Apple Security Fix Defends Devices From DarkSword iOS Exploit
- iOS 18.7.7 update: Apple deployed emergency patches for older iPhones and iPads to neutralize critical vulnerabilities tied to a leaked exploitation toolkit.
- DarkSword attacks: The web-based exploit allows threat actors to extract messages, location data, and cryptocurrency simply by users visiting compromised websites.
- Device security risks: Millions of unpatched devices remain vulnerable, requiring immediate updates or the activation of Lockdown Mode to ensure data protection.
A critical Apple security fix was released for users of older iPhones and iPads. The release of iOS 18.7.7 and iPadOS 18.7.7 addresses a severe vulnerability linked to web-based intrusions that leverage a publicly leaked exploitation framework known as DarkSword.
DarkSword attacks leverage sophisticated web exploits to compromise Apple hardware running iOS versions 18.4 through 18.7.
Analyzing the DarkSword Attacks
The iOS DarkSword intrusion sequence initiates when a user visits a website hosting the malicious payload, such as a legitimate but breached domain. To mitigate these immediate device security risks, network administrators and end-users must install the iOS 18.7.7 update immediately.
While Apple previously secured its flagship iOS 26 architecture against these specific intrusion methods weeks ago, this backported update specifically targets legacy devices and users who declined the iOS 26 upgrade to avoid the controversial "liquid glass" interface.
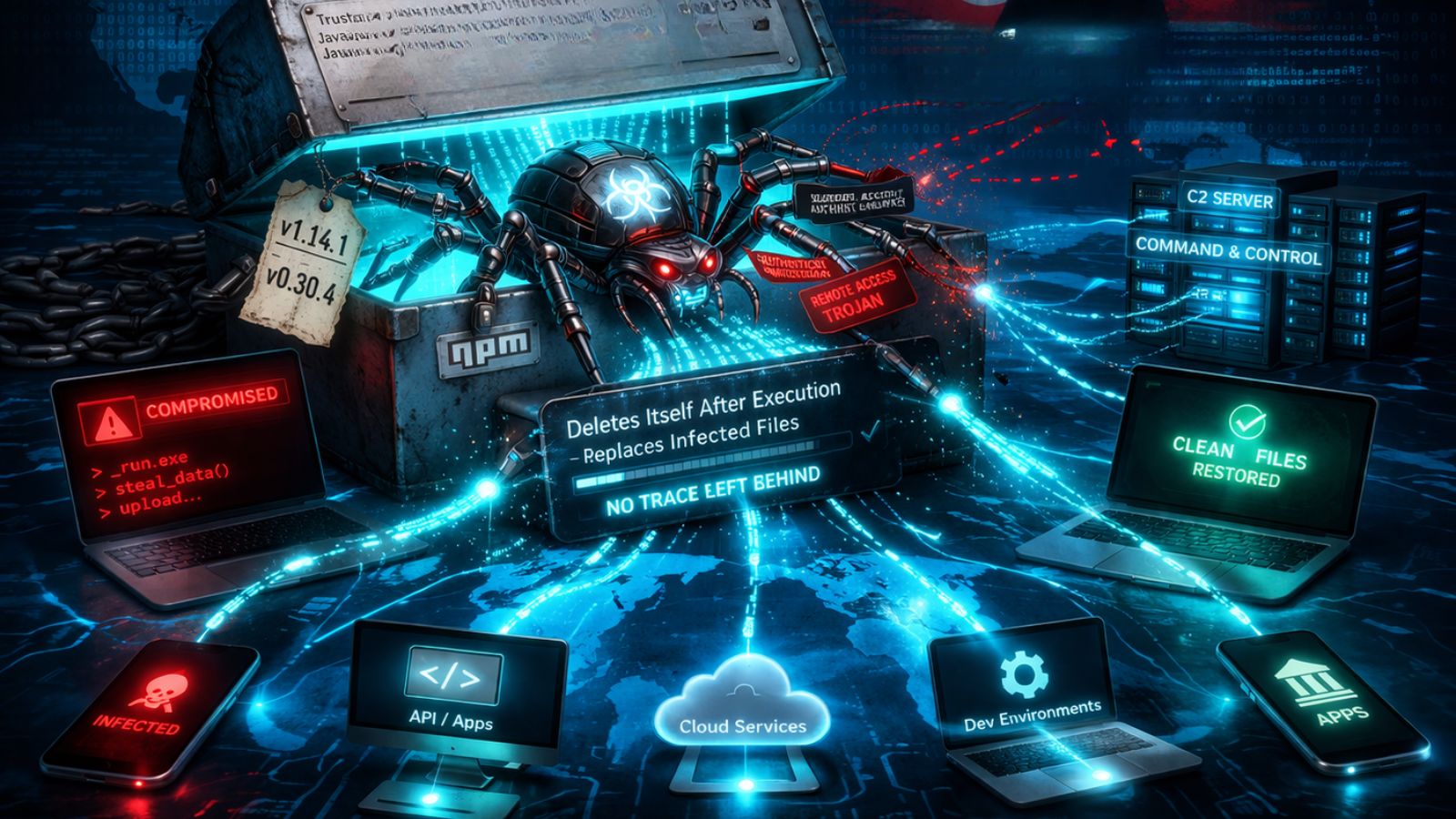
Once deployed, the DarkSword toolkit systematically extracts highly sensitive information, including encrypted messages, browser histories, precise geolocation data, and cryptocurrency wallet keys, uploading the stolen assets to remote command-and-control servers.
Mitigating Device Security Risks
Initially observed targeting high-profile individuals across China, Malaysia, Turkey, Saudi Arabia, and Ukraine, the recent public leak of the DarkSword framework allows unauthenticated attackers to target legacy systems globally. Apple confirmed that its stringent Lockdown Mode successfully neutralizes DarkSword attacks, providing a reliable failsafe for high-risk targets requiring maximum data protection.
Rocky Cole, co-founder and COO at iVerify, said that the iOS 26 public pushback, combined with a UK pushback against iOS 26.4, means that Apple cannot rely on users keeping their phones up to date with the latest build anymore,” and general population phones are currently “sitting ducks.”
Vincenzo Iozzo, CEO and Co-founder at SlashID, added that currently only 50–66% of the user base upgraded to iOS 26 and wonders “whether permanently backporting security updates to all intermediate versions would meaningfully improve overall user safety.”
Last year, a spyware campaign targeted iOS and Android devices through official App Stores.