SaaS Notification Pipeline Abuse, GitHub Phishing Campaigns, and Jira Notification Hijacking Increased, Cisco Talos Warns
- Legitimate platforms weaponized: Attackers exploit trusted SaaS notification pipelines to bypass traditional email security gateways and deliver malicious phishing payloads directly to targeted users.
- GitHub phishing campaigns: Threat actors leverage automated repository commit notifications to mask social engineering lures within standard developer alerts, neutralizing basic authentication protocols.
- Jira notification hijacking: Cybercriminals abuse collaborative invitation features to embed fraudulent project names and deceptive messages within legitimate enterprise system emails.
A critical escalation in SaaS notification pipeline abuse sees malicious actors increasingly co-opting the automated messaging infrastructure of trusted collaborative platforms to orchestrate social engineering operations via the Platform-as-a-Proxy (PaaP) technique. Attackers abuse GitHub automated notification pipelines and Jira workflow and invitation logic to generate emails from a legitimate platform's own infrastructure.
By routing malicious communications through verified platform servers, attackers successfully neutralize primary email authentication frameworks, including SPF, DKIM, and DMARC.
Exploiting Platform-as-a-Proxy Models
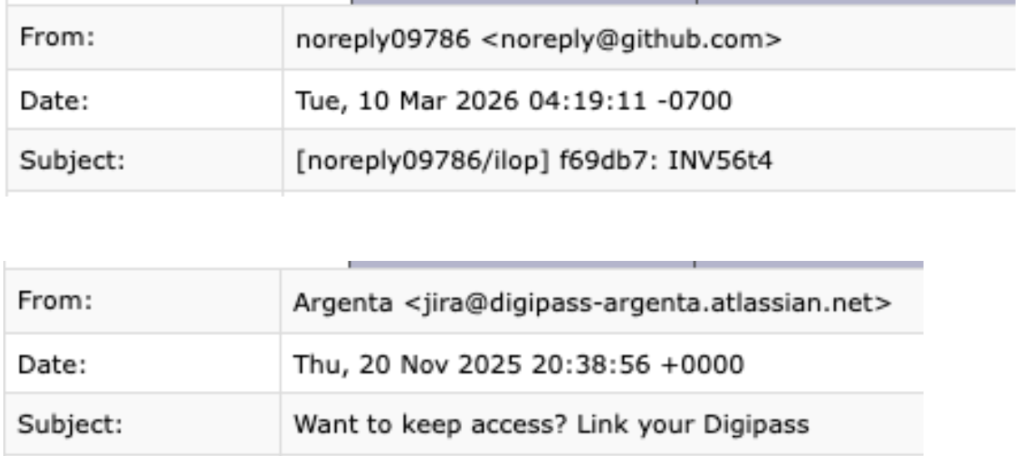
The core of this methodology relies on manipulating inherent organizational trust. In observed GitHub phishing campaigns, adversaries create unauthorized repositories and push commits containing embedded payloads, cybersecurity experts at Cisco Talos warned in a new report.
“During one campaign conducted on February 17, 2026, approximately 2.89% of the emails observed being sent from GitHub were likely associated with this abuse activity,” the report notes.
The malicious lure is strategically placed within the commit summary, ensuring it dominates the resulting automated alert. Because the alert originates from a verified source, enterprise security gateways routinely process the communication as benign.
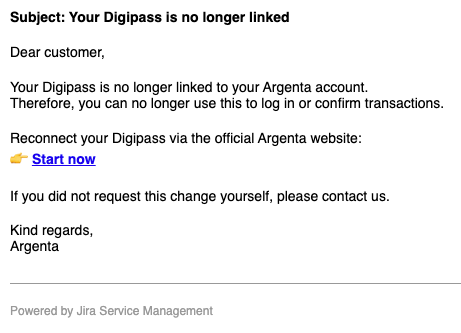
Threat actors execute similar tactics through Jira notification hijacking, exploiting the platform's collaborative invitation architecture. By manipulating customizable data fields, such as fraudulent project names or deceptive welcome messages, attackers embed malicious content within authentic Service Desk templates.
Mitigating Advanced Cybersecurity Risks
Traditional reputation-based filtering is inherently blind to platform-laundered malicious intent. Defending against these sophisticated vectors requires organizations to transition toward zero-trust architectures.
Security operations teams must focus on:
- Identity and instance-level verification.
- Upstream API-level monitoring.
- Semantic intent and behavioral profiling.
- Cognitive automation fatigue mitigation.
- Automated takedown orchestration.
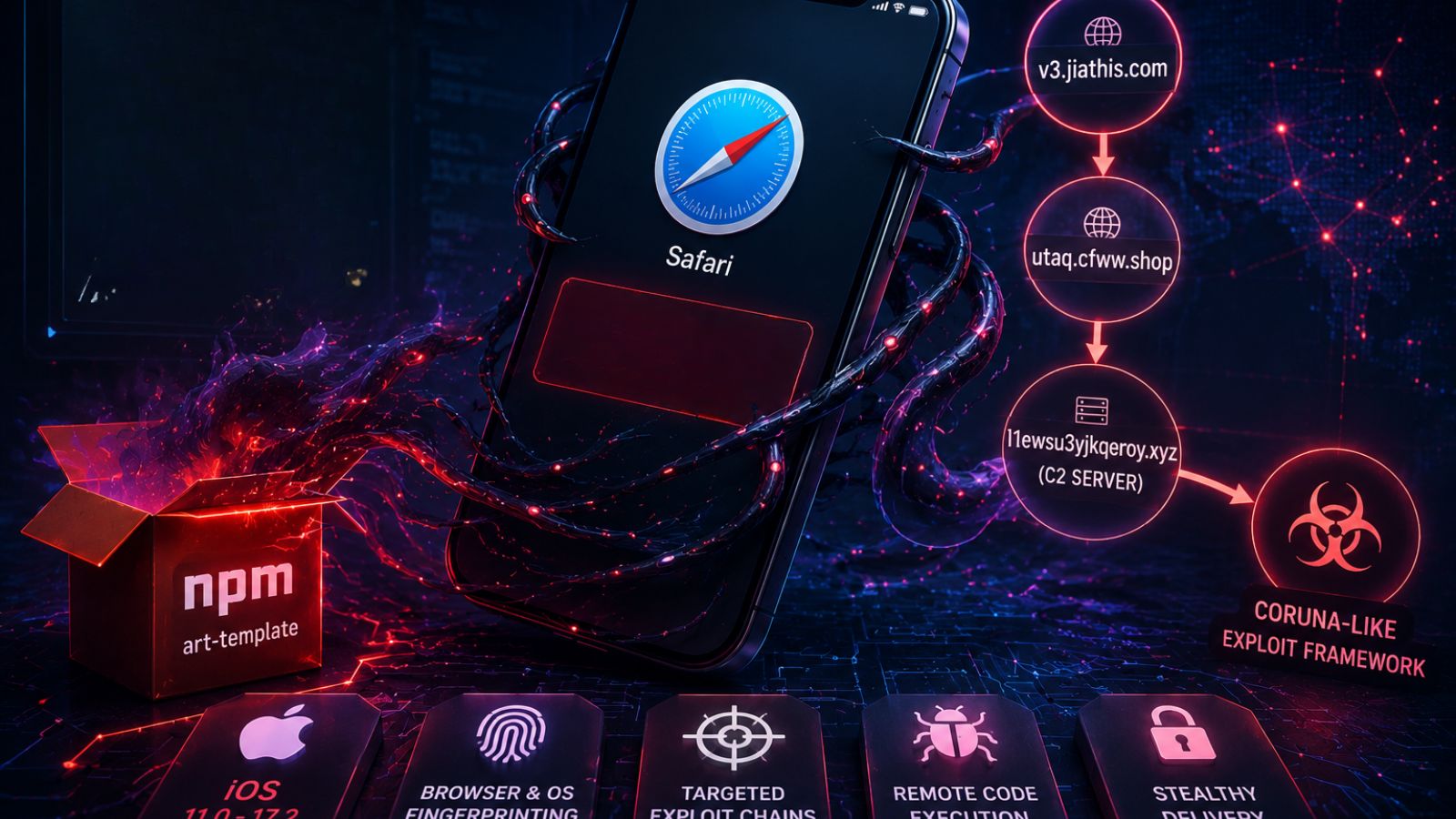
Earlier this month, FortiGuard Labs discovered DPRK cyber campaigns that execute multi-stage LNK-file attacks targeting organizations in South Korea, leveraging GitHub as Command and Control (C2) infrastructure to evade detection.