As AI Tools Spread Across Workplaces, Policy Enforcement Struggles to Keep Up
- Bahat believes risk can’t be assessed in isolation; it has to be understood first in full context.
- Anyone in the organization can use AI tools, and many new users are business users.
- Users’ understanding of security, and even of technology itself, is often limited or not up to date.
- The real challenge is explaining to teams what’s happening amid a fast-moving and chaotic environment.
- Stealth Startup evaluates that companies have policies for AI, but few can enforce them consistently
As part of TechNadu’s International Women’s Day campaign, Shahar Bahat, Founder & CEO of Stealth Startup, speaks about the fastest-growing attack surface today — everyday AI usage inside the organization.
Bahat brings product and security experience from Microsoft, Rezilion, and Unit 8200, the country’s elite military intelligence and cyber unit, into her work building security for the AI era.
Organizations have AI policies, but enforcement rarely scales. Risk cannot be judged in isolation and must be understood in context, intent, and guardrails.
Bahat moved from shaping products to carrying the weight of outcomes. She translated customer requests into urgent problems to solve, absorbed internal friction, and faced the hard shift every founder knows: when to defend the product, and when to protect the business.
In this LeadHer in Security conversation, Bahat encourages women entering cybersecurity with a simple message: go for it, you’re important, and you will figure it out.
Vishwa: What AI-related behaviors do organizations need to monitor as AI becomes part of daily work?
Shahar: AI creation has evolved significantly. In the “previous generation,” AI was primarily used for chat, answering questions, and generating text. Over the past 1.5 years, however, we’ve seen AI become deeply embedded in day-to-day work.
Today, every employee - and in many organizations, almost every role - is expected to use AI tools to work more efficiently. This shift spans all departments, from engineering to marketing and beyond.
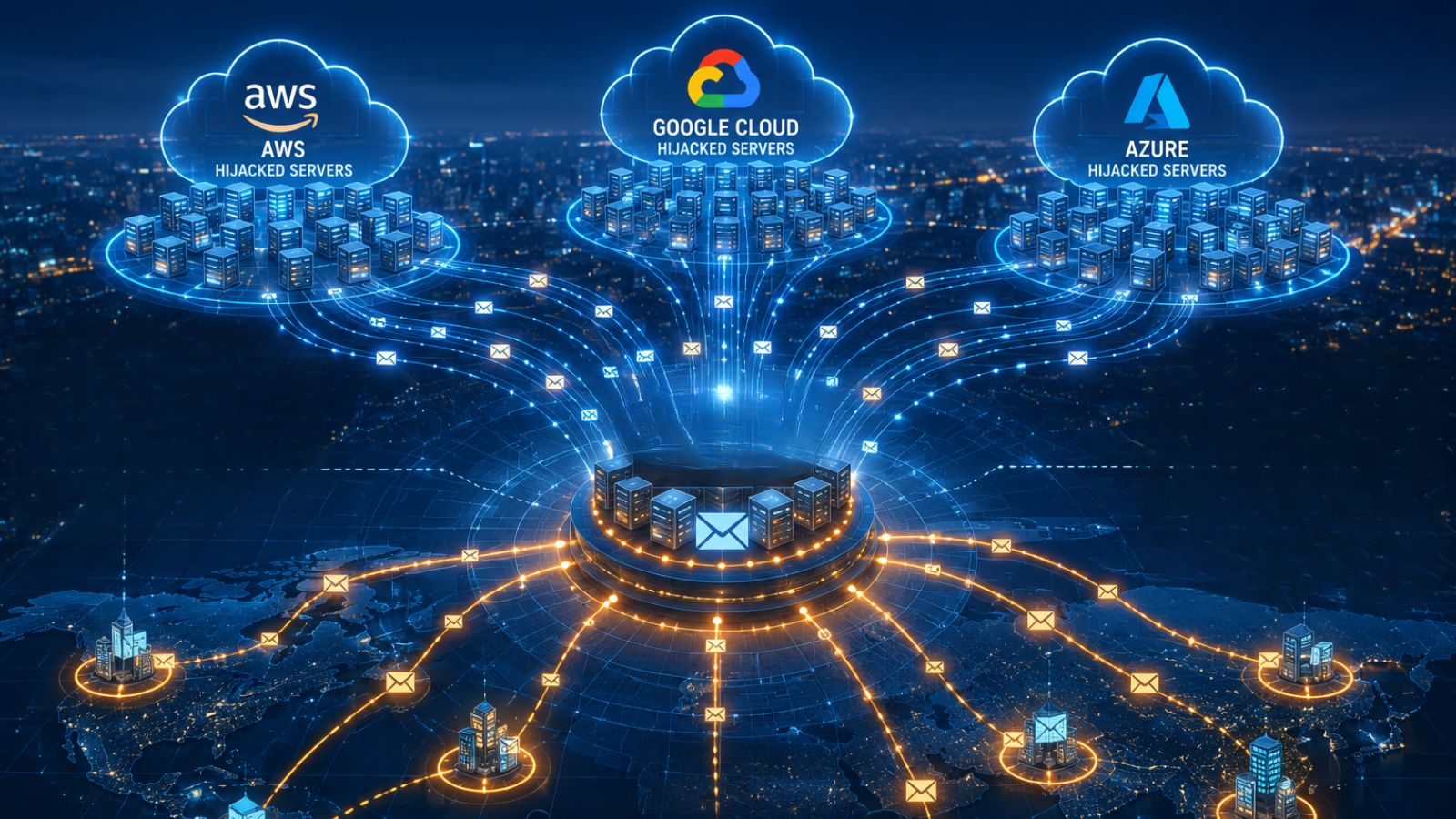
As a result, organizations are adopting new tools at an unprecedented pace, with new AI-powered applications entering the environment every day. While this creates enormous value, it also introduces an entirely new attack surface.
Vishwa: How are data signals used to detect risky AI usage across employee devices?
Shahar: We need to start by detecting AI usage in general. The concept of “risk” becomes nuanced when we talk about usage, because every employee has different intentions, capabilities, and goals.
Risk can’t be assessed in isolation - it has to be understood in context:
- What is being built?
- How?
- Why?
Some cases are more deterministic. For example, the use of clearly malicious tools is a strong signal and should be flagged immediately.
But in many other scenarios, risk is contextual. Is integration risky? It depends.
- Who is the employee?
- What was created?
- What guardrails are already in place?
Vishwa: When training employees on AI use, what challenges tend to limit behavior change?
Shahar: When training employees on AI usage, the challenges around behavior change largely depend on who the employee is. We’re now in a world where anyone in the organization can use AI tools to create - and many of these new users are business users.
Their understanding of security, and sometimes even of technology itself, is often limited or not kept up to date. This creates a significant gap between what users ask AI to do and what actually happens under the hood.
- What was created?
- What does the code really do?
- Is there additional infrastructure or ecosystem involved?
- And what happens when risk is introduced?
Another challenge is that workflows themselves are changing. Even for developers, the creation flow looks very different than it did before. The real difficulty is explaining and educating teams on what’s happening (and why) in the midst of this fast-moving, sometimes chaotic environment.
Vishwa: Where do you see gaps between organizations’ AI-related policies and how they are applied in practice? What policy changes would help?
Shahar: Enforcement is the core gap. Organizations operate at different stages of maturity and have different policies in place, but what most of them share is a lack of real enforcement. The ability to consistently monitor violations and automatically enforce policies often doesn’t truly exist.
In practice, enforcement usually degrades into emails, shared documents, or (at best) manual rules configured in existing tools. This approach doesn’t scale, isn’t sustainable, and ultimately breaks down as environments become more dynamic. That has to change.
Vishwa: As you moved from being a product manager to a founder and CEO, how did your view of leadership, and mentorship change?
Shahar: It is very interesting. I think there are some similarities in bringing different groups together around the same idea. Mission has played a big role for me - translating requests into real customer pain and turning that into a strong solution, while also creating consistent clarity and navigating internal politics.
My product background has helped me a lot in this process. It’s made me a better manager, a better CEO, a better seller, and ultimately a stronger visionary. That said, it also comes with a cost.

As a CEO, you have to recognize that there are moments when business priorities need to come before product ideals. You begin to represent the “requester” side of the organization (constantly pushing for outcomes) and the real challenge is knowing how to balance that responsibility with the deep product intuition and context you already have.
Vishwa: Looking ahead, what problem do you want to solve as a leader in cybersecurity?
Shahar: I want to change the mindset and the approach to security. Our goal is to empower security teams to be true enablers of the business - not blockers of innovation. This shift is already happening across organizations as creation moves faster and wider than ever before.
We’re here to help security teams lead that change, giving them the confidence, control, and clarity they need to move fast responsibly - and to make that transformation happen faster.
Vishwa: What advice would you give to women entering cybersecurity?
Shahar: Go for it - you’re important, and nothing should stand in your way. There’s always a solution, and you’ll figure it out. The security ecosystem needs you, and I’m here to help.