12 Hacktivist Groups Targeted 110 Organizations Globally: Almost 150 DDoS Attacks in Over 15 Countries
- Coordinated Campaign: Almost 150 hacktivist-led Distributed Denial-of-Service attacks have targeted 110 distinct organizations across 16 countries.
- Critical Sector Focus: Twelve threat groups primarily focused on disrupting entities in the government, critical infrastructure, and telecommunications sectors.
- Most Prolific: The most active actors were identified as Keymous+, DieNet, and NoName057(16), which specifically targeted the Middle East.
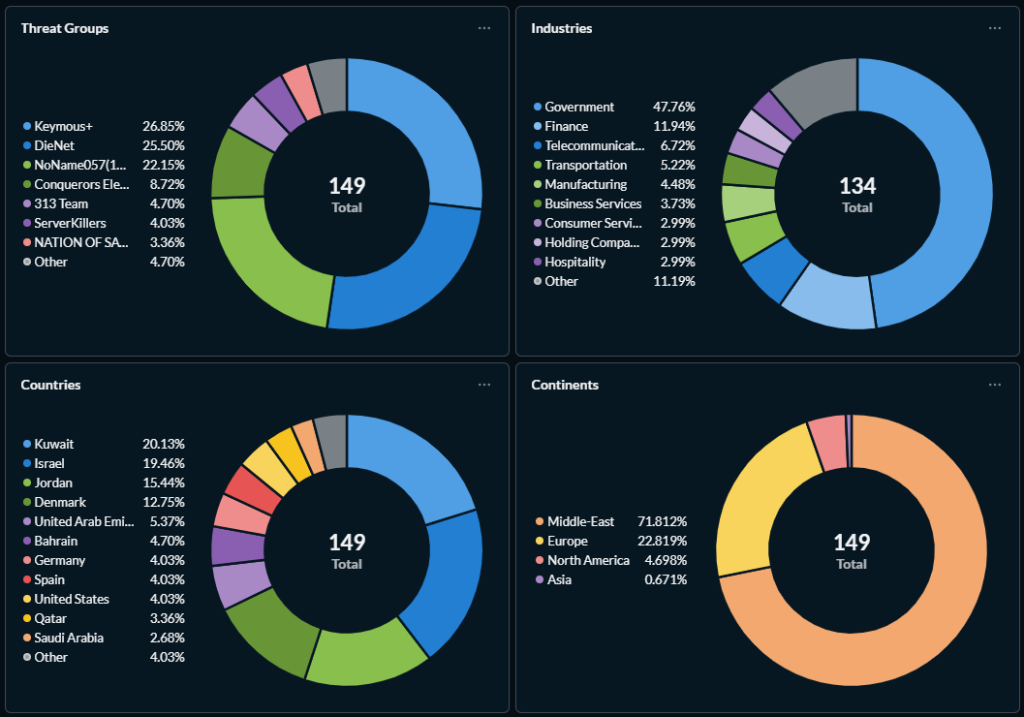
Security analysts have tracked 149 distinct hacktivist Distributed Denial-of-Service (DDoS) attacks launched by 12 threat groups against a wide array of international targets. This coordinated campaign has affected 110 organizations across 16 countries. Of these, 107 attacks targeted the Middle East.
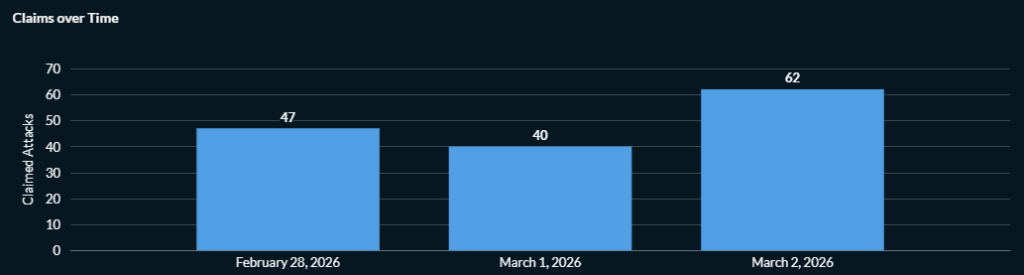
The primary objective of these operations, which occurred between February 28 and March 2, is to cause widespread service disruption and loss of availability for designated adversaries and their perceived allies.
Analysis of Critical Infrastructure Attacks
A very small number of groups were responsible for a staggering majority of all recorded global disruptions, according to a Radware report, which added that the most dominant actors globally were those involved in the Middle East campaign:
- Keymous+ (pan-Arab solidarity): The most prolific – 26.8%
- DieNet (against U.S.): A very serious secondary threat – 25.5%
- NoName057(16) (Pro-Russian): Significantly contributing to the global hacktivist DDoS activity on the two major fronts – 22.2%
“Global activity, biased largely by a majority of Middle East-targeted attacks (107 out of 149), concentrated disproportionately on public infrastructure and state-level targets, which are often prioritized for maximum public disruption and political visibility,” the report added.
Radware telemetry suggests a coordinated effort by Keymous+, DieNet, CEA, 313 Team, NOS, and NoName057(16) “to saturate” the Middle Eastern digital space.
Middle East Conflict Cyber Impact
The Middle East conflict cyber impact extends far beyond the immediate geographical theater of operations. The sectors most affected include government agencies, national infrastructure providers, and major telecommunications firms.
Network defenders must maintain a heightened state of readiness, ensuring incident response plans are in place to counter this growing threat of politically motivated digital disruption.
The report adds to previous warnings of retaliatory cyberattacks issued this week, which also mentioned DieNet, 313 Team, and NoName057(16), as the U.S. Cyber Command announced disrupting Iranian communications and sensors in a joint operation with Israel.