Darksword Exploit Kit Deploying iOS Spyware on iPhones, Adopted by Multiple Threat Actors
- Exploit chain exposed: The Darksword exploit kit leverages six recently patched iPhone vulnerabilities to deploy sophisticated malware on targeted devices.
- Multiple actors involved: State-sponsored espionage groups and commercial surveillance vendors utilize this framework to extract highly sensitive personal data.
- Severe device compromise: The attack chain bypasses critical security mitigations, granting attackers arbitrary code execution and escalating severe cybersecurity risks.
The Darksword exploit kit, a highly sophisticated attack framework, is actively targeting Apple devices. By exploiting a complex chain of six distinct iPhone vulnerabilities, multiple threat actors are deploying advanced iOS spyware to harvest sensitive user data.
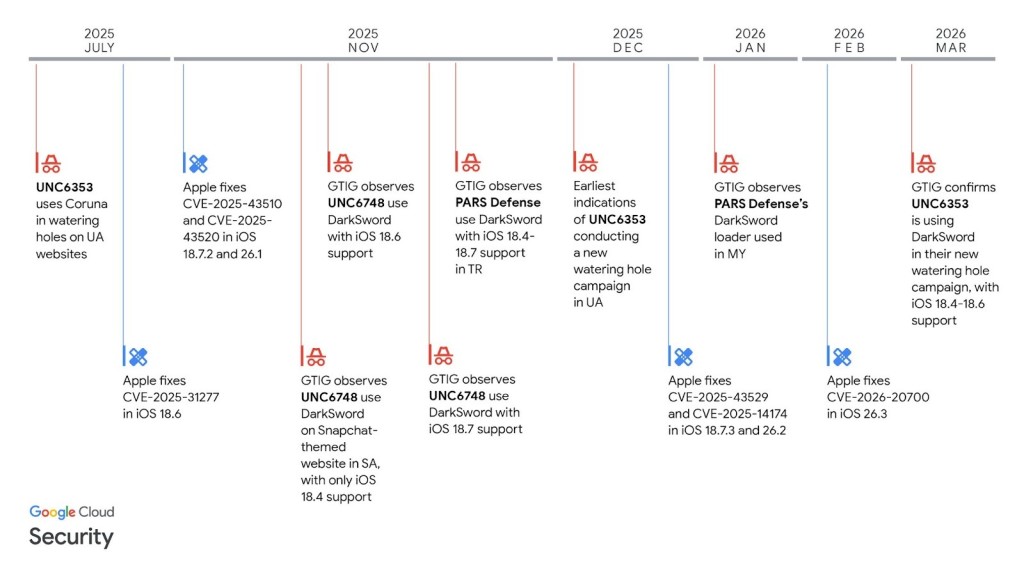
Google Threat Intelligence Group (GTIG) researchers have identified commercial surveillance vendors and suspected state-sponsored cyberespionage groups UNC6748, PARS Defense, and UNC6353 among the actors that targeted Saudi Arabia, Turkey, Malaysia, and Ukraine.
Unpacking the Exploit Attack Chain
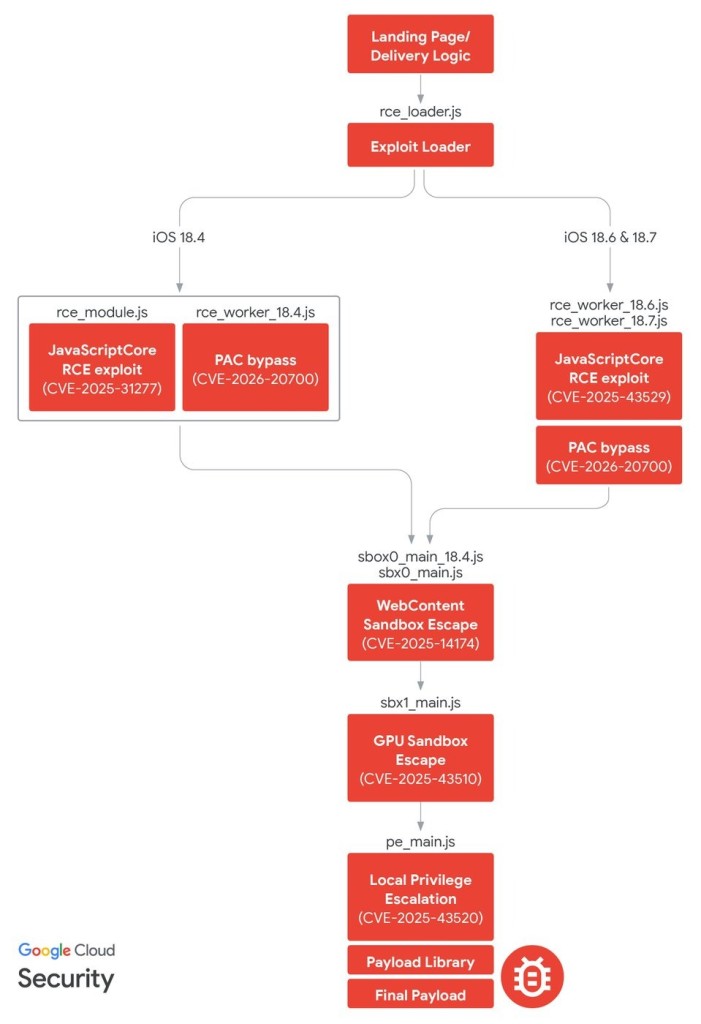
The sophisticated attack sequence initiates when a targeted user visits a malicious website. Threat actors first exploit remote code execution (RCE) flaws (specifically CVE-2025-31277 or CVE-2025-43529) to achieve arbitrary memory read and write primitives.
To bypass critical hardware mitigations like Pointer Authentication Codes (PAC), the framework exploits the now-patched CVE-2026-20700.
Safari's renderer process (known as WebContent) is tightly sandboxed. “DarkSword uses two separate sandbox escape vulnerabilities, first by pivoting out of the WebContent sandbox into the GPU process, and then by pivoting from the GPU process to mediaplaybackd,” GTIG said.
The attackers subsequently escape the sandbox via the GPU process and leverage the now-patched memory management vulnerability (CVE-2025-43510) to compromise the XNU kernel.
Once the operating system is fully compromised, the Darksword exploit kit deploys customized backdoor implants, tracked as GhostKnife, GhostSaber, or GhostBlade, depending on the specific threat group operating the infrastructure.
Expanding Cybersecurity Risks
The Darksword malicious payloads facilitate extensive iPhone data exfiltration, extracting details such as messages, location history, recordings, cryptocurrency wallet configurations, and browser cookies.
To protect against this exploit kit, administrators and individual users must immediately update their Apple devices to the latest iOS release. Apple has issued patches for all six vulnerabilities.
In November 2025, GTIG identified UNC6748 leveraging a Snapchat-themed website to target Saudi Arabian users and activity associated with the Turkish commercial surveillance vendor PARS Defense in Turkey. The security researchers also observed a new watering hole campaign by suspected Russian espionage actor UNC6353 that leveraged DarkSword to target Ukrainian users.
Earlier this month, GTIG observed that an iPhone exploit kit, dubbed Coruna, was used by multiple, unrelated threat actors, with sources saying these were leaked government tools. Last week, reports announced that U.S. contractor Trenchant was reportedly linked to Coruna.
Former Trenchant employee Peter Williams pleaded guilty and was recently sentenced to over 7 years in prison following accusations that over a 3-year period, he stole and sold at least 8 sensitive cyber-exploit components to a Russian zero-day exploit broker.