Automation Is Hiding in Plain Sight And Residential Traffic Is the Cover
- Kilmer asserts that a home IP address no longer guarantees that there’s a single person behind the activity.
- Spur Intelligence assesses that residential traffic provides cover and appears trustworthy.
- Attackers aim to make automated attacks resemble human traffic
- The problem becomes more apparent when teams analyze activity across multiple sessions.
- About mentorship, Kilmer says that being trusted with something risky or high-impact is not the same as being helped.
As part of TechNadu’s International Women’s Day campaign, Riley Kilmer, Co-Founder & Chief Innovation Officer of Spur Intelligence Corporation, examines how residential internet traffic has quietly transformed into a shield for automated abuse. Kilmer brings more than a decade of engineering experience across intelligence, threat infrastructure, and network security, including roles at the U.S. Department of Defense and Team Cymru.
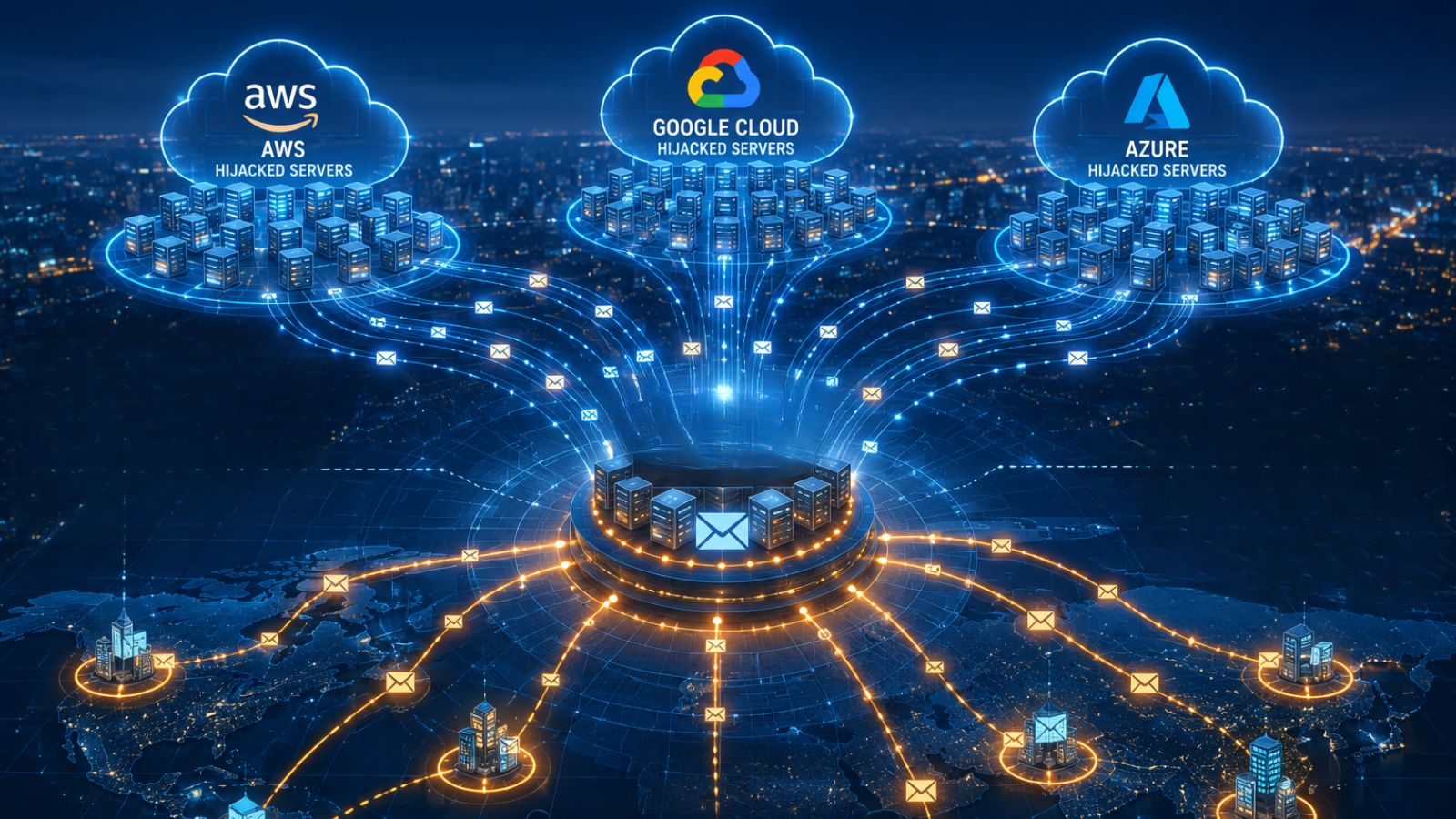
Kilmer explains that residential proxy networks are now built into everyday consumer software, devices, and SDKs. From the outside, this activity appears legitimate because it originates from real ISPs and mobile carriers. Internally, however, that same infrastructure is used to mask fraud and coordinated cyber attacks.
In this LeadHer in Security conversation, Kilmer outlines why static IP reputation and fixed behavioral baselines break, and why intent must be evaluated through evolving session patterns rather than one-time signals.
She also discusses sponsorship, reputation, and long-term resilience for women in cybersecurity, emphasizing that visibility and access, not just advice, create careers.
Vishwa: Why can residential IP traffic no longer be treated as inherently low-risk? Can you walk through why this has changed in recent years?
Riley: Residential IP traffic can’t be treated as low-risk anymore because it’s now commonly used by automated systems and fraud operations. A home IP address no longer guarantees that there’s a single person behind the activity.
This shift came from the growth of residential proxy networks built out of everyday consumer software and devices. Free apps, games, VPNs, embedded SDKs, and inexpensive hardware often include terms that allow network access to be resold quietly in the background. From the outside, that traffic still looks normal because it comes from real ISPs, mobile carriers, and familiar devices.
What security teams see today is that residential traffic provides cover. It appears trustworthy at first glance, which allows automated activity to move through systems without drawing early attention.
Vishwa: How do security teams balance blocking abusive residential traffic without disrupting legitimate consumer behavior?
Riley: Security teams take an approach of avoiding widespread blocking by focusing on the patterns of abuse that develop over time. Blocking a large percentage of residential networks, or blocking based solely on volume, can quickly disrupt the user experience.
Effective teams look at how user behavior evolves across sessions. They track how long a user stays in a session, how a user navigates workflows, whether actions occur across multiple accounts, and whether that activity lines up with how real customers typically use the service.
Understanding these patterns enables security teams to intervene in specific cases where a user has demonstrated a pattern of abuse, rather than applying blanket controls to all users. By taking this approach, security teams can limit abuse while allowing legitimate consumer traffic to continue flowing normally.
Vishwa: How do attackers blend automation into normal-looking consumer behavior? How does this blending reflect in real-world attacks?
Riley: Attackers use several techniques to make automated attacks resemble human traffic. One of the most common methods is to slow down automation so it behaves more like a real user, following expected navigation patterns and spreading actions out over time to avoid detection based on a single request or event.
When looking only at individual sessions, nothing immediately stands out. Page loads look normal, and the timing between them doesn’t warrant concern. The problem, however, becomes more apparent when teams analyze activity across multiple sessions. As teams gain broad insight, they may notice repeated actions that indicate deliberate, coordinated activity.
For example, teams may notice the same actions occurring repeatedly across different geographic locations. When that pattern repeats consistently, it’s a strong indication that the activity isn’t random and should be treated as part of a larger, directed attack.
Vishwa: Why do IP reputation and static baselines break down with residential traffic?
Riley: Those signals were never designed to handle residential traffic. Home networks don’t stay fixed. Devices move between locations, IP addresses rotate, and multiple people or systems can appear behind the same address over short periods of time. Anything based on past behavior quickly falls out of sync with what’s happening now, which allows abuse to move through on residential IPs that still look clean.
Static baselines fail for similar reasons. Regular user behavior isn’t consistent enough to support fixed thresholds. People switch devices, work different hours, and connect from other networks on different days. When teams rely too heavily on static signals, abuse often blends in and goes unnoticed because nothing crosses an obvious line.
Vishwa: What passive signals help assess intent without adding user friction?
Riley: Passive signals help teams add context without interrupting legitimate sessions. Instead of relying on users to complete CAPTCHAs, teams observe how activity behaves as it unfolds.
Examples of such passive signals include a user's consistent location over time, their network, various indicators associated with known proxy-resale applications, and session behavior that doesn’t match what would be expected for an average person.
When viewed as a set, these signals provide teams with the information needed to build confidence without disrupting users who are acting legitimately.
Vishwa: How do hybrid work and BYOD complicate trust decisions? How have these shifts changed trust assumptions for security teams?
Riley: People regularly use their personal devices to access corporate networks. An employee might use a personal phone or laptop for work while that same device participates in a proxy-resale network without their knowledge.
In practice, location and device ownership still matter, but they don’t explain everything. Once legitimate business activity is mixed with traffic generated by other users on shared residential infrastructure, it becomes much harder for security teams to judge intent solely based on traditional signals.
As a result, security teams place more emphasis on how behavior looks over time rather than relying on a single login decision. Trust is continuously evaluated, based on activity, rather than assumed up front.
Vishwa: Could you share your observations about mentorship and sponsorship in security teams?
Riley: Mentorship in security is informal and inconsistent. It tends to flow through existing relationships, which means the same people get pulled along repeatedly. Sponsorship is rarer and harder to see, but it matters more.
I’ve watched women receive advice and feedback without getting access to the work or visibility that actually changes careers. Being trusted with something risky or high-impact is different from being helped.
A lot of this comes from familiarity. People advocate for others who feel known to them. Teams improve when leaders are intentional about whom they back, and willing to make that backing visible.
Vishwa: What guidance would you like to share for women pursuing long-term careers in cybersecurity?
Riley: The cybersecurity community is small, and it has a long memory. People remember who contributes, who follows through, and who helps move the work forward. Collaboration beyond your immediate team matters more than most people expect.
Roles change often in this industry, but reputation travels. Being known for doing solid work and engaging constructively gives you resilience in a field with constant churn.
It also matters to speak up when you are challenged, especially when your position is grounded in real understanding. You don’t need to win every argument, but you should not train yourself to disappear. Over time, silence gets mistaken for agreement or lack of depth.

Setbacks are inevitable. Projects fail, teams change, and decisions get revisited. Treat those moments as part of the work rather than as verdicts on your ability. Staying in cybersecurity long-term is less about avoiding friction and more about learning how to move through it without losing confidence.