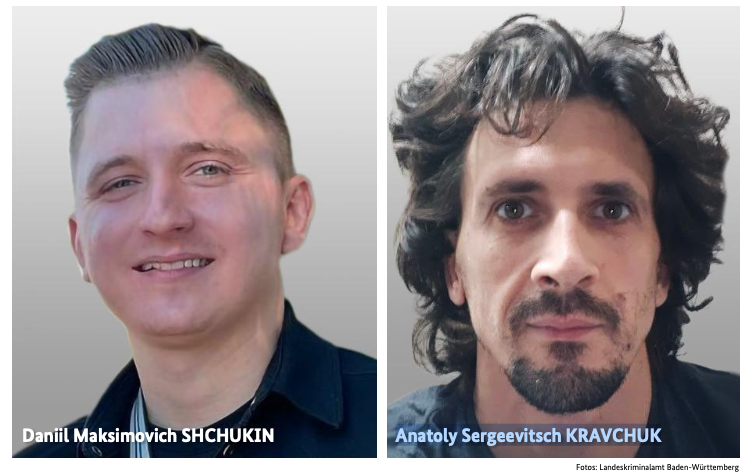
Germany Reveals the Name of Alleged REvil Ransomware, GandCrab Leader Daniil Maksimovich Shchukin (UNKN)
- Alleged leader identified: German authorities unmasked Daniil Maksimovich Shchukin as "UNKN," the alleged mastermind behind the REvil and GandCrab ransomware operations.
- Extensive sabotage acts: The suspect reportedly orchestrated 130 computer sabotage incidents in Germany, causing €35 million in economic damage between 2019 and 2021.
- Global cybersecurity risks: The identification marks a major milestone in combating double extortion tactics that have severely elevated global cybersecurity risks for enterprise networks.
German federal authorities have officially identified the elusive cybercriminal known as UNKN (or UNKNOWN) as 31-year-old Russian national Daniil Maksimovich Shchukin. The German Federal Criminal Police (BKA) alleges that Shchukin acted as the primary architect behind the notorious REvil ransomware gang and the GandCrab ransomware affiliate program.
Working alongside 43-year-old associate Anatoly Sergeevitsch Kravchuk, Shchukin reportedly executed widespread cyber extortion campaigns targeting critical enterprise infrastructure.
Unmasking GandCrab, REvil Ransomware Ops
The BKA investigation links the suspects to at least 130 distinct acts of computer sabotage within Germany alone. Between 2019 and 2021, these operations extorted nearly €2 million from victims and inflicted roughly €35 million in economic damage.
Shchukin's syndicates pioneered double extortion, demanding simultaneous payments for system decryption keys and data confidentiality. The GandCrab ransomware operation functioned as a highly profitable affiliate network before transitioning into the REvil structure, which infamously compromised IT management firm Kaseya in July 2021.
Furthermore, United States Justice Department filings from 2023 directly connected Daniil Maksimovich Shchukin to cryptocurrency wallets containing over $317,000 in illicit proceeds.
Mitigating Global Cybersecurity Risks
By doxing network administrators who facilitate Ransomware-as-a-Service (RaaS) deployment models, international law enforcement agencies systematically disrupt the operational anonymity that shields cybercriminal enterprises.
While Shchukin is currently believed to reside in Krasnodar, Russia, the publication of his identity and associated technical infrastructure significantly restricts his operational mobility.
Threat actors were arrested and charged for REvil Ransomware attacks in 2021, with $6 million seized. In 2024, authorities announced that a notorious Russian hacker connected to Conti and LockBit was apprehended.