DPRK Phishing Campaigns Exploit GitHub C2 to Target Users in South Korea
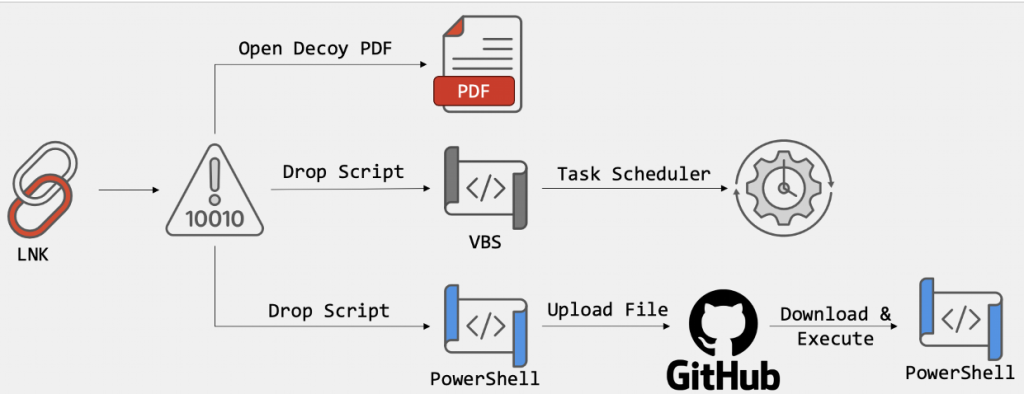
- LNK file attacks: Recent Democratic People's Republic of Korea (DPRK) cyber campaigns utilize malicious LNK files containing encoded PowerShell scripts to infiltrate systems and deploy decoy PDF documents.
- GitHub C2 infrastructure: Threat actors leverage the GitHub API as a covert command and control channel, effectively hiding malicious data transfers within standard encrypted connections.
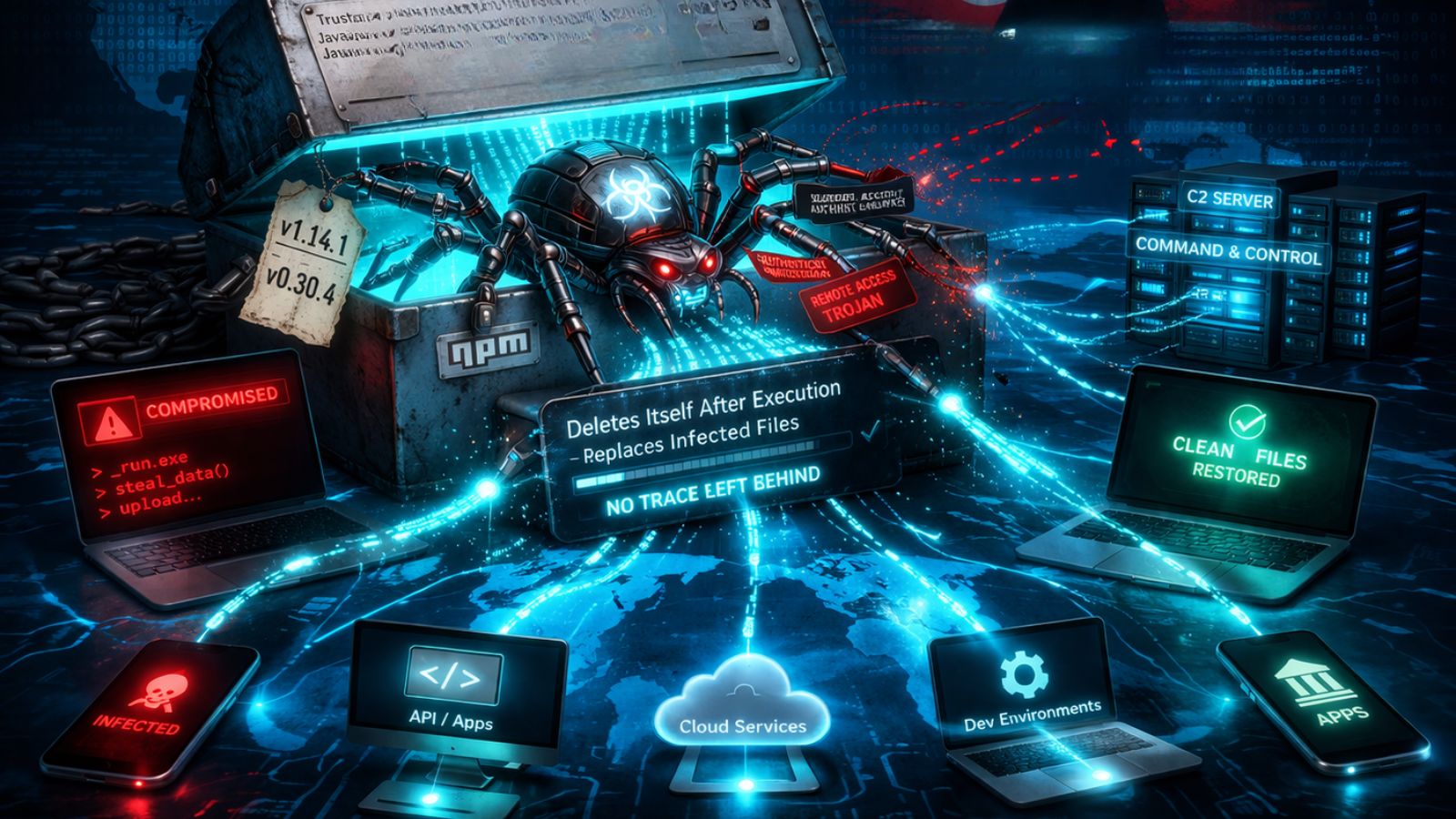
- Cybersecurity risks escalate: The malware evades detection by terminating if analysis tools are present, subsequently establishing persistence and exfiltrating system data to private repositories.
DPRK cyber campaigns that execute multi-stage LNK-file attacks target organizations in South Korea. These state-sponsored threat actors infiltrate Microsoft Windows environments to establish persistent access and exfiltrate sensitive enterprise data and leverage GitHub as Command and Control (C2) infrastructure to evade detection, cybersecurity researchers have discovered.
The infection sequence begins when victims open deceptive shortcut files disguised as legitimate business documents. Recent iterations of these LNK file attacks embed complex decoding functions directly within the file arguments.
Exploiting GitHub C2 Infrastructure
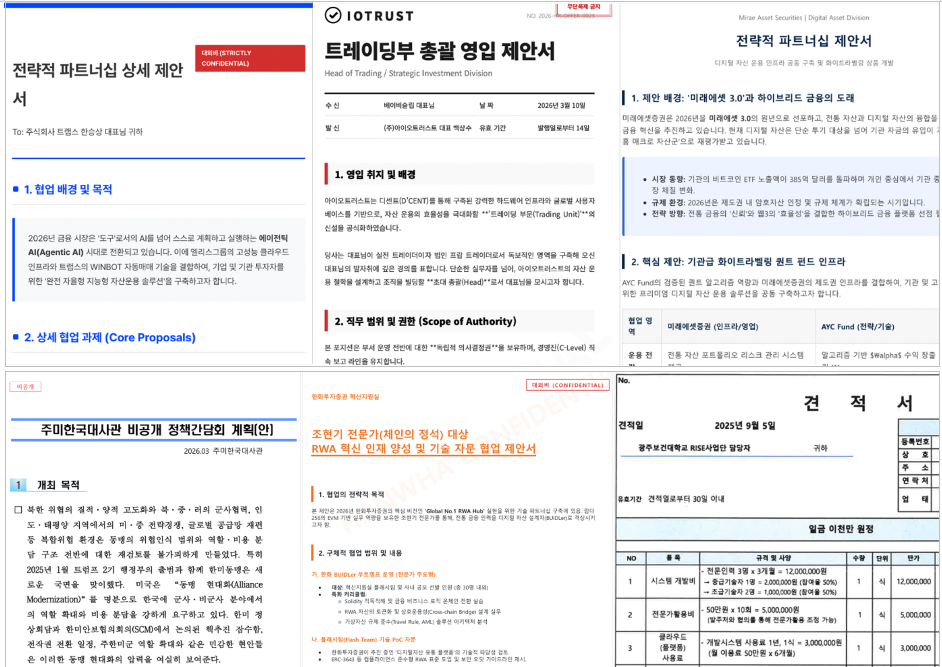
Once activated, the payload drops a decoy PDF to avoid suspicion while silently executing a malicious PowerShell script in the background, according to a new FortiGuard Labs report. The attackers employ multiple phishing themes. In one example, the document was a translation document with the DeepL branding.
To maintain operational security, the script actively scans the host environment for virtual machines, debuggers, or forensic analysis software.
After successfully bypassing initial environmental checks, the malware establishes systemic persistence through a Windows Scheduled Task configured to execute a VBScript payload periodically.
The defining characteristic of this operation is its reliance on GitHub C2 infrastructure. The North Korean threat actors utilize hardcoded access tokens to transmit compromised system data, including operating system versions, boot times, and running processes, directly to private GitHub repositories.
Covert Operation
Routing communications through the legitimate GitHub API effectively masks malicious traffic within trusted, encrypted web connections, easily bypassing standard corporate firewall filters. To defend against these advanced persistent threats, Sectigo’s Jason Soroko recommends prioritizing behavioral monitoring, scrutinizing network anomalies, and closely watching the execution of built-in utilities.
“The fact that this shortcut file creates a chain that ultimately reaches out to a GitHub repository, and pulls scripts over the internet, should put network defenders on alert that even productivity platforms can be attack vectors,” said Jamie Boote, Senior Manager, Strategic Security Consulting at Black Duck.
Boote highlighted a broader shift towards making the cloud-hosted and AI-assisted developer toolchain an attack surface.
Although these LNK files can be traced back to 2024, earlier versions had less obfuscation and contained significant metadata, allowing tracking of similar attacks spreading the XenoRAT malware.