APT28 DNS Hijacking Targets SOHO Router Vulnerabilities, Impacting 200 Organizations and 5,000 Consumer Devices Globally
- State-sponsored threat: Russian state-linked actor APT28 is actively exploiting SOHO router vulnerabilities to conduct a massive global espionage campaign.
- Traffic manipulation: The APT28 DNS hijacking operation redirects network traffic, enabling adversary-in-the-middle attacks and widespread credential theft.
- Widespread impact: Telemetry identified over 200 organizations and 5,000 consumer devices were compromised in this cyberespionage campaign.
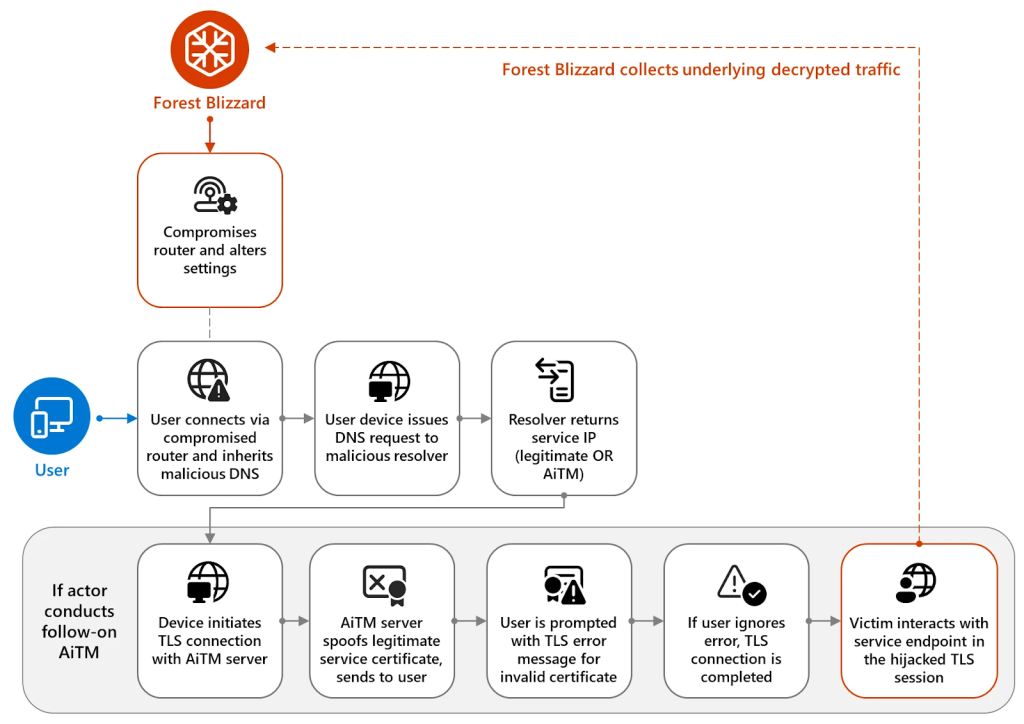
Russian state-sponsored threat actors APT28 have launched a highly coordinated global espionage campaign by compromising Small Office/Home Office (SOHO) routers. The notorious group, also tracked as Fancy Bear and Forest Blizzard, is executing sophisticated adversary-in-the-middle (AITM) attacks to steal sensitive credentials and monitor network communications.
Over 200 organizations and 5,000 consumer devices were affected, but Microsoft-owned assets or services were not among these.
Exploiting SOHO Router Vulnerabilities
The APT28 DNS hijacking attack methodology centers on identifying and compromising unpatched networking equipment, a recent Microsoft Threat Intelligence report revealed. Threat actors actively scan for SOHO router vulnerabilities, targeting devices with outdated firmware or default administrative credentials.
APT28 has leveraged DNS hijacking to support post-compromise AITM attacks targeting Transport Layer Security (TLS) connections on Microsoft Outlook web domains to intercept cloud-hosted content. “This is the first time Microsoft has observed Forest Blizzard using DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices,” the report added.
This APT28 technique silently redirects legitimate user traffic to malicious infrastructure controlled by the hackers. Users remain entirely unaware that their web traffic is being intercepted, allowing threat actors to harvest credentials, access communications, and deploy additional malicious payloads on connected devices.
Escalating Global Cybersecurity Risks
Remote work environments rely heavily on SOHO devices, which often lack the stringent security monitoring found in corporate networks. By co-opting these routers, APT28 effectively bypasses traditional enterprise security perimeters, integrating infected home networks into its global espionage campaign.
Microsoft urges organizations and remote workers to mitigate these vulnerabilities immediately. Network administrators must enforce strict password policies, disable remote administrative management on edge devices, and apply the latest firmware updates to prevent unauthorized DNS modifications.
February reports said that APT28, which was linked to the Russian GRU’s 85th Main Special Service Center (Unit 26165), deployed macro malware in a browser-based exfiltration operation targeting Europe. In May 2025, authorities across several countries warned of an intensifying APT28 campaign against Western firms that gathered intel on Ukraine Aid.
In April 2025, the Canadian Cybersecurity Center warned that Chinese threat actors targeted edge routers.