Testing Fast, Containing Faster: AI Security at Day Zero Speed
- Arambh Labs starts with the smallest viable version of an idea, launches it to a focused test audience, and seeks rapid validation.
- Garg believes in mastering the ecosystem before the tools.
- An alert becomes actionable when you add Identity and Intent.
- By layering business context over telemetry, we transform a thousand “maybes” into five “must-acts.”
- Speed should not come from rushing; it should come from eliminating manual friction.
To mark International Women’s Day, TechNadu spoke with Neha Garg, CEO and Co-Founder of Arambh Labs, to bring women’s leadership perspectives into the discussion on building AI-native security systems for speed, clarity, and control.
She brings nearly two decades of experience across AI and enterprise technology, with leadership roles at Google, Udacity, LinkedIn, and PwC.
Garg focuses on compressing the lag between detection and defense. Her approach centers on experimentation, rapid validation, and transforming overwhelming alert volumes into actionable priorities by layering identity and behavioral context over technical telemetry.
Within this broader focus on women advancing cybersecurity strategy, she reflects on execution discipline, responsible autonomy, and measurable defense.
Garg explains how reducing manual friction shortens Mean Time to Response, why autonomous remediation must include human oversight, and how “Day Zero” containment can stop threats before they escalate.
Vishwa: You’ve said you thrive in ambiguity. When the fog is thick, how do you ensure you aren’t building in the wrong direction?
Neha: In a startup, ambiguity is the default, not the exception. To keep from drifting, I anchor myself in a high-velocity experimental mindset. Instead of guessing, I lead with a strong hypothesis.
We build the smallest possible version of an idea, launch it to a concentrated test audience, and look for immediate validation. If it works, we double down. If it doesn't, we pivot before the ink is dry. It’s about having a big-picture vision but testing it with tiny, surgical strikes.
Vishwa: You’ve spanned engineering, product, and AI. What was the 'spark' that pushed you to leave product leadership to launch Arambh Labs?
Neha: I’ve always carried the entrepreneurial itch, but GenAI was the catalyst. We are living through a 'now or never' moment where every industry is being fundamentally disrupted. I saw a unique gap where AI’s speed could be used to solve security’s oldest problem: the lag between detection and defense.
Transitioning from leading AI products to building a company was about moving from shaping a tool to architecting a whole new standard for the industry.
Vishwa: For those pivoting into cybersecurity from other fields, what is your 'map' for navigating the learning curve?
Neha: Cybersecurity is a fascinating game of cat-and-mouse; the attackers are always trying to out-innovate you.
My advice? Master the ecosystem before the tools. Start with the big picture:
- Who are the players?
- What does the ecosystem look like?
- Why does each component exist?
Once you understand the 'why,' use GenAI to 'double-click' on the technical details.

Most importantly, don’t hide your outside experience. Coming from a different field allows you to see gaps that 'insiders' might miss. That fresh perspective isn't a weakness—it’s your competitive edge.
Vishwa: How do you transform an open-ended research question into a concrete product feature?
Neha: I look for the 'mapping' between a new capability and a persistent pain point. If a new AI model comes out, I don’t ask 'what can this do?' I ask 'how does this solve the specific problem I’m staring at today?'
It’s a transition from pure research to applied experimentation. We build fast, we fail often, and we celebrate the failures because they narrow the path to the one thing that actually works.
Vishwa: Your platform focuses on reducing noise. What specific 'signals' turn a generic alert into an actionable priority?
Neha: Noise is the enemy of security. An alert becomes truly actionable when you add Identity and Intent. It’s not just about what happened, but who did it, what they have access to, and how that behavior deviates from their normal pattern.
By layering business context over technical telemetry, we transform a thousand 'maybes' into five 'must-acts.' We focus on the alerts that represent a true breach of trust, not just a configuration quirk.
Vishwa: Customers report major reductions in 'Mean Time to Response' (MTTR). What operational shifts allow teams to move faster without cutting corners?
Neha: Speed shouldn't come from rushing; it should come from eliminating manual friction. The biggest operational shift is moving from 'investigation by hand' to 'investigation by orchestration.' When you automate the data gathering and initial triage, your human experts aren't wasting time looking for logs—they are making high-level decisions. You respond faster because the platform has already done the 'legwork' before the human even enters the loop.
Vishwa: Autonomous remediation is powerful but intimidating. What guardrails ensure humans stay in control?
Neha: We believe in 'Human-in-the-Loop' by design. While our platform is capable of fully autonomous action, we recognize that trust is built in stages. We offer a sliding scale of flexibility: for routine, low-risk steps, teams can toggle on full automation. For critical systems, we ensure the platform prepares the 'kill switch,' but a human provides the final 'go' signal. It’s about giving teams a co-pilot, not replacing the pilot.
Vishwa: You’ve mentioned containing threats before teams even see them. Which security workflows benefit most from this 'Day Zero' speed?
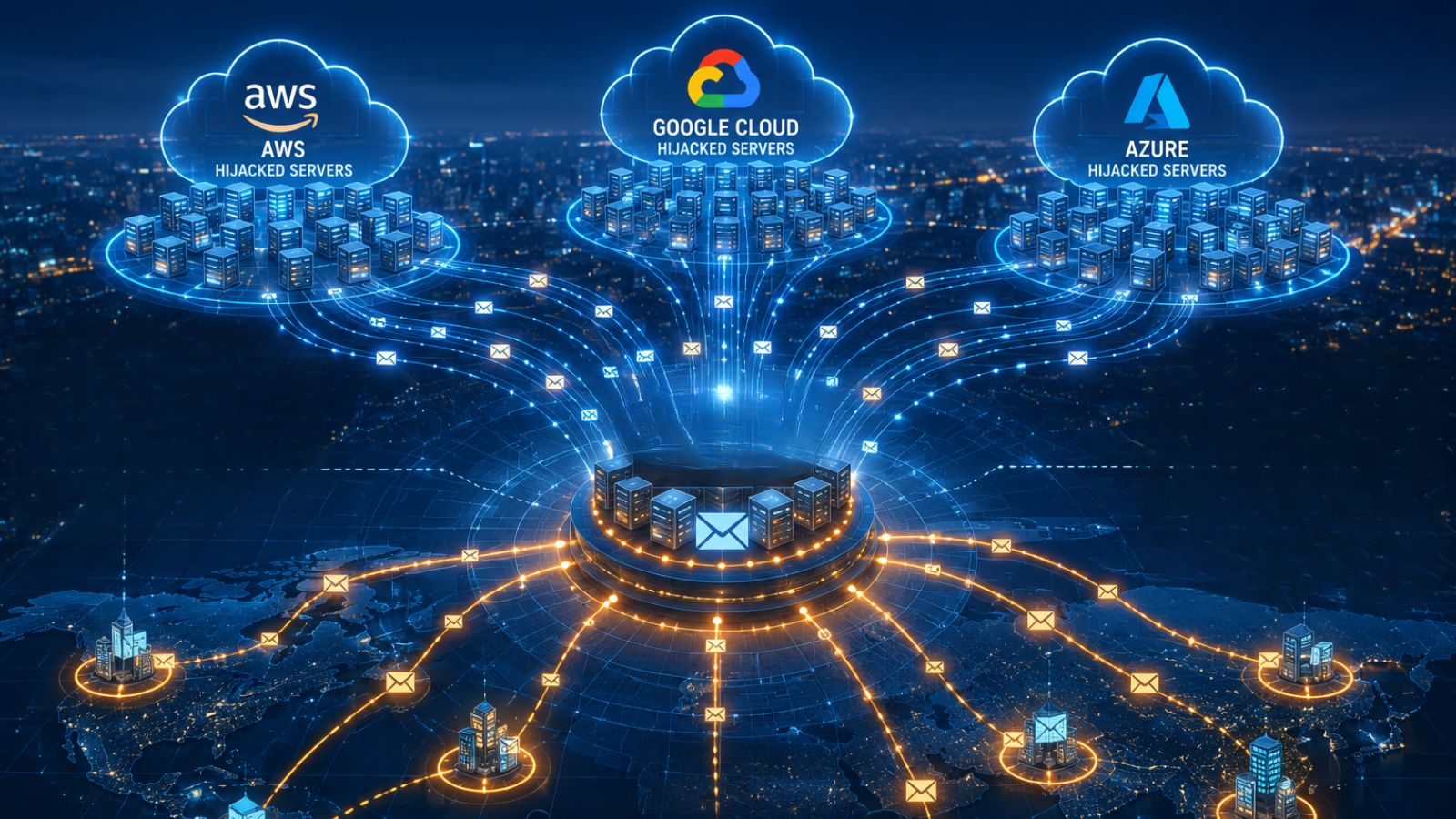
Neha: The 'Day Zero' and GenAI-driven attacks move at a pace humans can't match. The moment a new threat emerges in your industry, the first question is always: 'Is this in my environment right now?'
We automate that hunt. Our platform scans for new Indicators of Compromise (IOCs) across your entire history and environment instantly. If it finds a match, it performs basic containment—like isolating a compromised asset—before the threat can spread. We’re essentially giving teams the ability to stop the fire before the alarm even reaches the station.