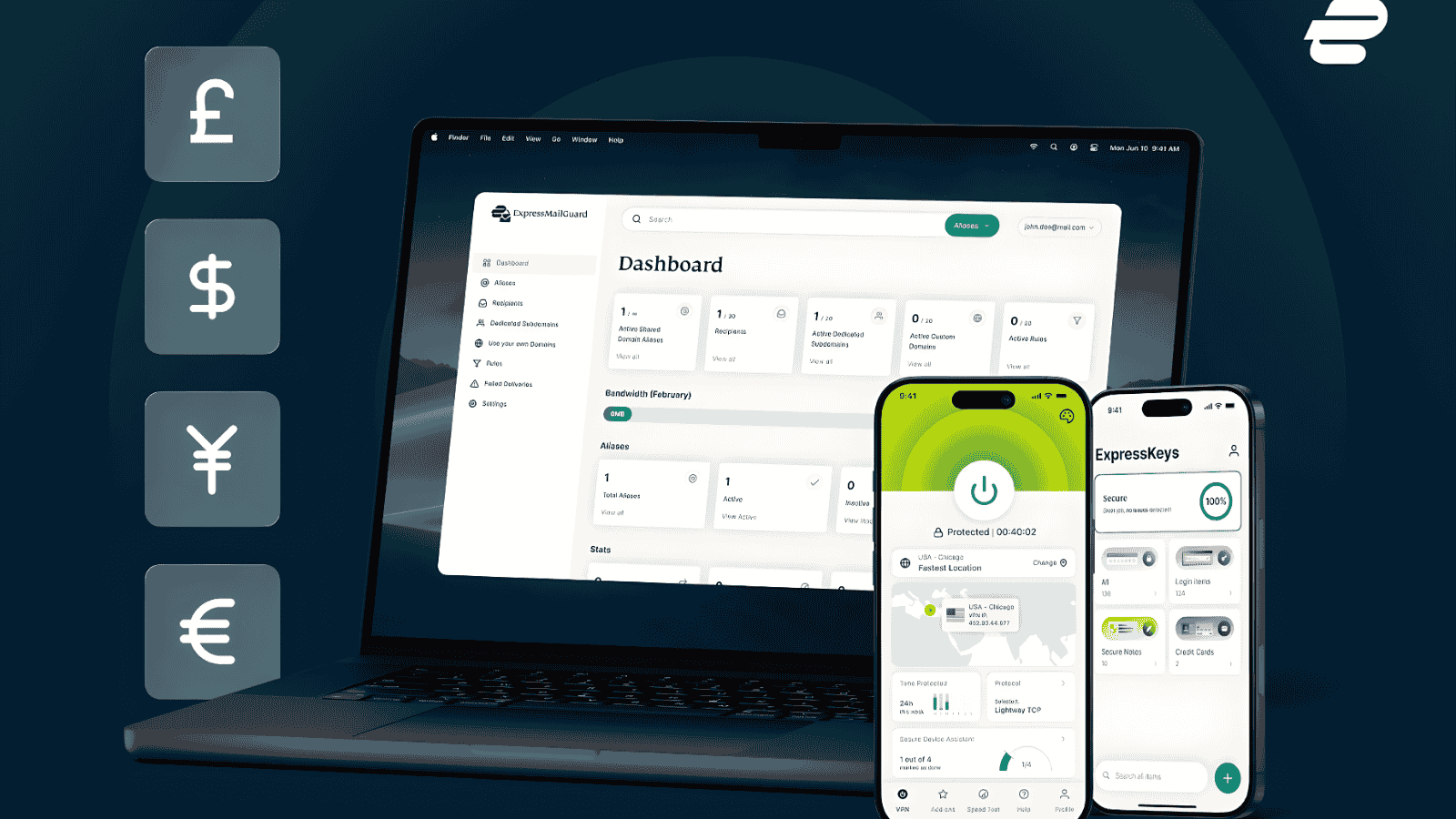
Key TakeawaysExpressVPN local currency pricing: Supports GBP, EUR, BRL; fixed prices remove exchange rate fluctuations for users.Regional expansion underway: Testing…

Key TakeawaysAI-Driven Development: Darktrace researchers identified a fully AI-generated malware strain exploiting the React2Shell vulnerability, demonstrating how LLMs lower the…
Key TakeawaysSystem Disruption: A cybersecurity incident forced the temporary suspension of operations at Senegal's Directorate of File Automation (DAF), the…

Key TakeawaysCritical Flaws Exposed: Two zero-day vulnerabilities (CVE-2026-1281 and CVE-2026-1340) in Ivanti Endpoint Manager Mobile (EPMM) allow attackers to hijack…
Key TakeawaysMassive Data Exposure: A hacktivist scraped and published the payment records of over half a million customers of consumer-grade…
Lorna Mahlock – U.S. Cyber Command Marine Corps Maj. Gen. Lorna Mahlock has been confirmed by the U.S. Senate as…

Key TakeawaysDatabase Sale: Threat actor "quellostanco" claims to be selling a database of approximately 104,000 records allegedly stolen from EgyptAir…







