Axios Supply Chain Attack Deploys Cross-Platform RAT
- Account compromise: On March 31, 2026, an npm account compromise injected the malicious [email protected] package into Axios versions 1.14.1 and 0.30.4.
- Cross-platform RAT: The injected package successfully deployed cross-platform RAT malware, granting threat actors unauthorized access to affected development environments.
- Open-source security risks: This high-profile incident highlights critical open-source security risks, emphasizing the immediate need for strict dependency auditing and supply chain verification.
A severe Axios supply chain attack occurred on March 31, 2026, when malicious actors successfully compromised the “jasonsaayman” npm maintainer account of the most popular HTTP client library in the JavaScript ecosystem. This breach allowed the attackers to inject a malicious package, identified as [email protected], directly into Axios versions 1.14.1 and 0.30.4.
Axios Dependency RAT
StepSecurity identified two malicious versions that injected a new dependency never imported anywhere in the axios source code, but that executed a postinstall script acting as a cross-platform remote access trojan (RAT) dropper targeting macOS, Windows, and Linux.
The dropper established communication with a live command-and-control (C2) server and delivered platform-specific second-stage payloads. The cross-platform architecture significantly widens the attack surface for any software application relying on the affected Axios versions.
After execution, the malware evaded forensic detection by deleting itself and replacing its own package.json with a clean version.
The report assessed that the attack was not opportunistic, as the malicious dependency was staged 18 hours in advance. “Three separate payloads were pre-built for three operating systems. Both release branches were hit within 39 minutes,” researchers said.
Escalating Open-Source Security Risks
This Axios supply chain attack is considered one of the “most operationally sophisticated supply chain attacks ever documented against a top-10 npm package,” according to StepSecurity researchers, who have responsibly disclosed the issue to the project maintainers.
Development teams must immediately audit their dependency trees, remove the affected packages, and update their Axios implementations to secure, verified versions. If you have installed [email protected] or [email protected], assume your system is compromised. Recovery steps say users should:
- Downgrade to a clean version and pin it.
- Add an overrides block to prevent transitive resolution back to the malicious versions
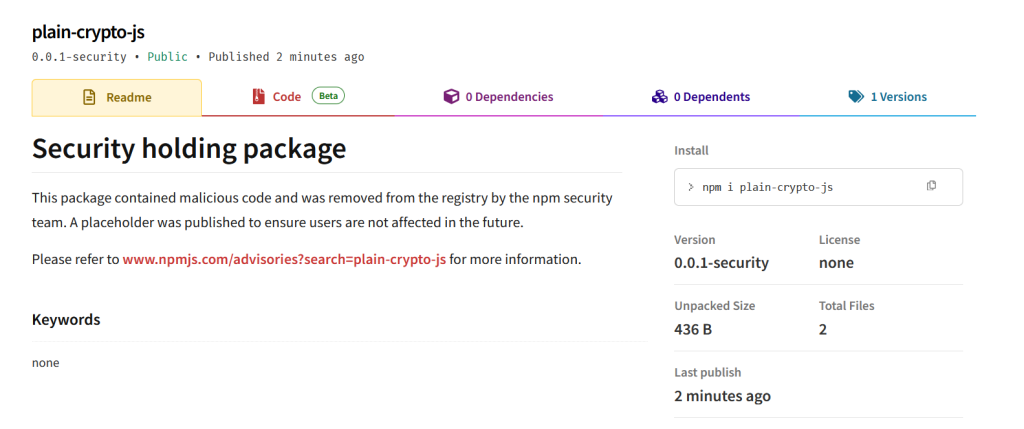
- Remove plain-crypto-js from node_modules.
- If a RAT artifact is found, rebuild from a known-good state. Rotate all credentials on any system where the malicious package ran.
- Audit CI/CD pipelines for runs that installed the affected versions.
- Use --ignore-scripts in CI/CD as a standing policy to prevent postinstall hooks from running during automated builds:
- Block C2 traffic at the network/DNS layer as a precaution on any potentially exposed system
Late last year, a WebRAT campaign targeted researchers via GitHub repositories containing fake PoC exploits for legitimate vulnerabilities, and 17 trojanized NPM packages delivered the Vidar infostealer in November 2025.