Alleged OVHcloud Data Breach Exposes Millions of Customers and Server Infrastructure
- Massive scale claimed: An alleged OVHcloud data breach reportedly compromised over 1.5 million enterprise customers and almost 6 million active hosted websites.
- Extensive data exfiltration: The web hosting provider breach allegedly exposes website code, databases, and server configurations.
- Impacted information: The claim states that the stolen data also includes personally identifiable information.
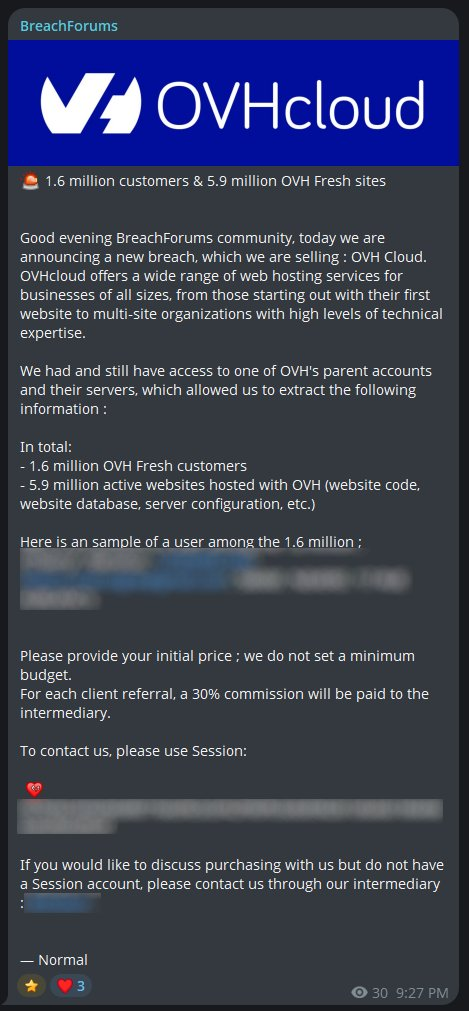
A reported OVHcloud data breach is for sale on a popular hacker forum. A user alleged the successful exfiltration of massive datasets from the major global web hosting provider, affecting approximately 1.6 million enterprise customers and 5.9 million active websites globally.
Analyzing the Web Hosting Provider Breach
According to initial security reports from March 24, 2026, a new user operating under the alias “contactbreachforums” claimed to have gained unauthorized network access to the French company by compromising an administrative parent account and its associated server infrastructure, effectively bypassing primary perimeter defenses.
The scope of the alleged data exposure is yet unknown, but the seller offered a sample to prove the dataset reportedly encompasses information such as:
- names,
- physical addresses,
- email addresses,
- telephone numbers,
- website code,
- backend databases,
- server configurations.
Was OVHcloud Hacked?
The alleged OVHcloud data breach is yet pending verification. However, the company's founder, Octave Klaba, stated that the provided data sample was not found in OVH's databases. Given that the purported proof is based on a single line of information, the claim may be false.
Evaluating the Cybersecurity Incident
Security analysts at HackManac have assigned the event an ESIX score of 7.70, reflecting the high-risk nature of the targeted global infrastructure and the extensive volume of the claimed exfiltration.
As the digital forensics investigation progresses, system administrators using the platform must enforce strict cryptographic protocols, audit server access logs, and continuously monitor for unauthorized configuration changes to mitigate potential exploitation.
In other recent news, reports say a purported Crunchyroll data breach exposed customer information via Telus. Last week, reports suggested a Divine Skins breach impacting over 105,000 League of Legends custom skin users was orchestrated by Anonymous.