DarkSword iPhone Exploit Kit Newer Version Leaks on GitHub, Exposing iOS Users to Spyware
- Public GitHub leak: The DarkSword spyware source code is now publicly accessible, allowing inexperienced hackers to easily execute severe iOS vulnerabilities.
- Massive cybersecurity threat: The leaked HTML and JavaScript exploits threaten hundreds of millions of Apple devices currently running iOS 18 or older operating systems.
- Data exfiltration risks: This iPhone exploit kit leak enables attackers to remotely steal sensitive user data, including messages, call histories, and cryptographic keychains.
A newer version of the DarkSword advanced hacking tool was publicly released on GitHub. Security researchers warn that the readily available code requires no specialized expertise to execute, leaving iOS users at immediate risk of severe data theft.
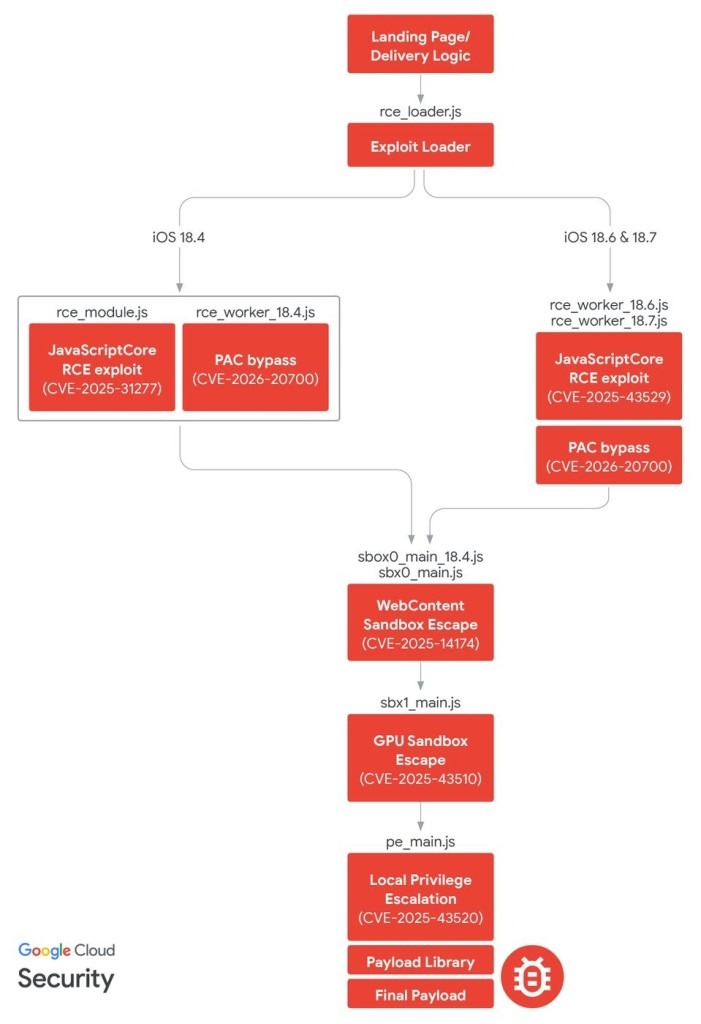
The DarkSword exploit kit leverages six patched iPhone vulnerabilities, some as zero-days, a Google Threat Intelligence Group (GTIG) report stated. The public leak gives cybercriminals out-of-the-box access to deploy the DarkSword advanced iOS spyware and harvest sensitive user data.
Analyzing the DarkSword Spyware
The leaked new versions of DarkSword spyware share the same infrastructure as the previously discovered ones but contain uncompiled files that are easy to copy and paste and host on a server, Matthias Frielingsdorf, the co-founder of iVerify, told TechCrunch on Monday. Google agreed with Frielingsdorf’s assessment.
Once an attacker hosts these malicious files on a remote server, they can deploy the DarkSword spyware without needing deep technical knowledge of Apple's underlying architecture.
Upon successful execution, the malware injects a payload that systematically reads and exfiltrates forensically relevant device files. This may include highly sensitive information such as user contacts, text messages, call logs, and the device keychain, which securely stores Wi-Fi passwords and authentication secrets.
Assessing the Widespread Security Impact
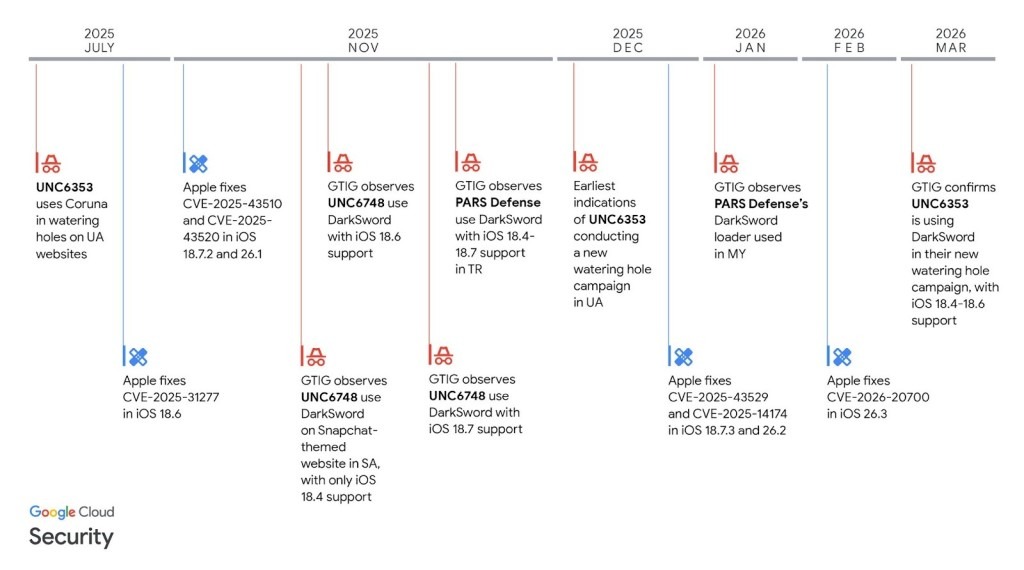
Originally identified in targeted nation-state attacks, this tool now poses a widespread cybersecurity threat to the general public. GTIG researchers last week identified commercial surveillance vendors and suspected state-sponsored cyberespionage groups, including UNC6748, PARS Defense, and suspected Russian espionage group UNC6353, among the actors that leverage Darksword to target Saudi Arabia, Turkey, Malaysia, and Ukraine.
The exploit specifically targets hardware running iOS 18 or older firmware versions. Apple metrics indicate that approximately one-quarter of all active iPhones and iPads operate on these outdated systems. Security administrators and users must immediately update their hardware to the latest available software patches or enable Lockdown Mode.
The proliferation of a single exploit chain across disparate threat actors mirrors the previously discovered Coruna iOS exploit kit, which was allegedly developed by U.S. defense contractor L3Harris’s Trenchant division (a former Trenchant senior pleaded guilty to two counts of theft of trade secrets he reportedly sold to a Russian zero-day exploit broker). Notably, UNC6353, previously observed using Coruna, moved to incorporating DarkSword into their watering hole campaigns.