The Imperative of Software Supply Chain Security: AI-Generated Code Risks, Secure SDLC Practices, and SBOM Validation
Key Takeaways
- Compliance as a differentiator: Achieving regulatory compliance is a key indicator of an organization's speed in responding to software supply chain flaws.
- AI risk exposure: While 95% of organizations use AI for development, only 24% comprehensively evaluate IP, license, security, and quality risks on AI-generated code.
- SBOM validation gap: Only 51% of organizations always validate SBOM from external suppliers, despite validation correlating with faster flaw remediation.
The software supply chain has evolved into a primary attack surface, necessitating a shift from reactive measures to proactive governance. As development velocity increases, organizations face mounting pressure to secure their software development life cycle (SDLC) against emerging threats.
Mitigating AI-Generated Code Risks
A recent Black Duck report emphasizes that software supply chain security is a critical business enabler. Organizations that prioritize compliance controls and robust dependency management achieve significantly faster identification and remediation of critical vulnerabilities than their less mature counterparts.
The rapid adoption of artificial intelligence (AI) in development has introduced complex challenges.
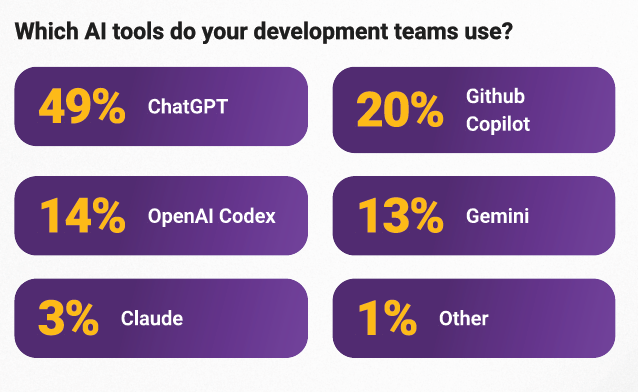
With nearly all surveyed organizations leveraging AI tools, the lack of standardized governance exposes the supply chain to AI-generated code risks, including IP infringement and security vulnerabilities.
- 62% of respondents say the software they build leverages proprietary AI/ML models and elements,
- 57% report using AI coding assistants or agents to write code.
- 49% say the software they build leverages open source AI/ML models and elements.
“By 2030, 95% of code is expected to be AI-generated,” said Saumitra Das, Vice President of Engineering at Qualys. “Due to the sheer volume of code being generated and the lack of people who reasonably understand it, we will need new architectures for dealing with the kind of issues discussed in the report.”
The study found that while security risk evaluations are common, comprehensive checks for quality and licensing are frequently overlooked.
- 76% security risk evaluations.
- 56% quality issue evaluations.
- 54% IP or license risk evaluations
- 4% no evaluations.
Only 24% apply comprehensive IP, licensing, security, and quality evaluations to AI-generated code, which Sectigo’s Jason Soroko says leaves significant blind spots in provenance, obligations, and exploitable flaws.
”AI can also amplify dependency sprawl and introduce opaque third-party components that traditional AppSec programs were not built to inventory or govern at rapid-release cadence,“ he said.
Secure SDLC Practices and SBOM Validation
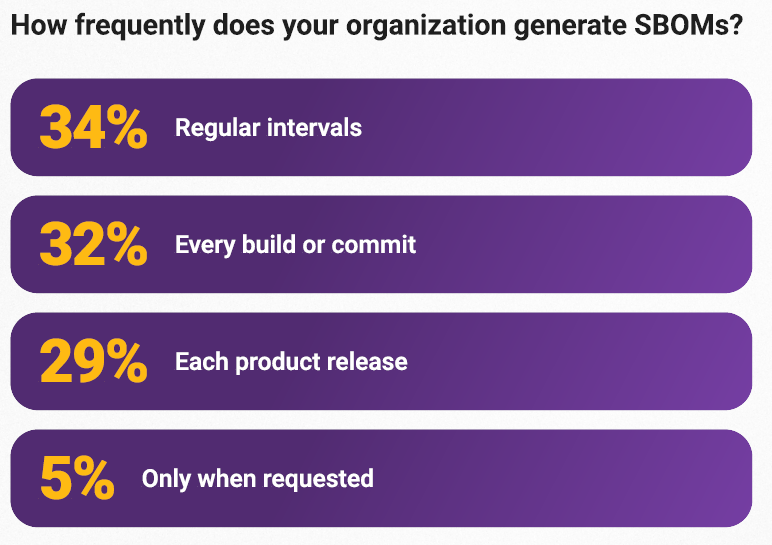
To enhance resilience, the report advocates for the widespread adoption of secure SDLC practices and automated continuous monitoring. A critical component of this strategy is Software Bill of Materials (SBOM) validation.
Data indicates that organizations that consistently validate external SBOMs are better prepared, while those that do not are less prepared. Of the 51% of organizations (275) that always validate external suppliers’ SBOM:
- 63% are very prepared to evaluate third-party software.
- 59% respond to critical software vulnerabilities within a day.
To mitigate these risks, the report recommends subjecting AI outputs to the same rigorous security and compliance checks applied to third-party and open source software, effectively treating AI as another untrusted supplier within the chain. Black Duck recommends organizations to:
- Enforce access controls, private repositories, and secure build environments.
- Automate scanning and attestation at each stage of the CI/CD process.
In a recent interview with TechNadu, Yair Finzi, CEO and Co-Founder of Nokod Security, details how GenAI amplifies risks in citizen-developed applications and how to address supply-chain concerns in an era where AI generates code faster than pipelines can handle.