UAT-10027 Leverages ‘Dohdoor’ Backdoor and Cobalt Strike Against US Education and Healthcare
- Sector Targeting: The threat actor UAT-10027 is actively targeting the U.S. education and healthcare sectors using sophisticated malware.
- Malware Deployment: The campaign utilizes a custom backdoor named "Dohdoor," which leverages DNS over HTTPS (DoH) for command and control communication.
- Payload Delivery: Attackers are deploying Cobalt Strike beacons to maintain persistence and facilitate lateral movement within compromised networks.
A new threat actor, tracked as UAT-10027, has launched a focused cyberespionage campaign against critical sectors in the U.S., including education and healthcare. The cluster deploys a custom-built backdoor dubbed Dohdoor, which is designed to evade detection by blending malicious traffic with legitimate network requests.
Cisco Talos assessed with low confidence that UAT-10027 is North Korea-nexus, based on the similarities in the tactics, techniques, and procedures (TTPs) with those of the other known North Korean APTs.
Dohdoor Backdoor Attacks Leverage DNS over HTTPS
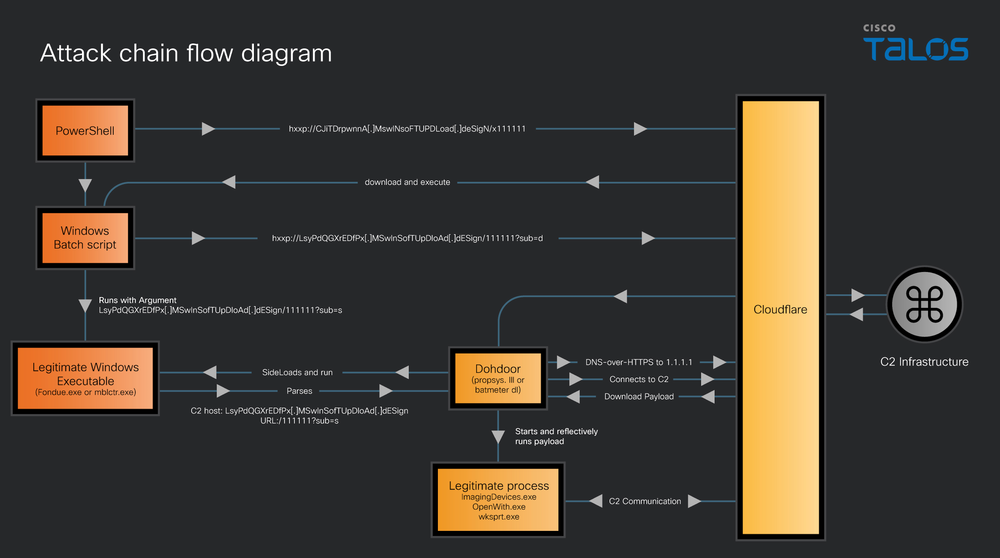
The core of this campaign involves the deployment of "Dohdoor," a sophisticated backdoor that uses DNS-over-HTTPS (DoH) for command-and-control (C2) communications behind reputable cloud services, such as Cloudflare, to enable stealth C2 communication, according to Cisco Talos intelligence.
By using DoH, Dohdoor backdoor attacks can effectively mask their traffic within standard encrypted DNS queries, making it difficult for traditional network security monitoring tools to distinguish malicious from benign activity. Once established, the backdoor facilitates the delivery and execution of additional payloads, potentially leveraging a Cobalt Strike beacon.
Dohdoor, sideloaded via misused various living-off-the-land executables (LOLBins), shows similarities with Lazarus’ Lazarloader tool.
While UAT-10027's malware shares technical overlaps with the Lazarus Group, the campaign’s sector focus deviates from the group’s typical profile of cryptocurrency and defense targeting. However, the victimology overlaps with that of other North Korean APTs, including Kimsuky.
Increasing Healthcare Sector Cyber Threats
UAT-10027’s methodology suggests a well-resourced actor capable of developing custom tooling. The combination of DoH-based communication and potential Cobalt Strike payloads indicates an intent to maintain long-term persistence for data exfiltration or future disruptive activities.
This campaign underscores the escalating cyber threats in the U.S. healthcare sector, with the University of Hawaii (UH) Cancer Center last month confirming a ransomware attack that exposed patients’ data.
This month, a Notepad++ hijacking incident involving the deployment of a backdoor was linked to a Lotus Blossom Group campaign, and researchers discovered that Chinese hackers exploited Ivanti VPN flaws, impacting almost 120 organizations.