Newly Discovered Android Malware, DroidBot, Targets 70+ Banking and Crypto Apps
- DroidBot acts as a malware-as-a-service (MaaS) designed for Android.
- Over 770 infections were identified across many European countries.
- The malware can intercept SMS messages, log information, and access devices remotely.
Being a fairly open mobile platform, Android is often affected by data-stealing malware and remote access Trojans. Even though Google is focused on increasing the platform’s resilience, new malware breeds appear more often than ever. The latest malware breed was discovered by Cleafy researchers, targeting banking and crypto apps.
Named DroidBot, this Remote Access Trojan (RAT) operates as a malware-as-a-service (MaaS). It’s available for $3,000 per month, offering less experienced malicious actors the complete set of tools to steal highly sensitive information. This includes the malware builder, command-and-control (C2) servers, and a central admin panel to control operations, extract stolen data, and issue commands.
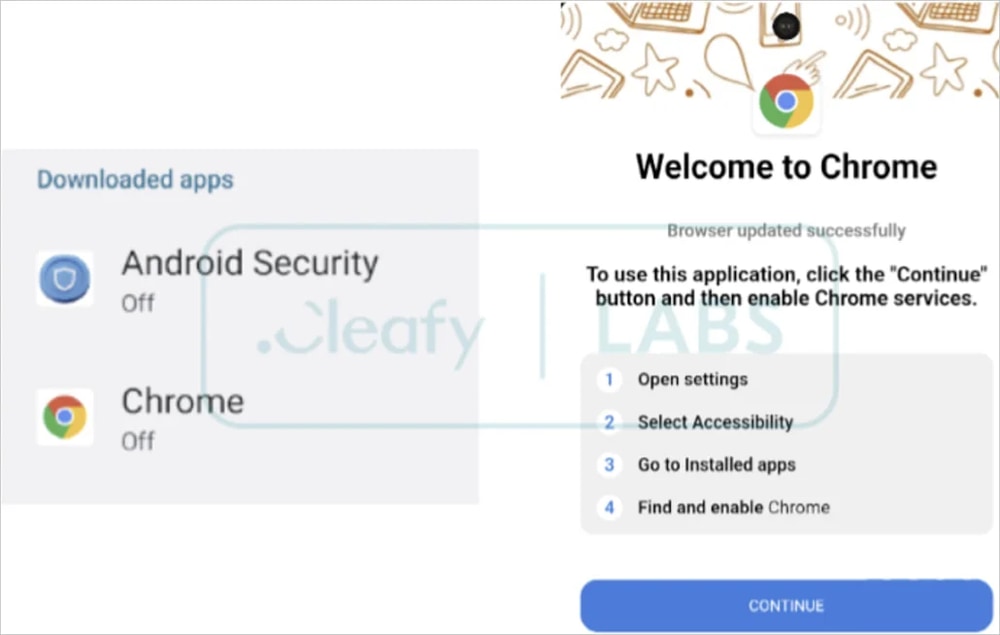
DroidBot uses standard decoys to trick users into installing fake apps, which usually present as Google services, generic security apps, or popular banking apps. It takes advantage of Android’s Accessibility Services to perform its functions. That means the user must willingly provide access to these services, usually during the initial installation stages.
Upon granting access to Accessibility Services, DroidBot can perform a wide range of functionalities, including:
- SMS Interception: The malware can intercept incoming SMS messages, capturing transaction authentication numbers and bypassing two-factor authentication mechanisms.
- Key-Logging: DroidBot can capture any information entered or displayed on the device’s screen, including login credentials, personal data, account balances, and more.
- Overlay Attack: A fake log-in page can be presented over legitimate banking apps, which is how DroidBot captures valid user credentials.
- VNC-Like Routine: This functionality allows the malware to take screenshots of the victim’s device, providing visual data to malicious actors.
- Screen Interaction: Using Accessibility Services, DroidBot can enable remote access to the infected device. This allows malicious actors to tap buttons, fill out forms, navigate through apps, and more.
Regarding the affected apps, Cleafy notes that 77 banking and crypto apps have been identified as potential targets. Those include Binance, KuCoin, BBVA, Unicredit, Santander, Metamask, BNP Paribas, Credit Agricole, Kraken, Garanti BBVA, and more.
Furthermore, 17 affiliate groups have been identified, revealing a network of botnets and 770+ infections throughout France, Belgium, Spain, Italy, and Turkey, which are the most targeted countries. Infections were also observed in the UK, Norway, Sweden, Finland, Germany, Poland, Greece, and other European countries.
To avoid a DroidBot infection, Android users are advised to download apps only from the Play Store. They should also scrutinize permission requests and make sure “Play Protect” is active on their mobile devices.