Hackers Hired to Target Android, iCloud of Egyptian, Lebanese Journalists and Activists
- Strategic targets: A hack-for-hire group is reportedly conducting espionage against journalists, activists, and government officials across the Middle East and North Africa.
- Phishing vectors: The iCloud phishing campaign compromises Apple IDs, granting threat actors unfettered access to sensitive device backups and personal communications.
- Malware deployment: These Android spyware attacks disguise malicious payloads as popular messaging applications, silently compromising mobile endpoints.
A cyberespionage operation targeting high-profile individuals across the Middle East, North Africa, and beyond utilizes Android spyware and an extensive iCloud phishing campaign to exfiltrate critical data. Security researchers have connected these attacks to a suspected hack-for-hire group.
Access Now asserted that the hackers behind this espionage campaign work for a hack-for-hire vendor with connections to BITTER APT (also known as APT-C-08, T-APT-17, nd TA4865), a cyberespionage group with suspected ties to the Indian government, known for targeting government, military, diplomatic, and critical infrastructure sectors mostly across South Asia.
iCloud Phishing, Android Spyware Campaign
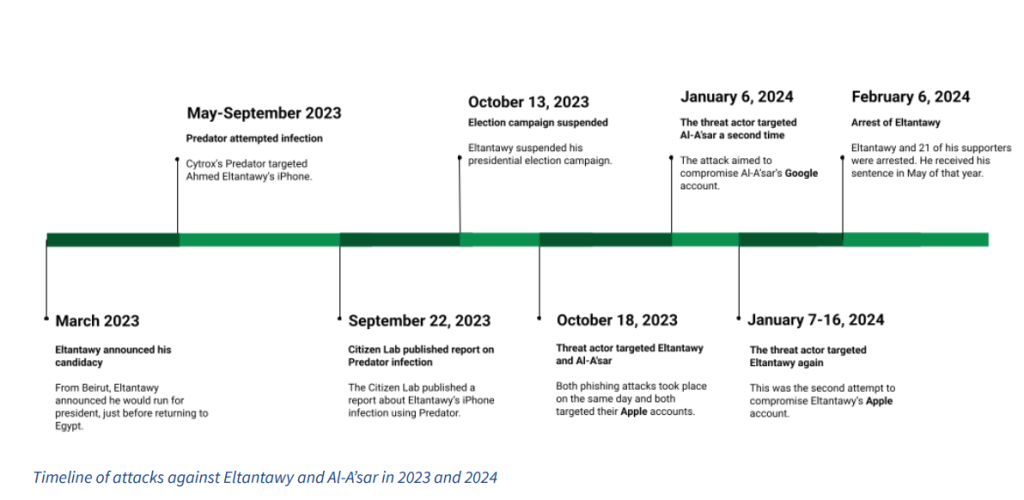
Mobile cybersecurity company Lookout and Digital rights organizations Access Now and SMEX have documented spyware and phishing attacks against two Egyptian journalists and a journalist in Lebanon from 2023 through 2025.
Lookout assessed the attacks also “likely targeted victims in Bahrain, Bahraini government entities, the UAE, Saudi Arabia, the U.K., Egyptian government entities, and potentially the United States or alumni of U.S. universities.“
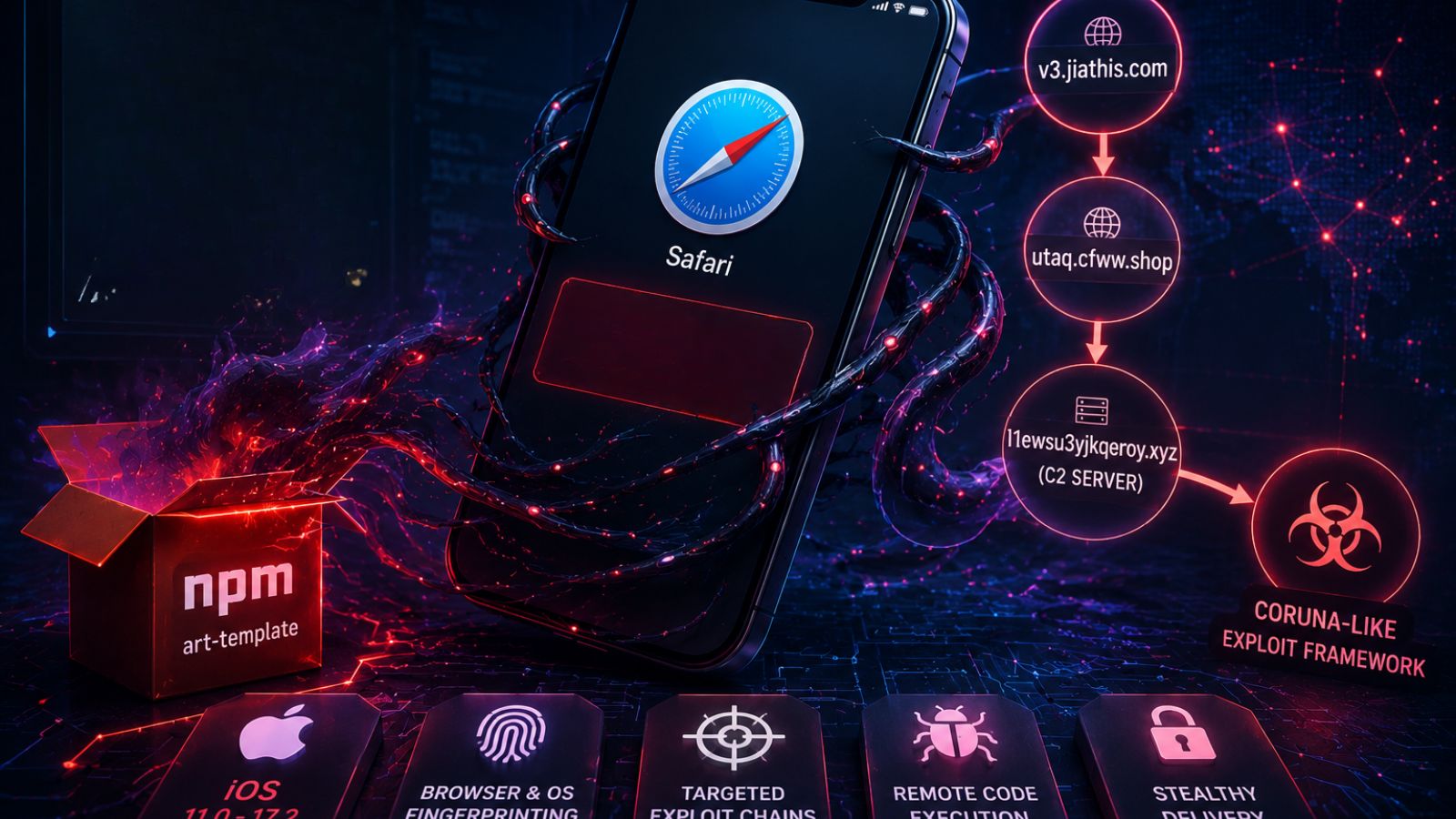
Instead of using costly zero-day exploits, the group runs a targeted iCloud phishing campaign to harvest Apple ID credentials, according to TechCrunch. By compromising iCloud authentication, attackers can covertly extract comprehensive device backups.
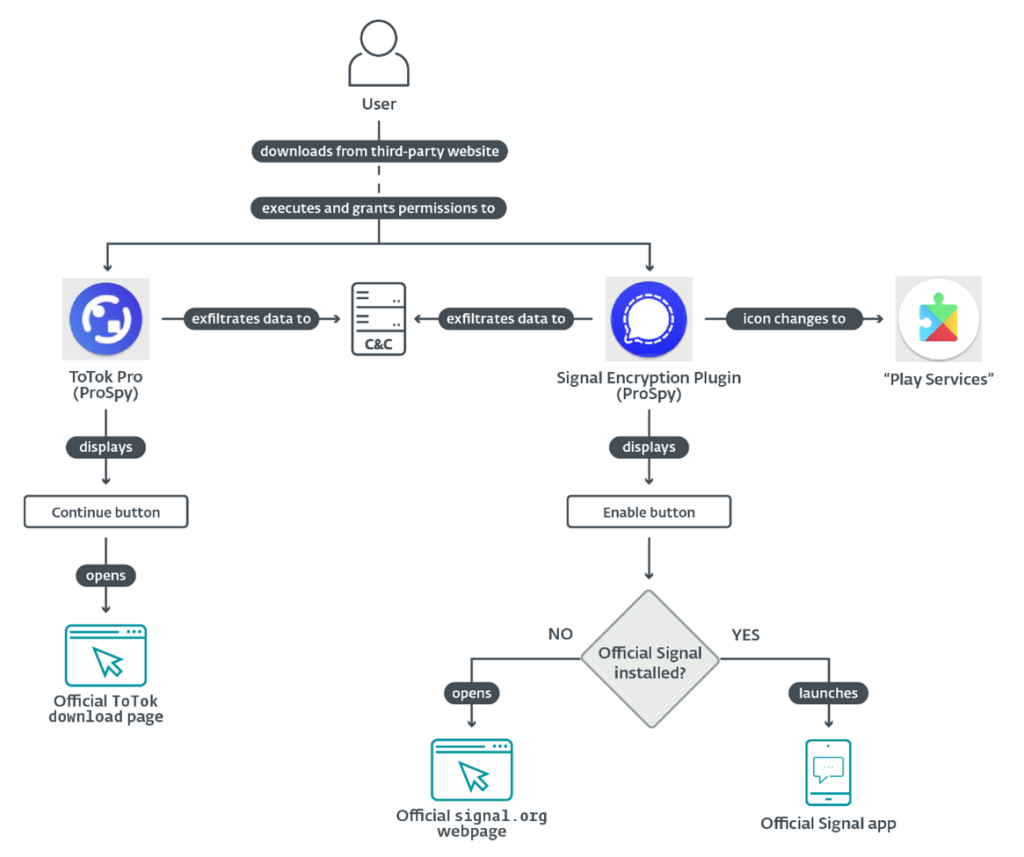
For Android users, the threat actors deploy advanced malware tracked as ProSpy. These Android spyware attacks disguise the malicious architecture in repackaged versions of popular communication software, including Zoom, Signal, WhatsApp, and regional platforms such as ToTok and Botim.
Escalating Cybersecurity Risks
The proliferation of commercial espionage entities presents unprecedented cybersecurity risks, as state-sponsored actors may leverage private contractors to maintain plausible deniability.
Early this month, security researchers reported a fake WhatsApp app targeted users in Italy with spyware. In late March, a newer version of the DarkSword iPhone exploit kit leaked on GitHub, exposing iOS users to spyware.
On the other side, Intellexa executives were sentenced in February in connection with the Predator spyware scandal, which targeted over 90 individuals in Greece, including politicians and journalists. In 2025, Paragon Spyware targeted journalists and political figures, including Italian political consultant Francesco Nicodemo.