LeakNet Ransomware Tactics: New ClickFix Lures Delivered via Compromised Legitimate Websites & Deno Loader
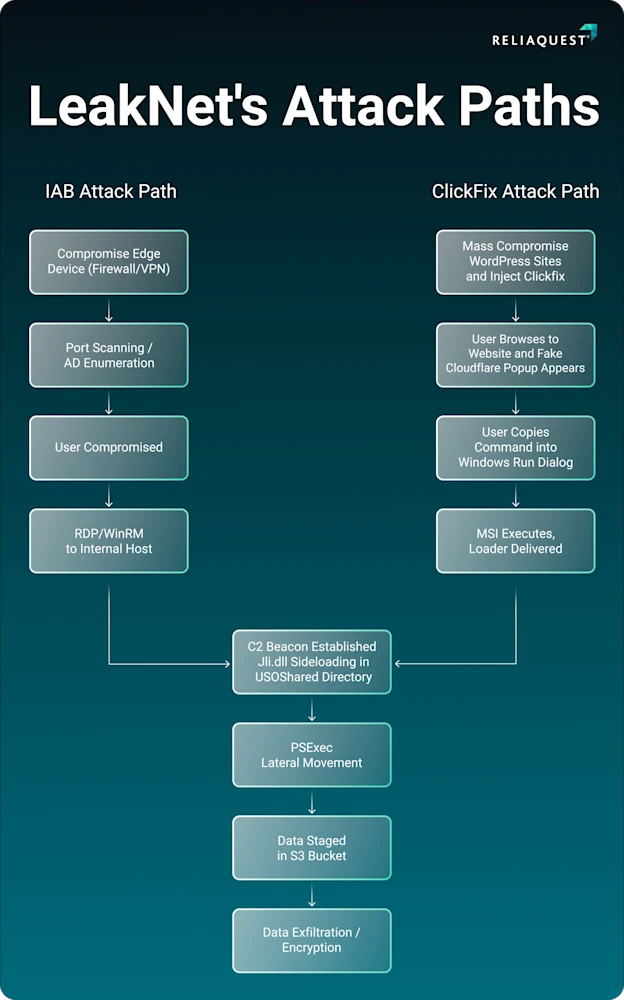
- New Access Tactics: The LeakNet ransomware group now utilizes ClickFix lures hosted on compromised legitimate websites.
- Stealthy Execution Method: Attackers deploy a novel Deno-based loader that executes base64-encoded payloads entirely in memory.
- Predictable Attack Chain: These cybersecurity threats consistently follow a post-exploitation sequence of DLL sideloading, lateral movement, and staging.
LeakNet ransomware employs ClickFix lures on compromised legitimate websites, a newly confirmed initial access method that is part of its fundamental shift in attack methodologies, which compresses the timeframe from initial access to data encryption. The threat actor also leverages a staged command-and-control (C2) loader built on Deno.
ReliaQuest security researchers have identified a strategic departure from relying on initial access brokers (IABs), which was likely the group’s previous tactic. The group now generates direct network footholds using sophisticated social engineering techniques and memory-centric execution runtimes.
ClickFix Lures for Initial Access
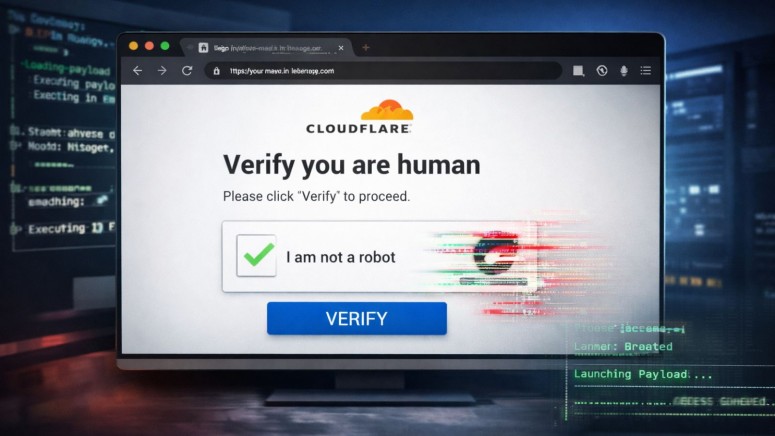
The compromised legitimate websites display ClickFix lures – deceptive error prompts that trick visitors into manually executing malicious system commands. Attackers typically utilize a fake Cloudflare Turnstile verification page, a Microsoft Installer (MSI), and a VBS file.
Following successful user interaction, the attack sequence initiates a novel Deno-based loader (a legitimate JavaScript and TypeScript runtime environment). Attackers exploit this utility through a "bring your own runtime" (BYOR) execution model, use a fileless execution mechanism that fingerprints the victim machine, and establish C2 communication.
Despite the evolving entry vectors, these escalating cybersecurity threats maintain a highly predictable post-exploitation playbook. Upon establishing persistence, LeakNet ransomware operators consistently execute Dynamic Link Library (DLL) sideloading and use PsExec-based lateral network movement and S3 bucket payload staging.
Preventing LeakNet Initial Access and Lateral Movement
By leveraging established web infrastructure, LeakNet bypasses standard network-layer reputation filters. Using Deno turns allowlists and “unknown binary” heuristics less effective, and fileless execution effectively circumvents traditional signature-based endpoint protections.
To disrupt this attack chain, security administrators must:
- Block newly registered domains,
- Restrict Win-R access,
- Limit PsExec to authorized administrators.
In January, an ErrTraffic ClickFix tool industrialized social engineering malware. However, a free ‘ClickFix Hunter’ tool was made available last month after the ErrTraffic ClickFix service was observed to be industrializing social engineering malware.