Phishing Campaign Impersonating the U.S. Social Security Administration Targets 80+ Organizations
- Active threat campaign: The VENOMOUS#HELPER phishing campaign has impacted over 80 organizations, primarily targeting corporate networks located in the U.S.
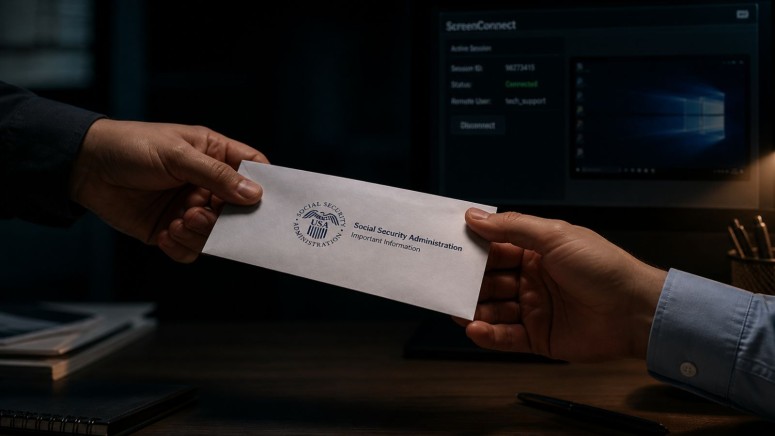
- SSA lures: Attackers utilize Social Security Administration (SSA) lures together with JWrapper-packaged SimpleHelp and ScreenConnect tools.
- Legitimate software: This RMM tool abuse silently grants threat actors unauthorized, persistent remote access.
A phishing campaign is leveraging legitimate remote management software, a self-hosted SimpleHelp 5.0.1 instance and a ScreenConnect relay, to infiltrate enterprise networks. Since April 2025, the VENOMOUS#HELPER phishing campaign has actively targeted corporate environments, successfully compromising more than 80 organizations predominantly operating within the United States.
SSA Lures and RMM Tool Abuse
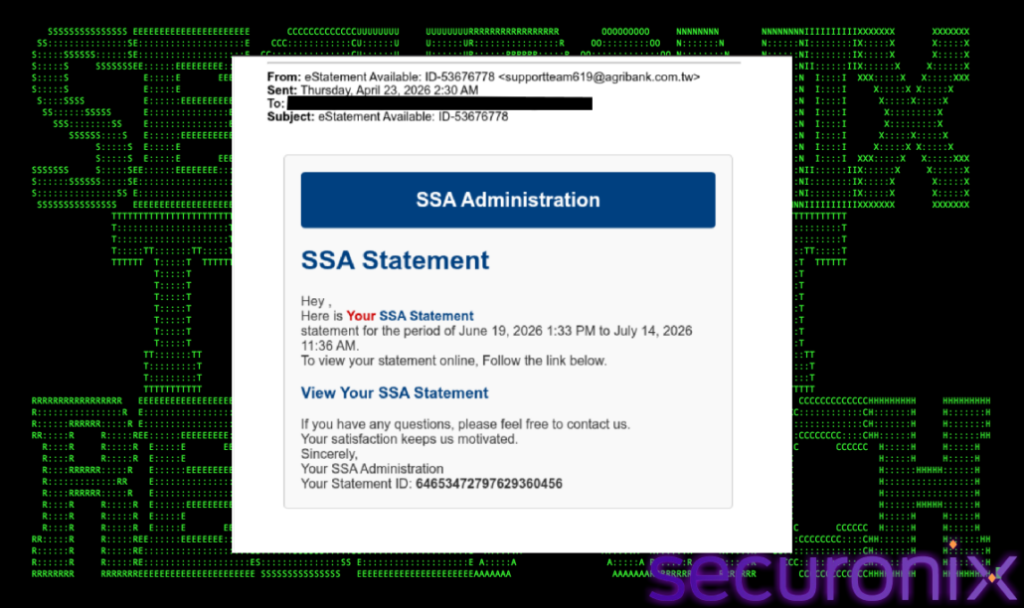
To initiate the intrusion, threat actors distribute deceptive emails using SSA-themed lures that contain a link to a compromised, legitimate Mexican business website, according to a new Securonix report.
The convincing SSA-branded verification page prompts email address confirmation before directing visitors to download an executable from a second attacker-controlled host – a weaponized subdirectory of a legitimate business site.
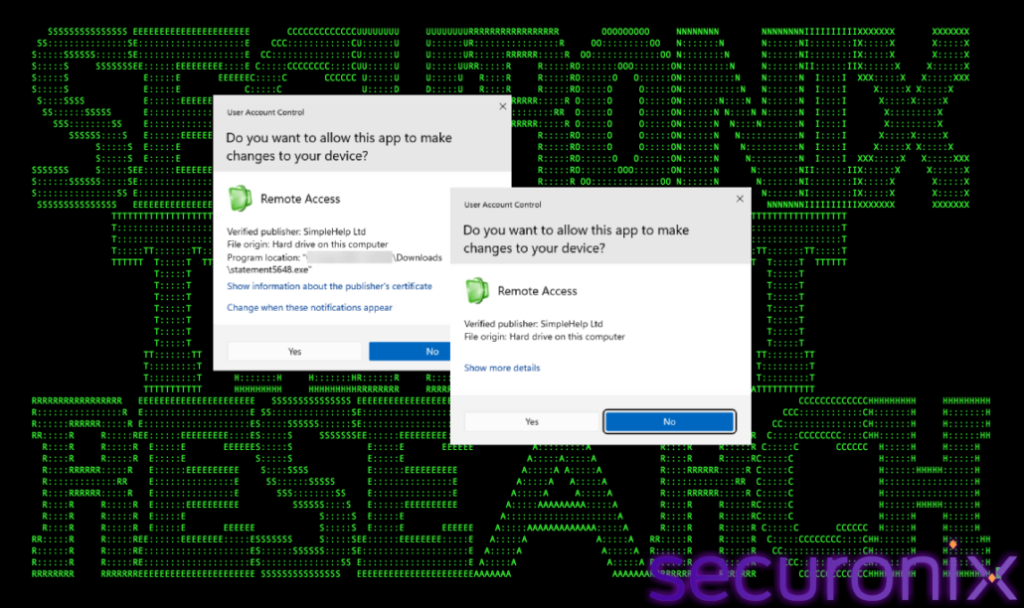
The attackers deploy legitimate Remote Monitoring and Management (RMM) software to the host machine:
- Primary RMM: SimpleHelp 5.0.1 (self-hosted, cracked build) via JWrapper.
- Secondary RMM: ConnectWise ScreenConnect (self-hosted relay, port 8041).
Deploying two independent RMM tools simultaneously creates a redundant dual-channel access architecture that survives remediation of either channel independently, establishing persistent, stealthy access.
“Securonix assesses the operator monitors the victim’s idle state and activates only when cursor position has remained static for an extended period, consistent with the victim being away from their workstation,” the report added.
Escalating Cybersecurity Threats
Securonix assesses this activity is consistent with a financially motivated Initial Access Broker (IAB) or ransomware precursor operation targeting U.S. organizations.
To defend against this ongoing operation, organizations must immediately audit their network traffic for unauthorized RMM installations and educate personnel on the indicators of SSA-themed phishing attempts to mitigate the risk of initial compromise.
This campaign appears to have been tracked previously by Sophos (tracked as STAC6405) and Red Canary independently.
In late April, users reported receiving Robinhood phishing emails, which attackers could send via an account creation flaw.