Alleged Cisco Breach Linked to Trivy Supply Chain Compromise, ShinyHunters Claims 3 Million Salesforce Records
- Alleged breach impact: Cisco faces intense scrutiny following reports of a significant internal network intrusion that may have exposed 3 million Salesforce records.
- Trivy vulnerability exploited: Attackers used the Trivy supply chain compromise to infiltrate Cisco's internal development environment, stealing AWS keys and cloning repositories.
- ShinyHunters claims: The ShinyHunters threat group issued an extortion demand, alleging the theft of millions of Salesforce records alongside cloud assets.
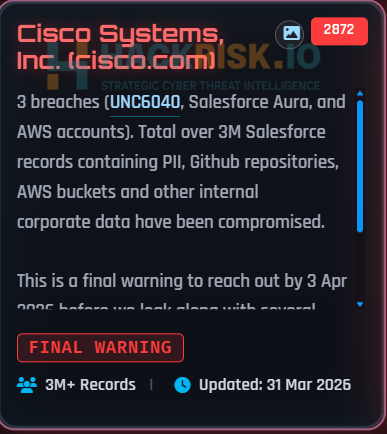
ShinyHunters claimed a breach at Cisco, asserting it gained access to over 3 million Salesforce records containing personally identifiable information (PII), GitHub repositories, AWS buckets, and other private corporate data.
Attackers reportedly used credentials exposed during the recent third-party Trivy dependency compromise to infiltrate Cisco’s internal development and build environment.
Trivy Supply Chain Compromise
The ShinyHunters extortion post that surfaced on the dark web alleges the group successfully penetrated Cisco’s internal development infrastructure, cloning over 300 GitHub repositories and extracting highly privileged AWS keys.
The threat actors claim to possess over 3 million Salesforce records, and, according to the post, the data is derived from three breaches: voice phishing via UNC6040 activitysh, Salesforce Aura, and AWS accounts.
“The breach of Cisco’s development environment following the Trivy compromise is the most substantiated part of the story, consistent with Aqua Security’s disclosure and the reported theft of AWS keys and large-scale repository cloning,” SOCRadar said.
Extended Trivy Impact
The Trivy vulnerability scanner’s poisoned component enabled unauthorized access to sensitive secrets and access tokens due to its widespread use in automated deployment workflows, exposing critical CI/CD security risks. Network administrators and security operations centers must immediately audit third-party dependencies and rotate all potentially exposed credentials.
A Mercor AI cyberattack was linked to a supply-chain exploit involving the compromise of the LiteLLM project, with Lapsus$ claiming responsibility for the breach. LiteLLM suspects the compromise originated from the Trivy dependency used in its CI/CD security scanning workflow.
Last month, ShinyHunters claimed Salesforce, Snowflake, Okta, Sony, AMD, Lastpass, and data compromise via a massive Salesforce breach, and reports revealed Interlock Ransomware exploited Cisco Firewall vulnerability CVE-2026-20131 weeks before disclosure.
In November 2025, hacking collective Scattered LAPSUS$ Hunters emerged as the new Extortion-as-a-Service cybercriminal alliance.