Mercor AI Cyberattack Tied to LiteLLM Project Compromise, Lapsus$ Claims Breach
- Startup breached: The Mercor cyberattack exposed sensitive corporate data following a severe supply chain intrusion by extortionist hacking syndicates.
- LiteLLM project compromise: Threat actors successfully infiltrated the open-source LiteLLM repository, inserting malicious payloads that affected thousands of downstream enterprise environments.
- Cybersecurity risks escalate: This widespread open-source vulnerability highlights the severe operational dangers associated with integrating unverified third-party dependencies into proprietary network architectures.
A Mercor AI cyberattack was confirmed, stemming from a recent supply chain exploit involving the LiteLLM project compromise. The announcement follows the Lapsus$ threat actor's claims of targeting the prominent artificial intelligence (AI) recruiting startup and stealing 4TB of data.
The LiteLLM incident has been linked to TeamPCP. The breach originated when malicious actors exploited an open-source vulnerability to infiltrate the LiteLLM repository and distribute malicious code to thousands of downstream environments.
LiteLLM Project Compromise
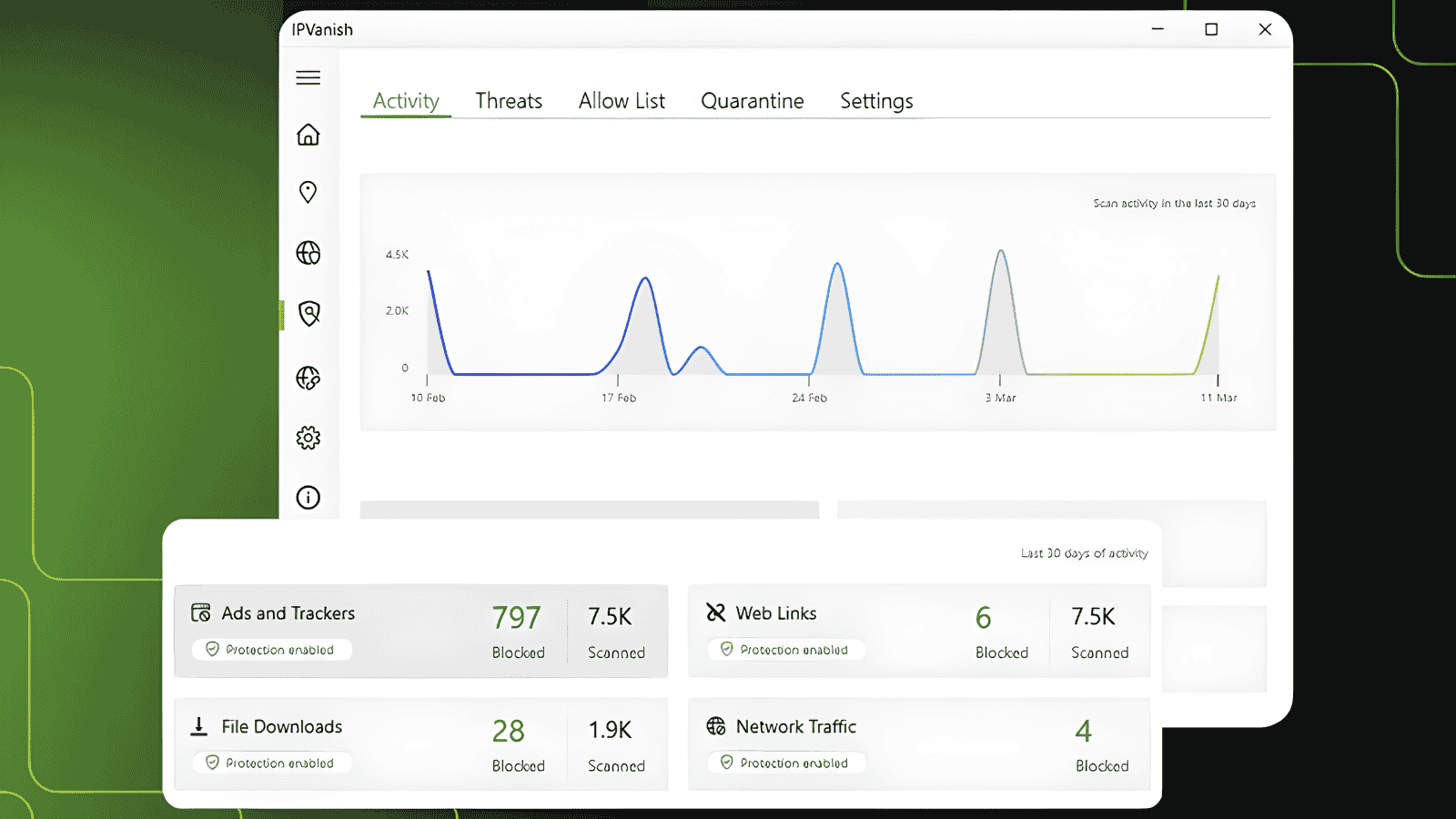
Reports say Lapsus$ auctioned the Mercor data on the dark web, claiming to have breached the company’s Tailscale VPN and exfiltrated the entire 4-terabyte database. The compromised assets potentially include a 211GB user database, 939GB of source code, and 3TB of storage buckets with video interviews and passports.
The leaked sample of allegedly stolen Mercor data included internal Slack communication logs, ticketing databases, and video interactions between AI systems and human contractors, according to TechCrunch.
Mercor has initiated comprehensive incident response protocols and engaged external forensic experts to secure and remediate the compromised infrastructure. The connection between Lapsus$ and TeamPCP is not yet clear.
Escalating Cybersecurity Risks
The Mercor cyberattack demonstrates how a single compromised dependency can bypass enterprise perimeter defenses, granting unauthorized actors direct access to proprietary data.
LiteLLM suspects that the compromise originated from the Trivy dependency used in its CI/CD security scanning workflow. The Trivy open-source security scanner was recently compromised by threat actors who extracted privileged access tokens.
Socket also noted that Trivy Docker images pushed to Docker Hub without corresponding GitHub releases contained infostealer IOCs associated with TeamPCP.