Canis C2 Surveillance Framework Exposed API Discovered Targeting Japan
- Framework exposed: Security analysts uncovered the Canis C2 surveillance system via an exposed API on a malicious Japanese server.
- Extensive targeting: This highly sophisticated cross-platform malware actively compromises Android, iOS, Windows, Linux, and macOS.
- Deceptive tactics: Attackers deploy targeted phishing campaigns spoofing legitimate regional financial services to trick victims into executing malicious payloads.
Threat intelligence researchers recently identified a previously undocumented threat, dubbed the Canis C2 surveillance framework, which grants attackers access to the infected device's location and media, as well as the ability to perform credential overlay injection and arbitrary code execution.
The investigation began when Hunt.io analysts detected a phishing Android application mimicking Paidy, a Japanese buy-now-pay-later service, via a domain spoofing Pay-Easy, a separate Japanese payment service that allows users to pay via PC, smartphone, or ATM without visiting a bank.
Complex Phishing, Cross-Platform Malware Capabilities
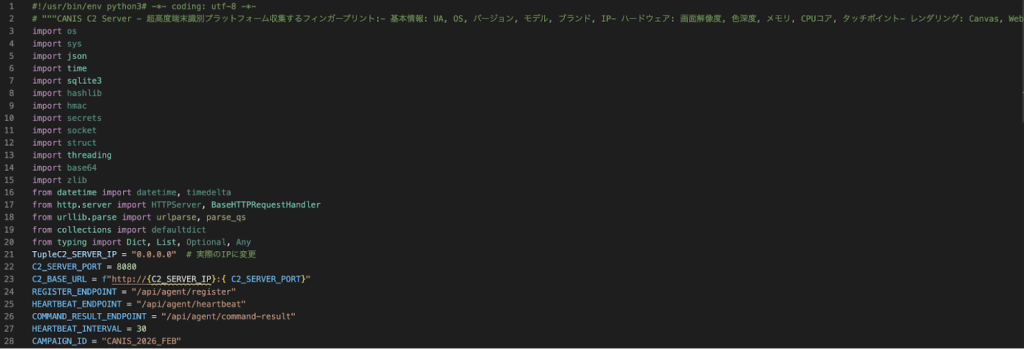
This initial access vector led researchers to an exposed backend API, revealing the full operational scope of the Canis command-and-control (C2) surveillance architecture.
“The actor behind it is clearly comfortable with Japanese, and large portions of the codebase show signs of LLM-assisted development,” the security researchers noted, who believe Canis may use some variation of ForcedEntry, an NSO exploit targeting the same features from 2021.
Threat actors orchestrated highly deceptive phishing campaigns, presenting victims with fabricated electric billing statements that ultimately installed malicious apps that granted attackers extensive administrative device permissions.
This cross-platform malware demonstrates exceptional technical sophistication. The framework deploys dedicated agents for Android, iOS, Windows, Linux, and macOS environments and includes a browser-based JavaScript agent that supports over 20 commands. Upon installing and granting the app permissions, the operator has access to:
- GPS tracking,
- Camera and audio capture,
- Credential overlay injection,
- Arbitrary code execution via a registered ServiceWorker.
The malware analyzes complex sandbox bypasses for iOS devices (BlastDoor, ImageIO) and executes Active Directory enumeration scripts against Windows enterprise networks.
Following the actor catching on to the researchers’ activity, a new iteration was seen that featured a standard American Express credit card account login page without any download prompt. Yet, the HTML source included JavaScript that referenced several paths, including "/api/proxy/", "/aitm_capture", and others.
Regional Threats
The emergence of the Canis C2 architecture highlights a critical escalation in localized cyberespionage operations. Users are advised to avoid installing unofficial applications and to be wary of suspicious email attachments.
Early this month, a DPRK phishing campaign exploited GitHub C2 to target users in South Korea, and a fake WhatsApp spyware app targeted users in Italy. In March, a sophisticated phishing campaign exploited trusted Cisco domains, impersonating JPMorgan to target a European security vendor.
In an interview with TechNady, Bitdefender’s Security Analyst Alina Bizga detailed how fraud becomes more accessible as AI tools and Scam-as-a-Service platforms enable coordinated campaigns.




![Webpage for americanexpress-site[.]com. | Source: Hunt.io](https://cdn.technadu.com/wp-content/uploads/2026/04/image-28-1024x484.png)