KelpDAO Crypto Theft: Lazarus Hackers Linked to $290 Million Heist
- Critical infrastructure compromise: The KelpDAO incident resulted in the unauthorized extraction of over $290 million in rsETH tokens from the decentralized finance (DeFi) protocol.
- Advanced attack methodology: Threat actors compromised verification nodes and deployed DDoS tactics to validate fraudulent cross-chain transactions across the network infrastructure.
- Nation-state attribution: Intelligence analysis links this significant security incident to the North Korean state-sponsored Lazarus Group.
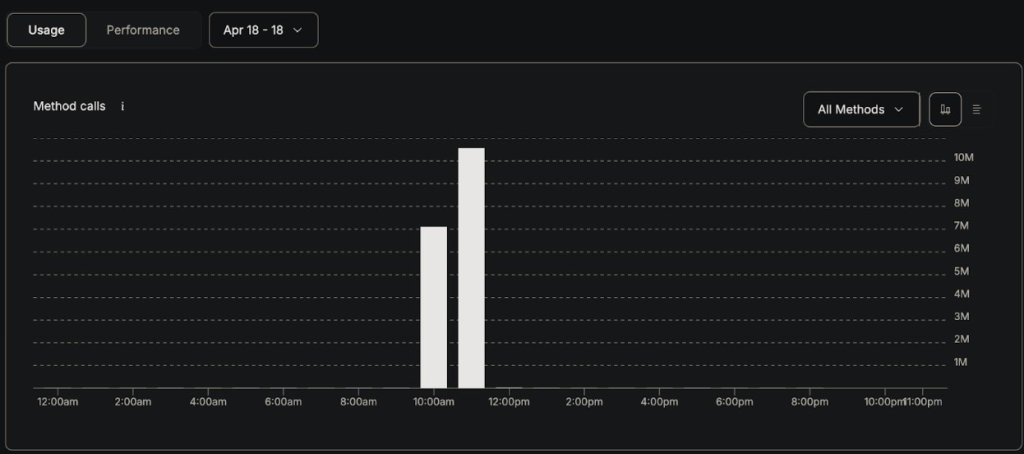
A critical DeFi security incident has compromised the KelpDAO network infrastructure. Threat actors suspected to be linked to the North Korean Lazarus Group executed a sophisticated attack on Saturday, resulting in the unauthorized extraction of approximately $290 million in cryptocurrency.
The manipulation resulted in the protocol accepting fraudulent cross-chain messages as legitimate transactions. This exploitation authorized the transfer of approximately 116,500 rsETH tokens (roughly $293 million), which passed through Tornado Cash to hide the trace.
Exploitation of Cross-Chain Verification Infrastructure
The attack vector targeted the verification layer responsible for cross-chain messaging validation. Layer Zero security analysis determined that the suspected North Korean threat actors, more specifically TraderTraitor, compromised KelpDAO RPC nodes related to the Decentralized Verifier Networks (DVNs), stating that other cross-chain assets or applications were not affected.
Concurrently, the attackers deployed a distributed denial-of-service (DDoS) campaign against the remaining operational nodes. This tactical approach forced the system to depend exclusively on the compromised infrastructure, which transmitted falsified blockchain state data to the network.
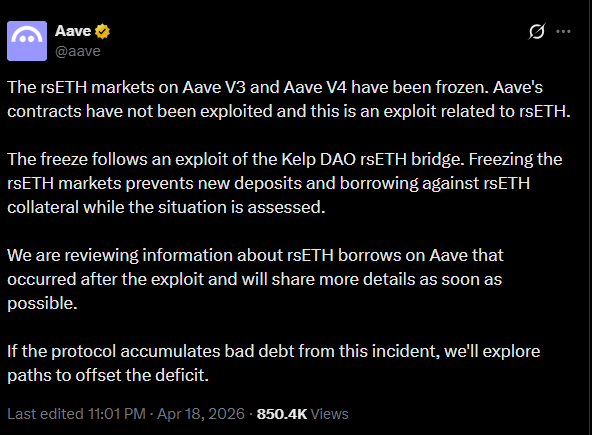
The incident necessitated the immediate suspension of rsETH smart contracts across multiple blockchain environments and compromised major lending protocol integrations, including Aave, Euler, and Compound.
Analysis of the DeFi Security Incident
KelpDAO development teams immediately engaged cybersecurity specialists to implement containment measures. LayerZero added that, despite having previously communicated best practices on DVN diversification to KelpDAO, the latter “chose to utilize a 1/1 DVN configuration.”
This incident demonstrates the critical operational vulnerabilities inherent in interconnected decentralized finance infrastructures. Early this month, an Axios supply chain attack was linked by Google to the North Korea-affiliated hackers UNC1069.
A March Resolv DeFi breach resulted in the theft of $24.5 million and the minting of $80 million uncollateralized USR.