Suspected Iran-Nexus Password Spray Attack Targets Microsoft 365 Users in the UAE and Israel
- Targeted regions affected: A suspected Iran-nexus password spray campaign primarily impacts Microsoft 365 tenants across Israel and the UAE, specifically focusing on municipal sectors.
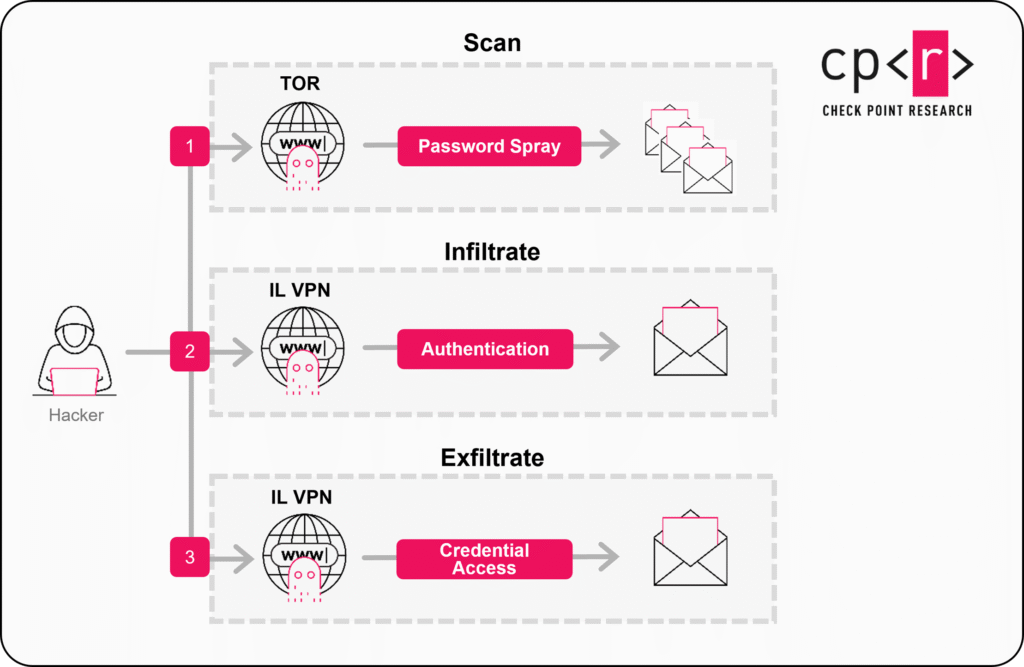
- Password spray execution: Attackers utilize Tor exit nodes and regional VPNs to execute the Microsoft 365 attack, masking their origin to bypass basic security filters.
- Data exfiltration objective: Upon discovering valid credentials, threat actors infiltrate systems to extract sensitive information.
An aggressive Microsoft 365 password spray campaign suspected to originate from Iran systematically targets cloud environments. This sophisticated operation focuses heavily on the Middle East, specifically exploiting cloud environments of government entities, municipalities, energy-sector organizations, and private-sector companies across Israel and the United Arab Emirates (UAE) to gain unauthorized access and exfiltrate sensitive data.
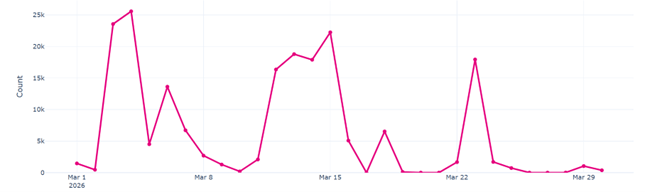
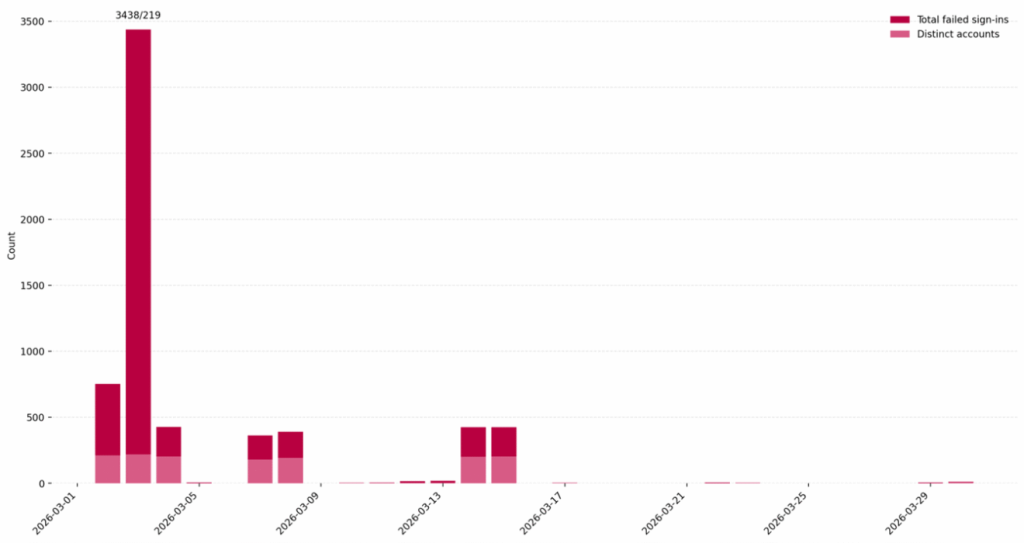
The campaign was carried out in three waves – on March 3, March 13, and March 23, 2026.
Microsoft 365 Attack Vector
This Microsoft 365 attack leverages distributed password spraying across thousands of users simultaneously, unlike traditional brute-force methods that trigger account lockouts rapidly, according to Check Point Research (CPR) cybersecurity researchers, who assess with moderate confidence that the activity originates from Iran.
Threat actors cycle through known weak credentials, utilizing a frequently rotating network of Tor exit nodes to evade IP-based detection. Once valid login details are identified, the attackers authenticate via commercial VPN IP addresses (Windscribe IP range 185.191.204.X or NordVPN IP range 169.150.227.X) geolocated in Israel.
This technique bypasses standard geographic access restrictions, enabling uninterrupted infiltration of municipal networks and critical infrastructure, which play a critical role in responding to missile-related physical damage. CPR noted that Iranian actors such as Peach Sandstorm and Gray Sandstorm used this method in the past for initial access and exfiltration.
The timing and precise target selection strongly indicate an objective of gathering intelligence to support broader regional kinetic operations. CPR observed some correlation between the targets of this campaign and cities that were targeted by Iran missile attacks in March.
Middle East Cybersecurity and Strategic Defense
This continuous network infiltration introduces severe operational risks, highlighting critical vulnerabilities in regional digital infrastructure. Effective password spray mitigation requires organizations to:
- Implement strict conditional access policies, explicitly blocking known Tor exit nodes and restricting unauthorized commercial VPN subnets.
- Enforce multi-factor authentication (MFA) across all tenant accounts.
- Actively monitor sign-in logs for anomalous authentication failures.
- Enable audit logs for post-compromise investigation.
In January 2026, a Microsoft 365 outage disrupted cloud services, blocking email and file access for enterprise users. In February 2025, Microsoft 365 accounts were targeted by a massive Chinese botnet password spraying attack and by Russian threat actors via device code authentication phishing.
Last month, CISA urged organizations to harden their endpoint management systems following a cyberattack on U.S. Medical Giant Stryker.
Recent Iran-related news include the FBI seizure of Handala websites and the EU sanctions on Iranian and Chinese firms for cyberattacks against European networks.