CISA Urges Organizations to Harden Endpoint Management Systems After Cyberattack Against US Medical Giant Stryker
- CISA security directive: The agency urged organizations to harden Microsoft Intune security to mitigate critical endpoint management vulnerabilities.
- Business operations disrupted: The Stryker cyberattack caused severe global disruptions to order processing, product manufacturing, and customer shipments.
- Handala claims responsibility: An Iran-linked hacking group claimed the attack, stating it was retaliation for a recent strike in southern Iran.
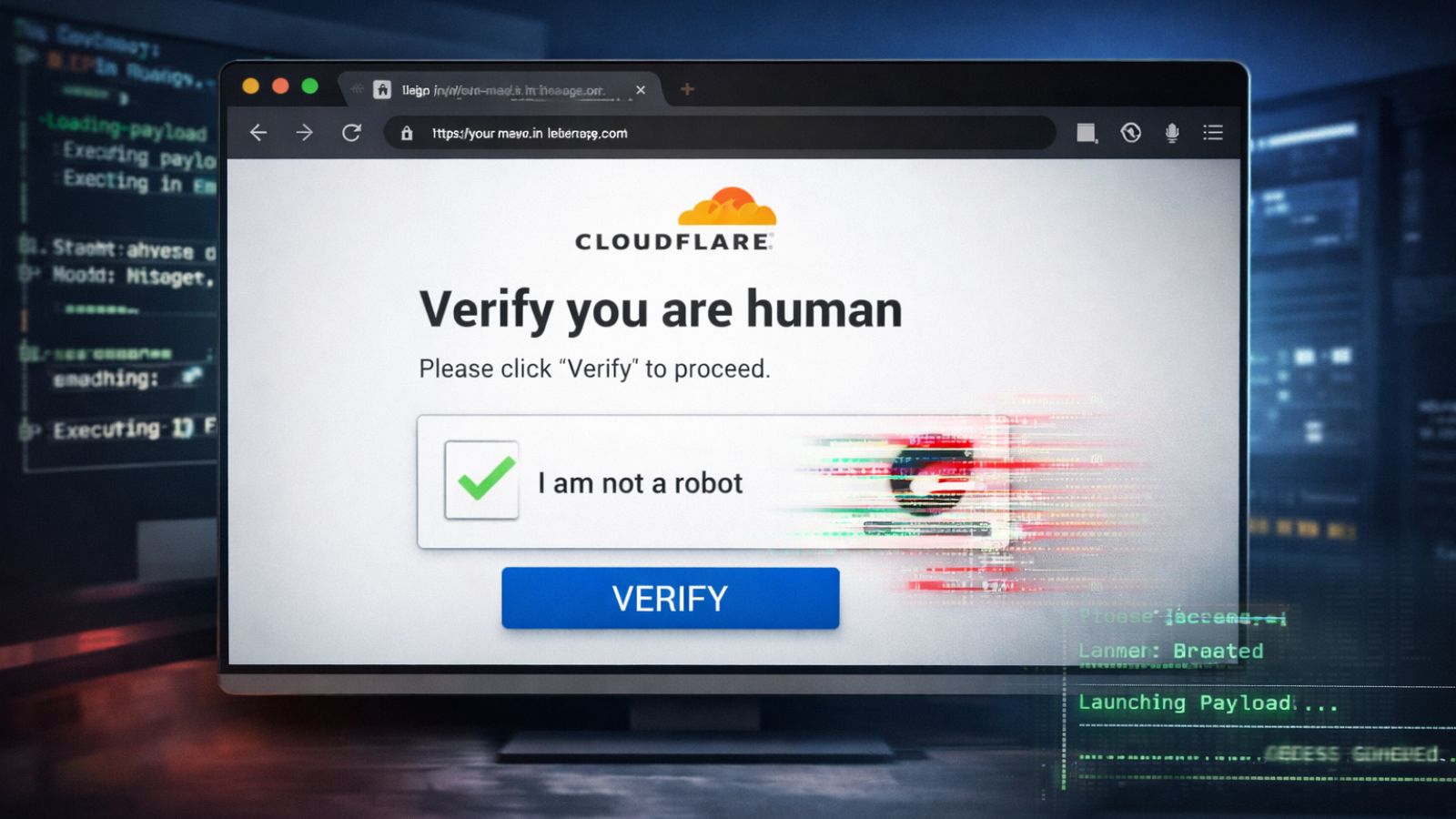
The U.S. government has issued a critical advisory urging organizations to fortify their endpoint management systems following a severe cyberattack on medical device manufacturer Stryker Corp. The March 11 intrusion compromised Stryker's computer systems, triggering a global disruption across its Microsoft environment that paralyzed order processing, manufacturing, and shipping operations.
Microsoft Intune Attack
In response to the incident, the Cybersecurity and Infrastructure Security Agency (CISA) issued an alert. “CISA is aware of malicious cyber activity targeting endpoint management systems of U.S. organizations based on the March 11, 2026, cyberattack against U.S.-based medical technology firm Stryker Corporation, which affected their Microsoft environment,” the alert said.
CISA specifically directed organizations to implement robust cybersecurity measures to harden system configurations and protect Microsoft Intune security.
This cloud-based tool manages user access, mobile devices, and applications across corporate networks, making it a high-value target for threat actors seeking broad administrative control.
Mitigating Endpoint Management Vulnerabilities
Stryker last week confirmed a security incident that wiped employee devices but denied a ransomware attack, with an Iran-linked threat actor known as Handala claiming the cyberattack and the exfiltration of 50 TB of data as a retaliatory measure for a strike on a school in Minab, southern Iran.
While Stryker confirmed the containment of the breach and stated that connected medical products remained uncompromised, Bloomberg reports indicated the disruption delayed surgeries for some patients.
Security administrators must proactively audit their configurations to defend against sophisticated actors exploiting endpoint management vulnerabilities within complex digital environments:
- Use principles of least privilege when designing administrative roles.
- Use Microsoft Entra ID capabilities (including Conditional Access, MFA, risk signals, and privileged access controls).
- Configure access policies to require Multi Admin Approval in Microsoft Intune.
CISA is currently coordinating with federal partners, including the Federal Bureau of Investigation (FBI), to monitor additional threats and determine further mitigation strategies.