Japanese School Yokosuka Gakuin Confirms Ransomware Attack and Data Leak Claimed by Rhysida
Key Takeaways
- Ransomware confirmed: Yokosuka Gakuin School Corporation confirmed it sustained a ransomware attack in early December 2025 that led to a data breach.
- Unauthorized access: The incident, claimed by Rhysida, involved unauthorized external access to a server, where a malicious program was executed.
- Data leakage: An investigation revealed that multiple photos, videos, and other materials were exfiltrated from the compromised server.
The Yokosuka Gakuin School Corporation, a prominent educational institution in Japan, has publicly disclosed a significant ransomware attack that resulted in a data leak. In a statement, the school confirmed it was the victim of a cyber intrusion in early December 2025.
The event was first identified after a university employee was unable to connect to a server, prompting an immediate investigation that uncovered illegal external access and the execution of a malicious program.
Rhysida Unauthorized Access and Data Exfiltration
The investigation confirmed that threat actors achieved unauthorized server access and deployed ransomware. As a result of the breach, the school discovered that multiple files, including photos and videos, had been leaked from the compromised system.
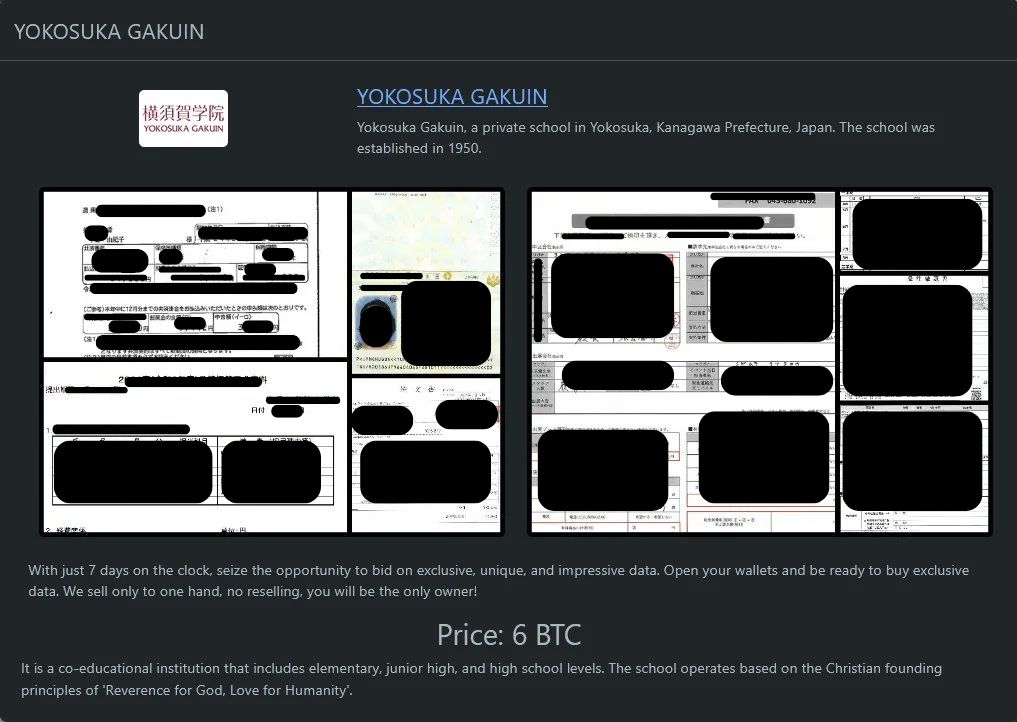
Meanwhile, the Rhysida seems to be auctioning sensitive internal files and personal identification records now for 6 BTC. Reports suggest that the threat actor conducted the cyber intrusion on December 15, allegedly via exploiting vulnerabilities in the institution’s network.
The full scope of the exfiltrated data is still being determined as part of the ongoing forensic analysis. This type of data breach in education highlights the vulnerability of academic institutions, which often hold large volumes of potentially sensitive information about students and staff.
Response and Mitigation Efforts
Upon discovering the attack, Yokosuka Gakuin took immediate action to contain the threat by disconnecting its systems from the internet. The institution is now collaborating with external specialists to conduct a thorough investigation and restore affected systems.
The school's public statement apologized for the concern caused and committed to providing updates as the situation develops.
Among the threat actor’s claimed targets this year are Cookeville Regional, the U.S. architecture and engineering company LaBella Associates, and Bayhealth Medical Center, as well as Sunflower Medical Group and Community Care Alliance (CCA).