Threat Actors Leveraged Several Commercial AI Tools to Breach 600 FortiGate Firewalls
- Widespread Breach: A single Russian-speaking threat actor compromised over 600 FortiGate firewalls across 55 countries within a five-week operational timeframe.
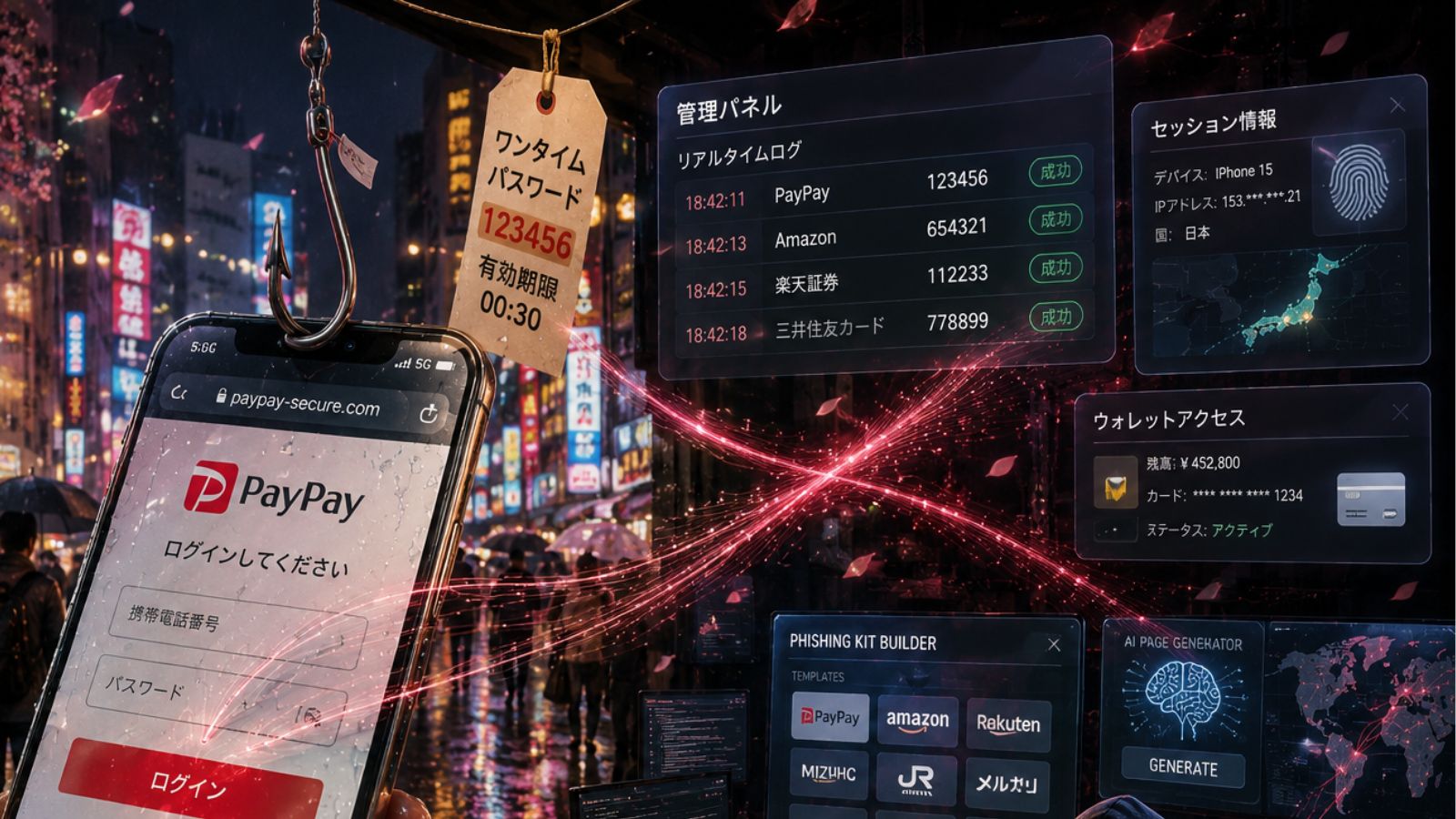
- AI-Powered Attacks: The campaign utilized multiple generative AI services to automate reconnaissance, develop custom exploitation scripts, and formulate systematic attack methodologies.
- Exploited Weaknesses: The breaches circumvented zero-day exploit requirements by targeting exposed management interfaces configured with weak credentials and lacking multi-factor authentication.
A large-scale AI-assisted hacking campaign targeted over 600 FortiGate firewalls across more than 55 countries between January and February 2026. According to Amazon Integrated Security's threat intelligence analysis, a Russian-speaking threat actor systematically targeted devices across global infrastructure, including deployments in South Asia, Latin America, and Northern Europe.
The campaign demonstrates a significant evolution in threat actor capabilities through extensive use of commercial AI services, amplifying the operational capacity of an adversary assessed as having low-to-medium technical proficiency.
Attack Methodologies and AI Integration
The threat actor did not exploit novel Fortinet vulnerabilities – instead, it capitalized on fundamental security misconfigurations. The campaign methodology involved systematic scanning for exposed FortiGate management interfaces and executing credential-based attacks using commonly reused credentials.
FortiGate configuration files contain:
- SSL-VPN user credentials with recoverable passwords
- Administrative credentials
- Complete network topology and routing information
- Firewall policies revealing internal architecture
- IPsec VPN peer configurations
After gaining VPN access to victim networks, the actor exfiltrated configuration files, which were subsequently parsed and decrypted using AI-assisted analytical tools, the report said.
The AI services were employed to generate custom reconnaissance scripts in Python and Go, automate internal network topology analysis, and develop lateral movement strategies. The attacker also specifically targeted the Veeam backup server infrastructure, including CVE-2023-27532 (information disclosure) and CVE-2024-40711 (RCE).
Cybersecurity Threat Landscape with AI Implications
This FortiGate firewall breach, carried out using commercial AI technologies, enabled the attacker to scale operational capabilities and execute technical tasks that typically require advanced expertise.
Security practitioners must implement immediate management interface access controls, enforce robust password policies with MFA, and deploy comprehensive infrastructure hardening protocols:
- FortiGate appliance audit
- Credential hygiene
- Post-exploitation detection
- Backup infrastructure hardening
This incident illustrates how generative AI is reducing technical barriers for executing sophisticated cyber operations. Last week, Google reported that state-backed hackers use Gemini AI for cyberespionage. In another case, AI-generated malware exploited the React2Shell flaw to target cloud infrastructure.