RedAlert Trojan Campaign Disseminates Fake Emergency App Targeting Israel via SMS Spoofing, Steals Contacts, GPS Data
- SMS Trojan: Threat actors are executing a RedAlert Trojan campaign using targeted SMS phishing to distribute a malicious Android application.
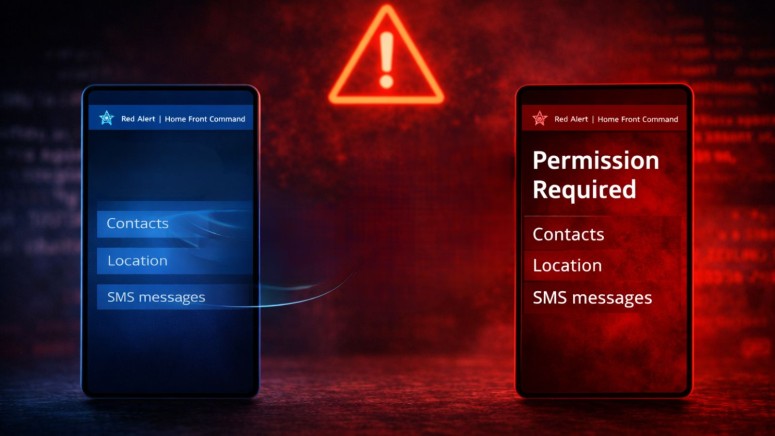
- Impersonation: The fake emergency alert app masquerades as the Israeli Home Front Command to intercept SMS messages, contact lists, and real-time GPS data.
- Operational risks: The campaign is exploiting regional conflict to track civilian locations and compromise multi-factor authentication protocols.
An advanced mobile espionage operation is actively exploiting regional instability through a highly targeted RedAlert Trojan campaign. Threat actors are utilizing SMS spoofing in Israel to deliver malicious payloads directly to civilian mobile devices, bypassing traditional network perimeters.
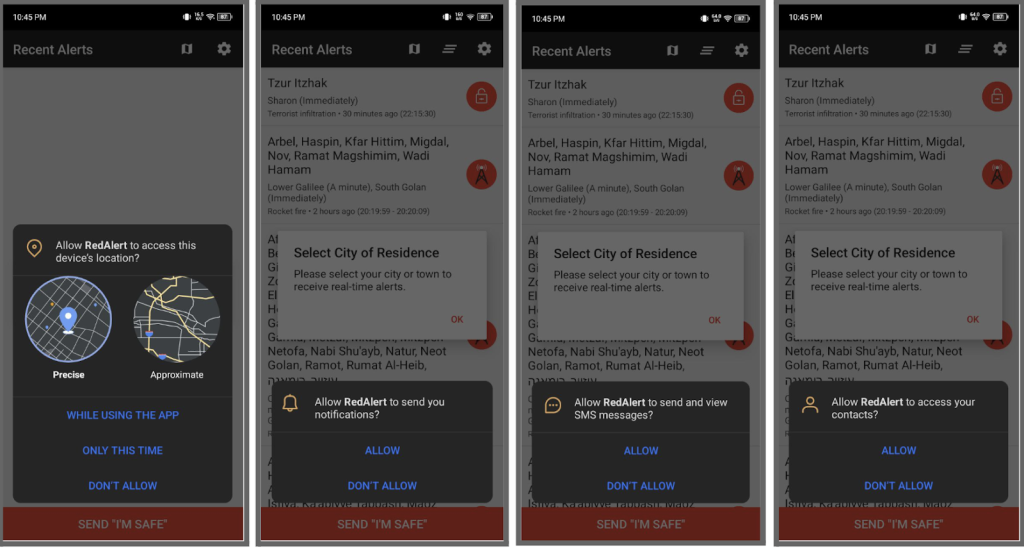
By mimicking legitimate government broadcasting channels, this operation manipulates users into downloading a fake emergency alert app under the guise of an urgent software update required for incoming rocket warnings.
Architecture of the Fake Emergency Alert App
The primary infection vector relies on instructing users to sideload an APK file outside the secure environment of the Google Play Store, according to the latest CloudSEK report. Once installed, the trojan perfectly replicates the graphical user interface of the official application.
However, the underlying architecture employs dynamic proxy hooks to spoof legacy signing certificates, successfully evading Android verification checks, and via the invoke method, makes the app appear as if it were officially installed from the Play Store instead of sideloaded.
The malware uses reflection and proxying to manipulate internal app fields, allowing it to dynamically load secondary payloads. Upon execution, the malware aggressively polls for high-level system permissions, enabling it to harvest sensitive data, including:
- Real-time GPS coordinates,
- Contact lists,
- SMS inboxes.
Mitigating Severe Cybersecurity Threats
The rapid exfiltration of real-time geospatial data and private communications presents critical cybersecurity threats. To neutralize this threat vector, security administrators must enforce strict Mobile Device Management (MDM) policies that prevent unauthorized application sideloading.
Users with compromised hardware must immediately:
- Quarantine their devices from corporate networks, Wi-Fi, and cellular data
- Navigate to Settings > Security > Device Administrators and revoke any administrative privileges granted
- Execute complete factory resets.
As the U.S. Cyber Command announced disrupting Iranian communications and sensors in a joint operation with Israel, researchers this week warned of retaliatory cyberattacks. In January, the new Devixor malware showed banking RAT and ransomware capabilities while targeting Iranian banks, crypto platforms, and payment services.