BlueHammer Zero-Day Exploit Leverages Windows Privilege Escalation, Prompts Security Concerns
- BlueHammer zero-day exploit: A disgruntled researcher publicly released code for an unpatched Windows privilege escalation vulnerability, granting attackers elevated system permissions.
- Disclosure motivations: The researcher leaked the vulnerability dubbed BlueHammer in response to Microsoft's handling of the private security disclosure process.
- Cybersecurity risks increase: The vulnerability leak provides attackers with local access capabilities to compromise systems, despite implementation bugs in the published code.
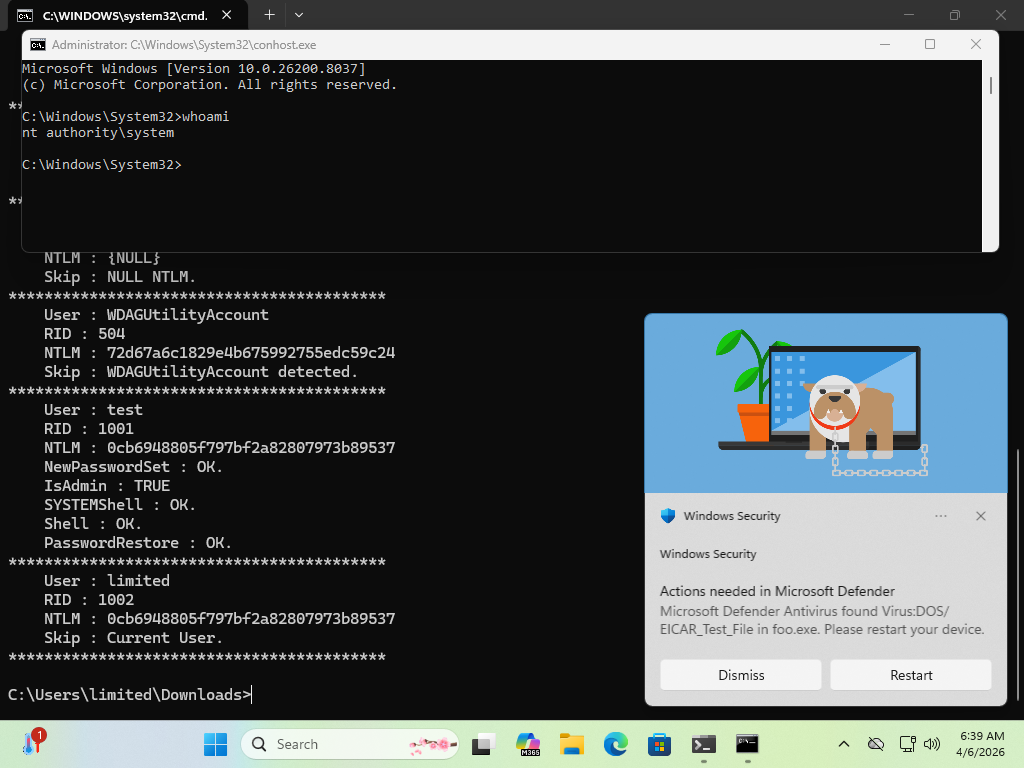
The BlueHammer zero-day exploit targets a Windows privilege escalation vulnerability, enabling threat actors to elevate standard user accounts to full SYSTEM or administrator permissions. The exploit code for this critical, unpatched software vulnerability was publicly released on GitHub by a security researcher operating under the aliases Chaotic Eclipse and Nightmare-Eclipse.
The individual was allegedly dissatisfied with how Microsoft’s Security Response Center (MSRC) handled the disclosure process, but the reason for the disclosure remains unclear.
Windows Privilege Escalation
The Windows BlueHammer zero-day exploit utilizes a local privilege escalation (LPE) technique combining a time-of-check to time-of-use (TOCTOU) error with path confusion, security analyst Will Dormann has confirmed. This mechanism grants unauthorized local attackers access to the Security Account Manager (SAM) database, which stores local password hashes.
Once attackers access this database, they can reportedly spawn a SYSTEM-privileged shell and achieve complete system compromise. “Though on the Server platform, it merely goes from non-admin to elevated admin rather than SYSTEM,” Dormann said.
Disclosure Tensions
The unprecedented release stems from the researcher's frustration with MSRC and its vulnerability disclosure procedures. The researcher specifically cited cumbersome reporting requirements, such as mandating video proof of the exploit, as a primary reason for bypassing coordinated disclosure protocols.
"Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible,” a Microsoft spokesperson commented. “We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community."
Until developers release an official patch, organizations must monitor local access closely and enforce strict credential hygiene to mitigate the threat posed by this unpatched Windows privilege escalation vulnerability.
A CISA directive last month urged organizations to harden Microsoft Intune security to mitigate critical endpoint management vulnerabilities following a cyberattack on U.S. medical giant Stryker.