When you purchase through links on our site, we may earn an affiliate commission. Here’s how it works.
Proton VPN Review 2025
Our experts have reviewed 53 VPN providers, which were put through extensive rounds of testing. To learn more about that process, here’s how we review VPNs, where we explain our criteria and our policy of being fully transparent.
Proton VPN is a versatile and reliable VPN for privacy-conscious Internet users. Introduced in 2014 by the brains behind Proton Mail and headquartered in Switzerland, a country outside the jurisdiction of the 14-Eyes Alliance, Proton VPN isn't subject to any data-sharing laws.
This VPN provider offers a strict no-logging policy, and it has been externally audited by third-party security firms, SEC Consult and Securitum. Also, Proton VPN has had no reported data leaks since its launch, rightfully deserving its place among the best VPN services overall.
In terms of security, Proton VPN offers a robust suite of features to guarantee your online safety. Proton VPN even upgraded its service with new features to help evade VPN blocks (more on that later). Also, with 8,600+ servers across 117 countries, Proton VPN boasts smooth streaming, torrenting, and gaming experiences. Its large server fleet helps avoid overcrowding, resulting in faster connection speeds.
Proton VPN also offers free and premium plans to ensure everyone can enjoy a private and well-secured online experience with their service. Below is a table with a quick summary of Proton VPN's free and paid features.
In this Proton VPN review, we put the service through various tests to determine whether it could live up to its impressively advertised features. We evaluated it based on a number of important criteria, including its speed, reputation, security and privacy, content-unblocking capabilities, pricing, customer support, and more.
We pride ourselves on remaining objective, so our reviews are always factual and fair. You can take a look at how we review VPNs if you are curious about our process. Our reviews are also consistently updated, so you’ll catch the latest and greatest on Proton VPN any time you revisit this article.
Background, Jurisdiction & Reputation
Proton VPN seems to be a reliable and trustworthy VPN service. Being based in Switzerland, it has proactive security measures regarding your privacy protection. Our Score: 10/10
Knowing where your chosen VPN comes from is more important than you think. That's because VPNs handle personal data. So, you need to make sure that no one collects it. That said, here's what you need to know about Proton VPN and its country of origin.
Where Is Proton VPN Based?
Proton VPN comes from Switzerland. That country is known for its neutral diplomatic stance and efforts to protect its citizens' privacy. In fact, the right to (digital) privacy is a part of the Swiss Federal Constitution, as highlighted below.
- Every individual has the right to have his/her data corrected or deleted. If you ask any data processing company to delete your personal data (in writing), that company must respond within 30 days. Of course, Proton VPN is considered a data processing company.
- Your IP address is considered to be your personal information. As ruled by the Federal Supreme Court of Switzerland, your IP can’t be used to trace your online whereabouts.
- There’s also the Swiss Federal Data Protection Act (DPA). This is a comprehensive set of laws dictating how personal data is processed by individuals, companies, organizations, and federal authorities. Companies based in Switzerland are forbidden from sharing private data with third parties without your explicit consent.
We should also highlight that Switzerland isn’t a member of the European Union. Also, this country isn’t a member of the 5/9/14 Eyes Alliance, which certainly sounds reassuring.
Lastly, Proton VPN is a product of Proton Technologies AG. They also own Proton Mail, a highly popular encrypted email service, alongside other services that allow their users to store and share files securely. Therefore, Proton Technologies certainly has the required knowledge when it comes to handling confidential data.
Did Proton VPN Leak Private Data in the Past?
No, Proton VPN hasn't leaked private data in the past. It has a strict no-logs policy in place to safeguard user privacy. However, back in September 2018, a privilege escalation bug was discovered in Proton VPN’s code. Still, the VPN acted before the bug was revealed publicly and patched this vulnerability.
In other words, no users were affected, and this vulnerability didn’t lead to any malicious code being sent through its secure network. Other than this report, we couldn't find anything troubling regarding Proton VPN’s practices.
We'll also add that Proton VPN goes through regular independent audits. In fact, Proton VPN just aced its most recent no-logs audit by Securitum, a highly respectable European security auditing company. This means your privacy is in solid hands. Plus, they've been busy adding features without skimping on security. It's clear that they're serious about protecting your data.
Regarding Proton VPN's sibling services, a troubling event happened in September 2021. An arrest of a climate activist in France happened after Proton Mail was forced to provide the IP address of the individual in question.
As explained by Proton Mail's CEO (Andy Yen), Proton Technologies AG is forced to comply with Swiss laws when a crime happens, which is when privacy protections are suspended.
That doesn't come as a surprise, as criminal activities are against any VPN's policies and terms of use. Still, Proton Mail did prove that it uses end-to-end encryption, as it couldn't provide any information about the accused individual's email messages.
Of course, the above applies to Proton Mail, not Proton VPN. Still, that situation acts as a reminder that when a crime happens, even the most secure VPN won't be able to give you total online anonymity.
Is Proton VPN Safe?
Yes, Proton VPN is a safe and very secure VPN provider. It routinely undergoes third-party audits to ensure safety and security.
Proton VPN offers the highest level of encryption (AES-256). For tunneling protocols, the VPN supports IKEv2, WireGuard, and OpenVPN. To further enhance security, Proton VPN has developed its custom Stealth protocol, which is now accessible on Windows, complementing its existing availability on Mac, iOS, and Android.
The 'Stealth' protocol disguises your VPN connection to bypass government censorship and VPN firewalls. These standard protocols have a strong track record and will certainly protect your Internet traffic.
In addition to its impressive security features, Proton VPN’s application code is all open source. This means anyone can examine it to confirm the apps don’t collect or store any user data. Learn more about that in our guide explaining whether Proton VPN is safe.
Supported Platforms & Devices
Proton VPN can be used on many popular platforms, with routers included. And now, it works on Web browsers as well. Our Score: 10/10
In this segment of our hands-on Proton VPN review, we'll check this VPN's supported platforms. So, take a look at the following table and then keep on reading.
With the Proton VPN Plus plan, you can connect up to 10 devices simultaneously, and it offers blazing speeds up to 10 Gbps. This means you remain protected no matter which device you switch to.
In terms of desktop platforms, there are native apps for Windows and Mac. Proton VPN also has a Linux app developed with the help of its vibrant GitHub community.
When it comes to mobile platforms, Android and iOS are supported. This was previously a major drawback as Proton VPN wasn’t available on Apple’s mobile operating system, which changed in November 2018 when Proton VPN finally reached the iOS App Store.
Additionally, Proton VPN can be installed on a range of routers. Since it uses OpenVPN, there’s a nice array of compatible routers based on DD-WRT, Tomato, and AsusWRT firmware versions (and other types of routers as well).
Also, let's not forget that Proton VPN now offers Web browser extensions as well. Just recently, this VPN launched its extensions for Firefox and Chrome, available for all free and premium users.
If you need more details, make sure to check our guide, which explains how many devices you can connect to Proton VPN at once.
Installation & Initial Configuration
You shouldn’t have a problem installing Proton VPN, even if you’re a complete beginner. The entire process can be done within minutes of your time. Our Score: 10/10
Getting started with this VPN service is a breeze. Simply download Proton VPN on your desktop or mobile device, and within a few minutes, you'll enjoy secure and private online connections.
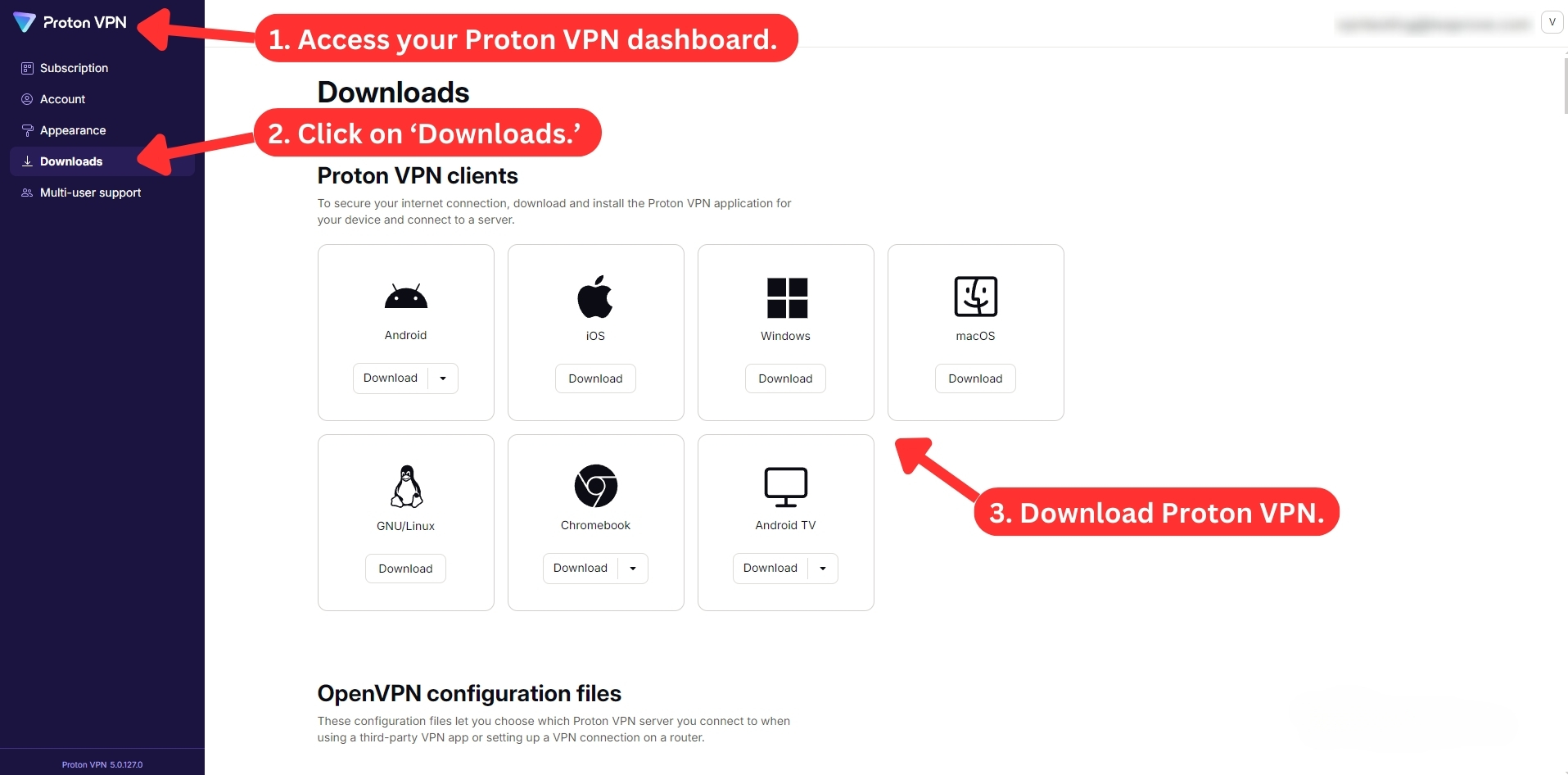
How to Download and Use Proton VPN?
To use Proton VPN, you'll first need to subscribe, get the installation file, and then install the app on your device. The entire VPN setup is quick and straightforward, taking just a few minutes.
Here's a step-by-step guide to get you started with the Proton VPN app on Windows.
- Subscribe to Proton VPN using your preferred Web browser.
- Log in to your account to access the dashboard.
- Click on the menu item called 'Downloads.'
- Select your device and download the installation file.
- Run the installation file and follow the screen prompts.
- Once installed, enter your username and password.
- Choose a server and connect. That's it!
When it comes to the actual process of installation, it should go pretty smoothly. If you've ever installed any software, you'll know what needs to be done. You won't find any bundled software here or any other annoyances.
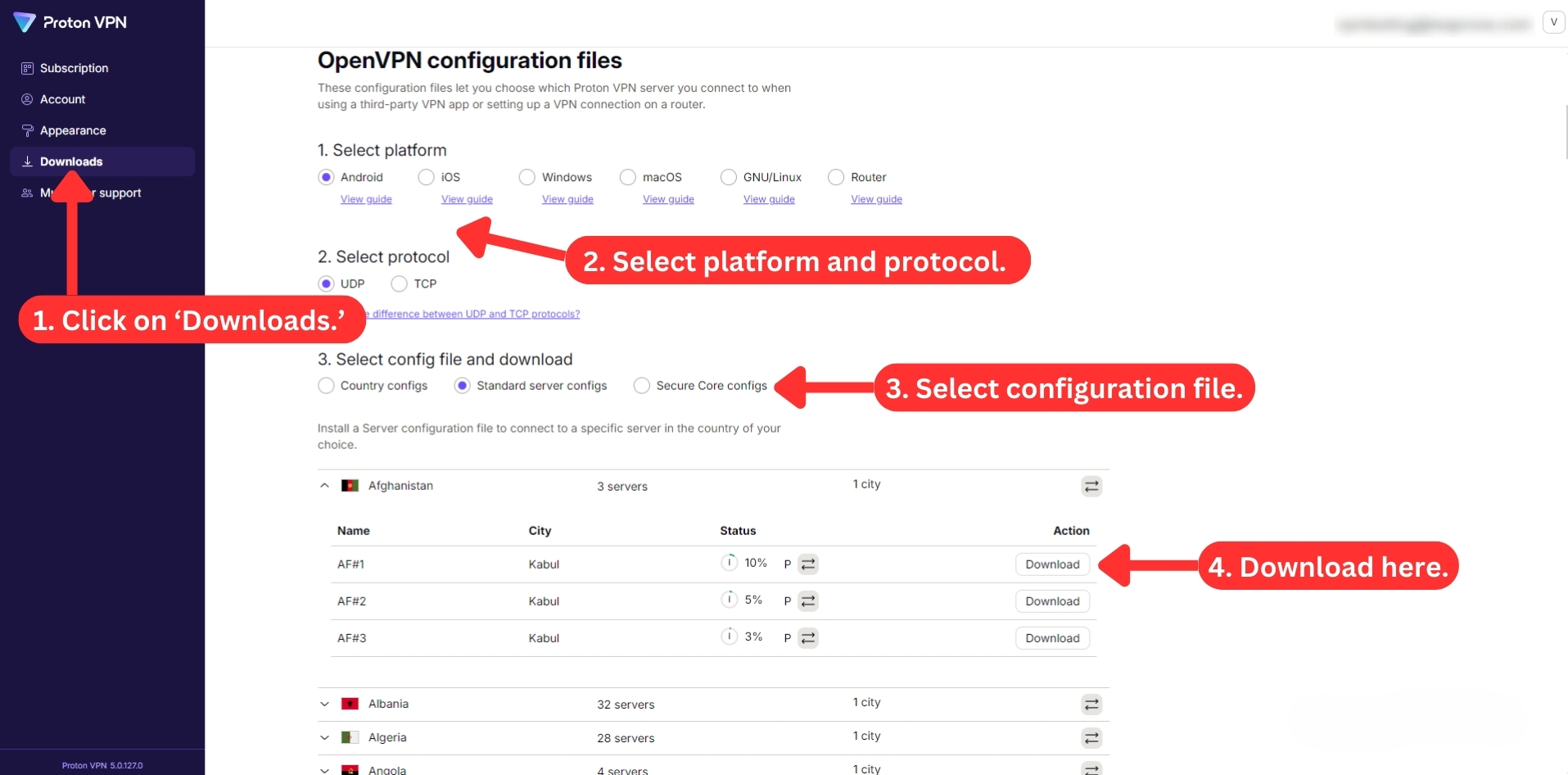
Once you log in to your account on Proton VPN's site, click on the left-placed menu item called 'Downloads.' You can see the available platforms and access or download OpenVPN configuration files - if you want to avoid installing Proton VPN's applications.
When it comes to platforms such as Android (TV), iOS, iPadOS, or Fire TV OS, installing Proton VPN is even simpler. You'll have to visit your device's app store, from where you can download and install the VPN. That's about it.
Prominent Features
Proton VPN is among the fastest VPN services right now. It has done plenty recently to improve download speeds, which are now blazingly fast. Our Score: 9/10
VPNs may seem similar on the surface. However, you should always check their features before buying a subscription. That will show you how much bang you’re getting for your buck. With that in mind, this section will highlight the most prominent Proton VPN features. Over the years, the service has developed some unique technologies that set it apart from other VPNs.
Here’s what you can expect from it:
- Full Data Leak Protection: This VPN protects your data and prevents leaks. Whether you use IPv4 or IPv6, Proton VPN has you covered with IP and DNS leak protection. This means that your online identity and activity are hidden from prying eyes. Proton VPN also uses other technologies to create a strong VPN tunnel that secures your connection.
- High-End Data Encryption: Proton VPN encrypts your data with AES-256-bit encryption, the highest standard available. This is the same encryption level used by the military and governments to safeguard their information. It also lets you choose from different protocols, such as Stealth, OpenVPN, WireGuard, or IKEv2, depending on your preferences and needs.
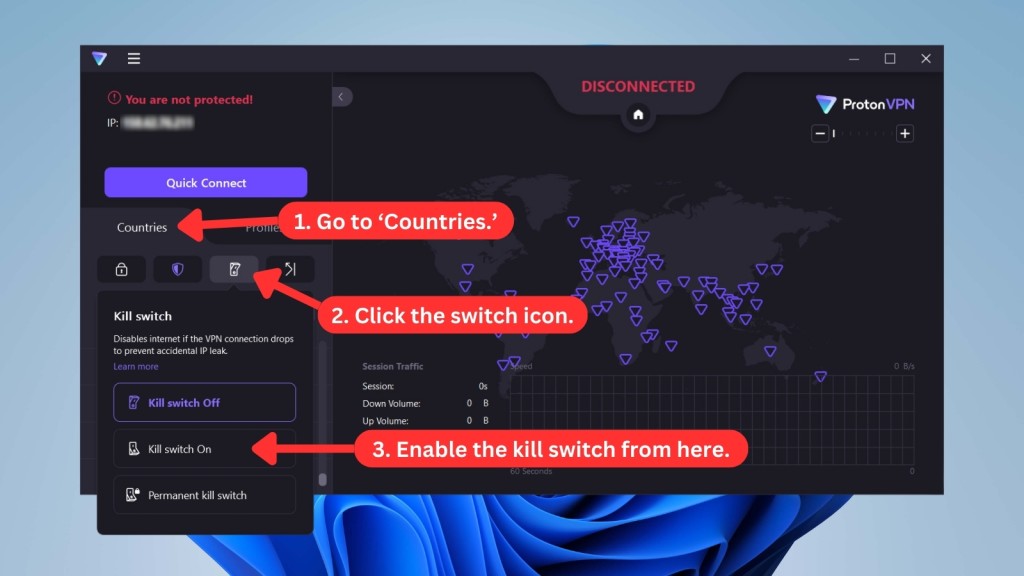
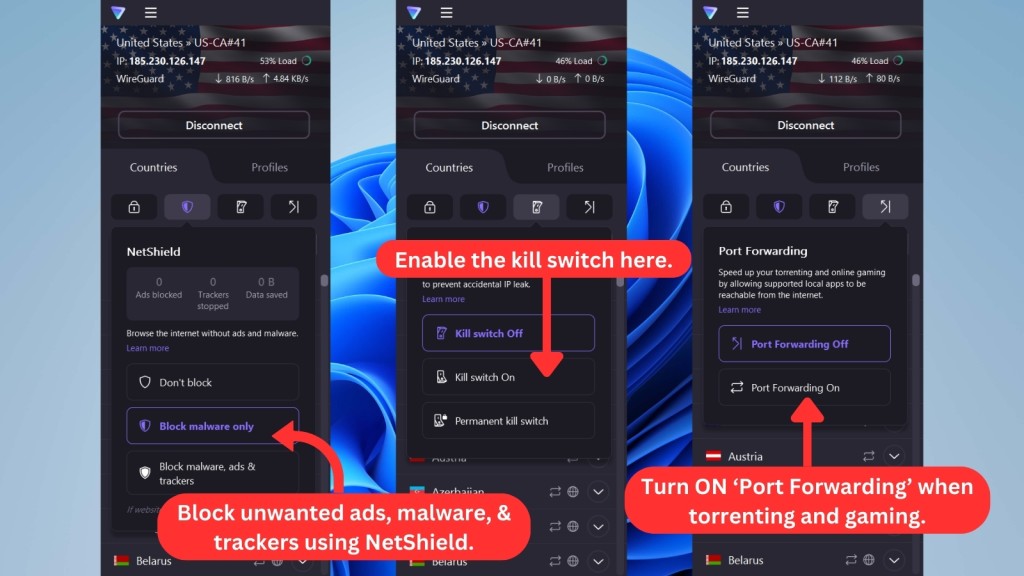
- Kill Switch: In addition, Proton VPN has a built-in kill switch that automatically stops your Web traffic if your VPN connection drops unexpectedly. This way, you don't have to worry about exposing your data or location. The kill switch is available on Windows, macOS, Linux, iOS/iPadOS, and Android devices.
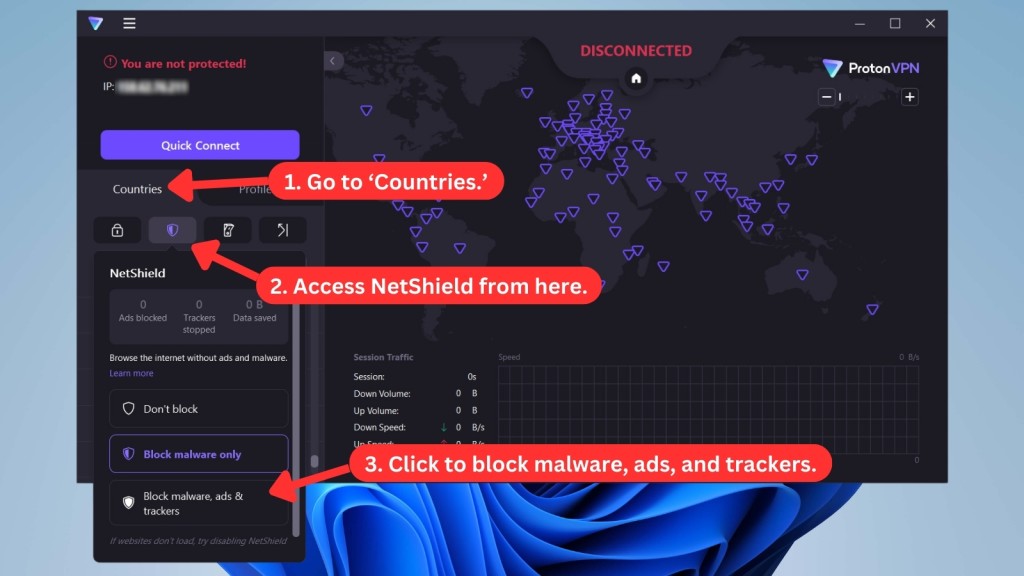
- NetShield: One of the newest features of Proton VPN is NetShield, a set of tools that block trackers, ads, and malware across your entire device. It's available on all supported apps. You can also choose from different levels of protection, depending on how much you want to filter out unwanted content.
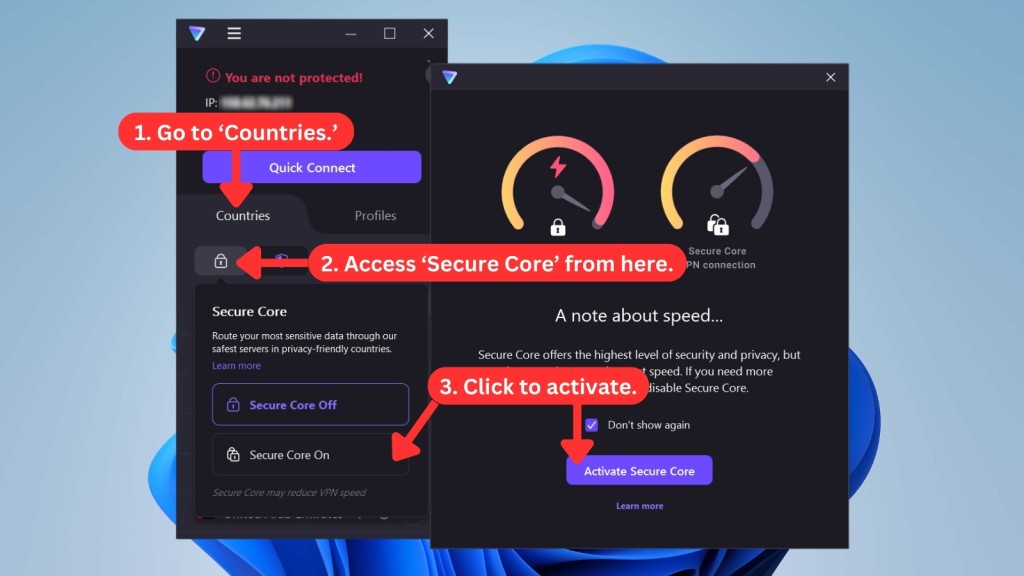
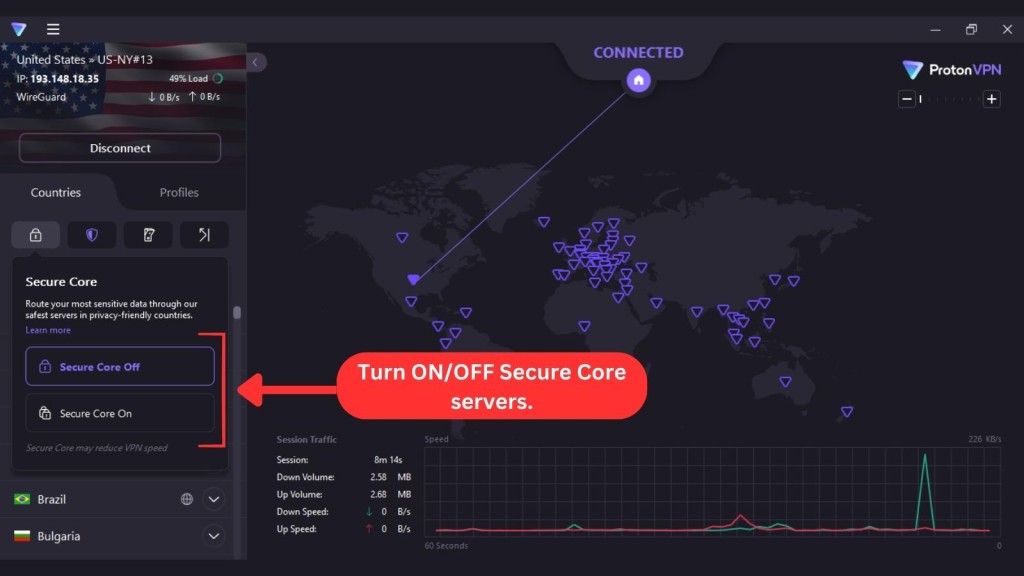
- Secure Core: This is Proton VPN's double-hop feature, which is available across all supported apps. It’s a system of servers in countries with strong privacy laws. This feature routes your traffic through an extra server before leaving Proton VPN's network. This way, no one can trace your online activity or location. However, it also slows down your connection speed since data travels through two servers instead of one.
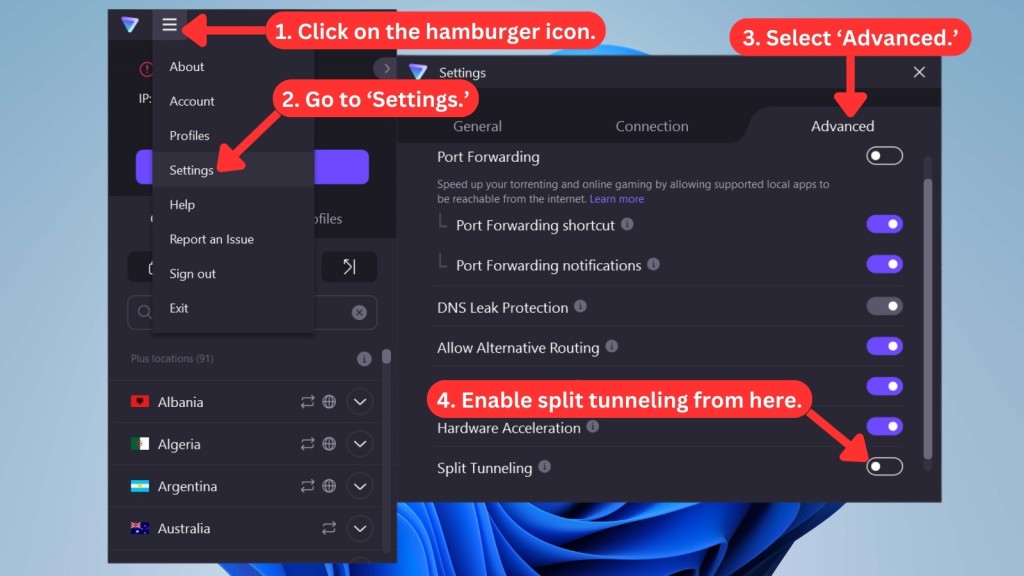
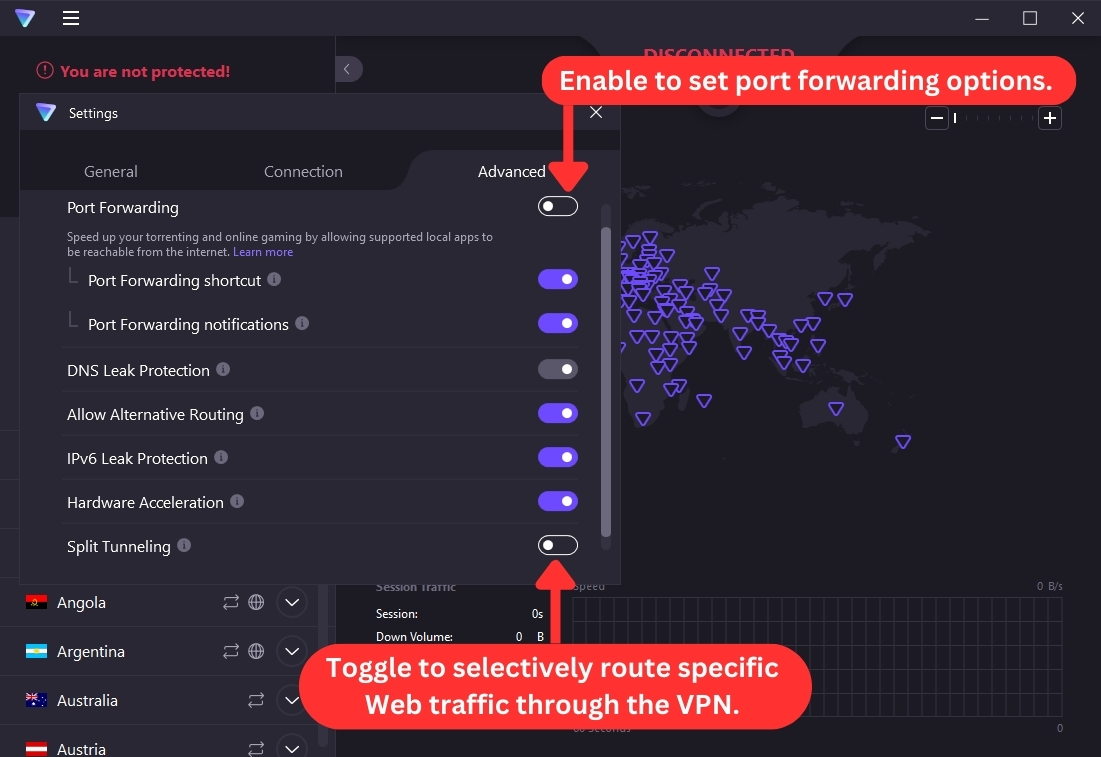
- Split Tunneling: To balance speed and security, you can use split tunneling on Windows and Android devices. This feature lets you decide which apps use the VPN and which ones don't. For example, you can use the VPN for sensitive tasks like online banking or shopping while using your normal connection for streaming or gaming.
- Port Forwarding: This feature directs Internet connections through Proton VPN's protective firewall to keep you safe and your online activities private. It's a handy feature if you download and share files using P2P like BitTorrent. While currently available through the Windows app with a single click, manual configuration options also exist for macOS and Linux users.
- Dedicated IP: Proton VPN offers dedicated IP addresses for business use, ensuring they're always available exclusively for your company. These static IPs remain unchanged throughout your rental period, securing remote access to your business servers. However, you must contact Proton VPN's sales team to get one or more dedicated IPs.
- VPN Accelerator: Speaking of speed, Proton VPN has a unique feature called VPN Accelerator that boosts your connection performance by up to 400%. This built-in feature on all apps uses advanced technologies to overcome CPU limitations, reduce latency, and optimize VPN protocols. Thanks to this feature, Proton VPN is one of the fastest VPNs around.
- Stealth (Obfuscation): This protocol is designed to circumvent censorship and bypass restrictive firewalls. With this feature, you can access information freely, regardless of geographic location. Stealth is now available on Windows, expanding its reach beyond macOS, Android, and iOS.
- Simultaneous Connections: Finally, Proton VPN allows you to install and use the VPN on up to 10 devices at the same time. You can also switch between different servers as often as you want and enjoy unlimited bandwidth. With the multi-login feature (available on all platforms), you can protect all your devices with one subscription.
As you can see, Proton VPN isn’t your average VPN. It covers all the basics while also offering some extra features for advanced users. With its extensive coverage and added bells and whistles, Proton VPN stands out from the crowd.
Server Count & Infrastructure
Proton VPN has recently expanded its server footprint to 8,600+ servers across 117 countries. With such extensive reach, you're highly likely to find a suitable connection to fulfill your VPN needs. Our Score: 10/10
Now, we’ll check the situation with Proton VPN servers, helping you compare this VPN to its main rivals in the VPN industry. Check out the following table.
Proton VPN has recently unveiled new features to break through censorship. This includes the expansion of Proton VPN's server network. The service now includes servers in 12 countries ranked lowest on the "Freedom House" and "Democracy" Indices:
- Afghanistan
- Bahrain
- Eritrea
- Ethiopia
- Iraq
- Kuwait
- Libya
- Saudi Arabia
- Sudan
- Tajikistan
- Turkmenistan
- Yemen
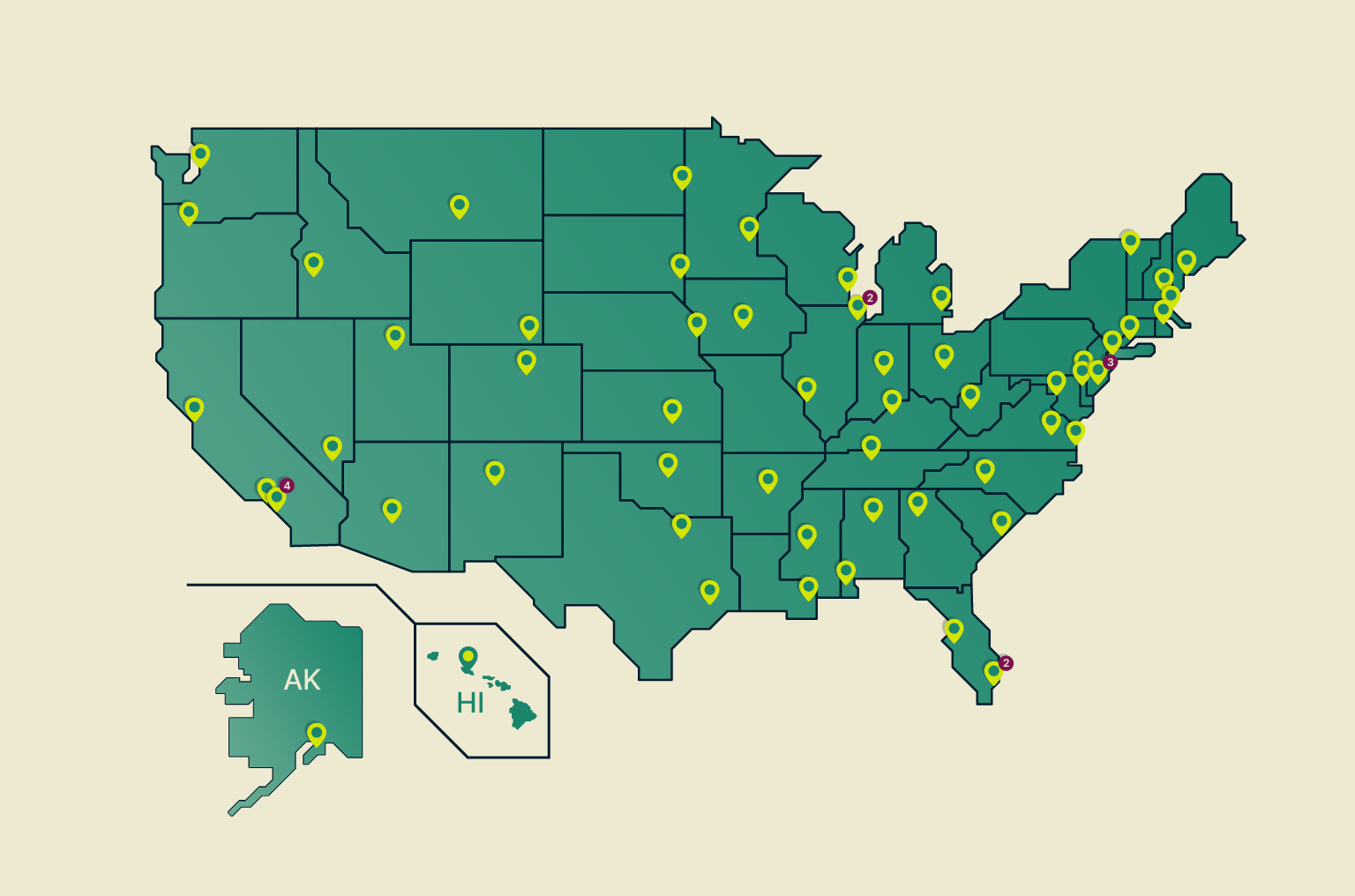
This expansion brings Proton VPN's total server count to over 8,600 across 117 countries, making it a strong contender among the VPNs with the most servers.
Additionally, all of Proton VPN's servers are owned by Proton Technologies AG. They aren't rented from data centers, which means you get the best possible protection for your sensitive data. However, Proton VPN secures data with full-disk encryption, not RAM-based servers. It's great for everyday use, but for the ultimate security, we recommend exploring VPNs with RAM-only servers.
We'd also like to mention that Proton VPN offers specialized servers. For example, some are optimized for streaming, downloading torrent files, accessing the Tor network, and more. There are also 10 Gbps servers - if getting the fastest possible speed is what you want.
When it comes to obfuscation, Proton VPN has a protocol called 'Stealth.' If you use this protocol on your Windows, Android, macOS, or iOS devices, you'll be able to connect to obfuscated servers, making your VPN traffic appear like the usual Web traffic.
Keep in mind that some of Proton VPN's servers aren't located in their 'end' countries. In other words, we're talking about virtual server locations, clearly indicated via the VPN's interface.
Does Proton VPN Use Virtual Server Locations?
Yes, Proton VPN uses 74 virtual server locations via the 'Smart Routing' feature. This technology allows you to connect to VPN servers in countries with limited accessibility without the need for physical server installations.
To use a virtual server, simply connect to one of Proton VPN's Smart Routing server locations. You can easily spot them in the apps because they have a globe icon next to them.
UI/UX Design & Ease of Use
Proton VPN comes with a clean and modern UI design, and it’s one of the most polished VPN applications in terms of its appearance and ease of use. Our Score: 9/10
Unlike most VPNs, Proton VPN isn’t forcing a mobile-like UI. Instead, it's a fully-featured VPN application that you can freely resize and reposition. Therefore, it certainly leaves a positive first impression.
How Well Does Proton VPN Work on Desktop Platforms?
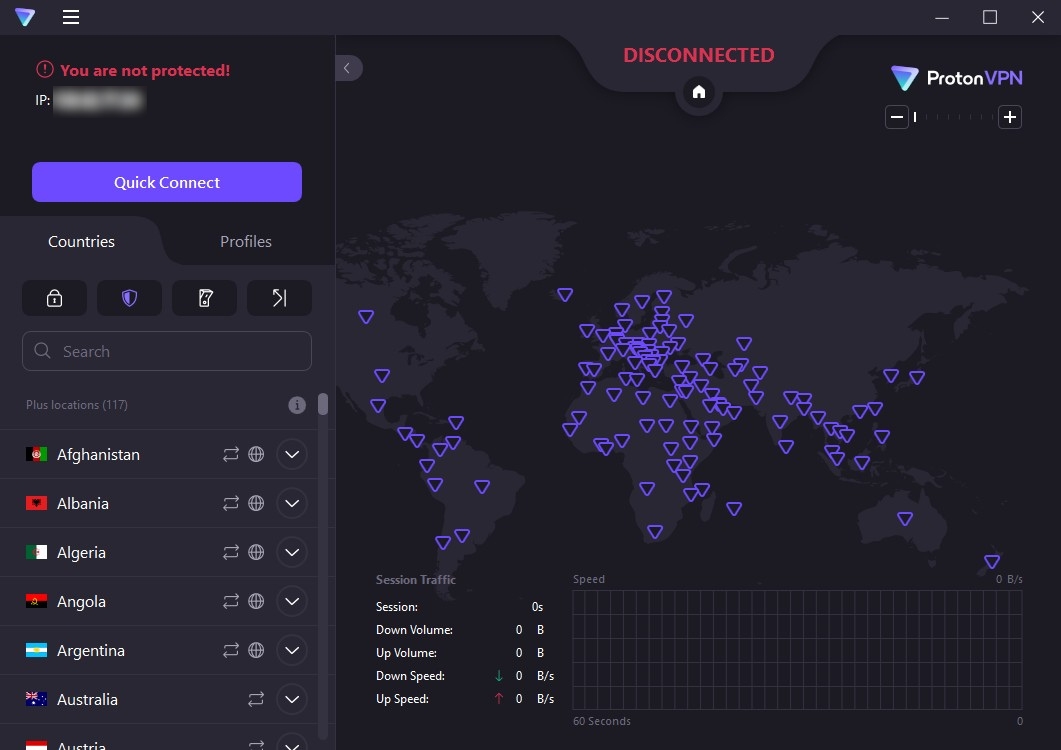
Proton VPN works great on desktop platforms. The home screen of the Proton VPN app provides everything you need to get started, with the biggest portion taking an interactive map of the world.
When you connect to a server, the map displays the country you're connected to. You'll also find information about your session's traffic below the map. You can use the map to connect to different countries, but it doesn’t allow you to fine-tune your user experience (which is where the left-placed sidebar enters the game).
To select a server, look at the left side of the screen, where you'll see a sizeable list of servers with icons that indicate their intended use (streaming, torrenting, and more). You can click on any of these to connect automatically, or you can select an individual location.
Underneath the 'Countries' and 'Profiles' tabs (on the left-hand side), you’ll see 4 useful buttons on the Windows app. The first one on the left lets you connect to 'Secure Core' servers (routing your traffic through two servers at once).
Then, you can use Proton VPN's 'NetShield,' enable 'Kill Switch,' and turn on 'Port Forwarding.'
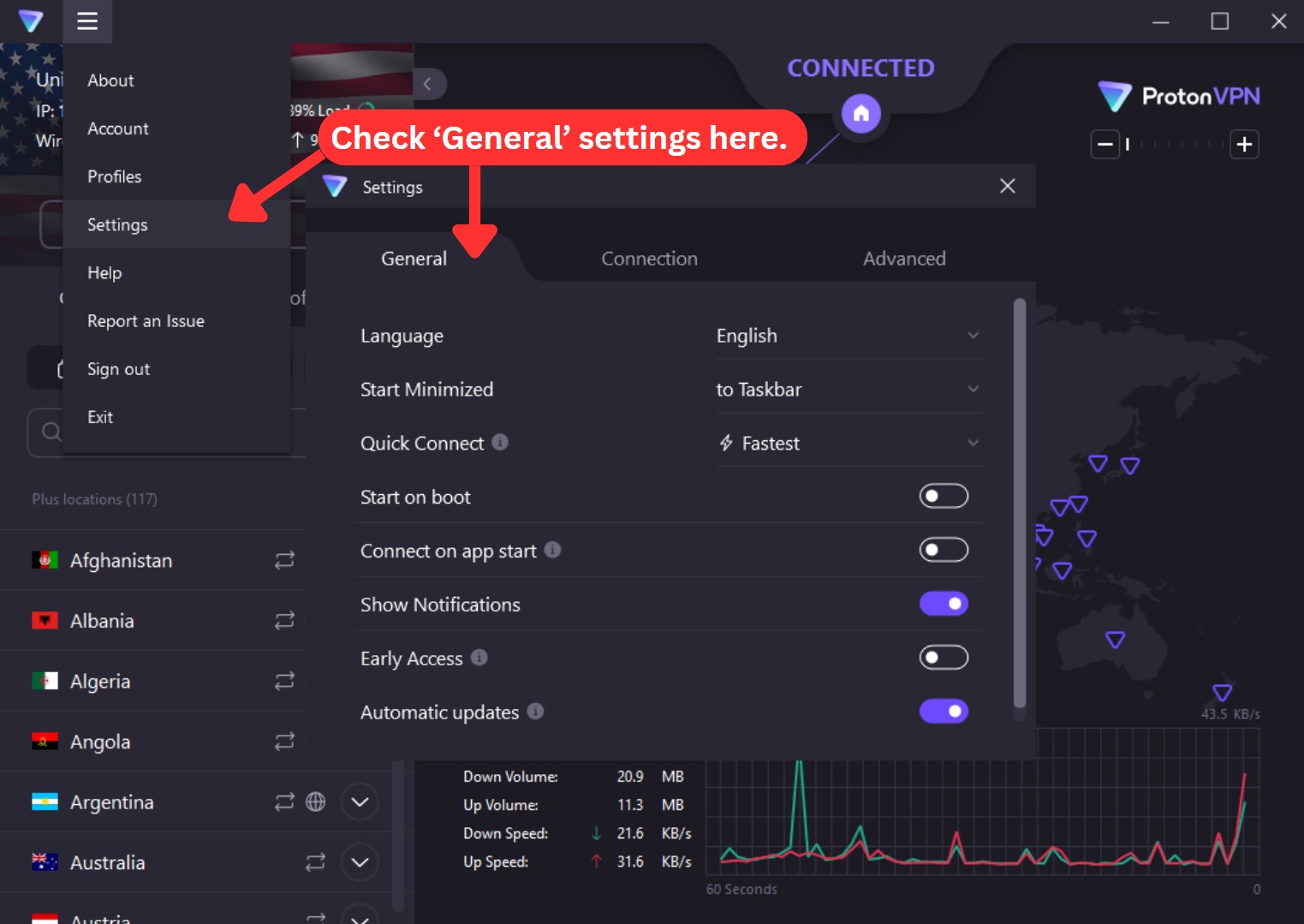
Proton VPN lets you fine-tune your VPN connection by visiting the app's settings. This is where you'll encounter four tabs on a Windows computer. Here's a quick overview:
- General: This tab also allows you to test new features early, and you can fine-tune the application’s behavior (enable/disable notifications, get messages about unprotected networks, and similar).
- Connection: You can find customization options for your VPN experience in this tab. Select your preferred protocol, enable the 'VPN Accelerator' feature (which comes enabled by default), turn on 'Moderate NAT' for better multiplayer gaming, or take control of your Internet traffic by configuring custom DNS servers.
- Advanced: If you're in a country with heavy Internet censorship, you can enable Proton VPN's 'Alternative Routing,' designed to evade anti-VPN systems. This tab also allows you to enable port forwarding, split tunneling, and hardware acceleration for graphics rendering.
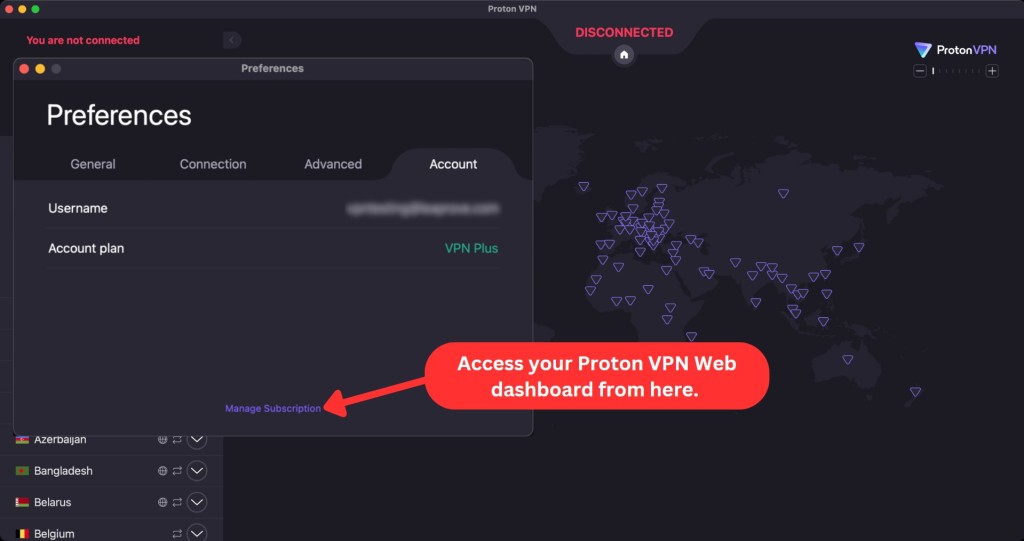
On Mac, you'll find a fourth tab labeled 'Account' where you can check your account information, such as your username, account type, and account plan. To dive deeper into your subscription, you'll see a link at the bottom of this window that takes you to Proton VPN's Web dashboard.
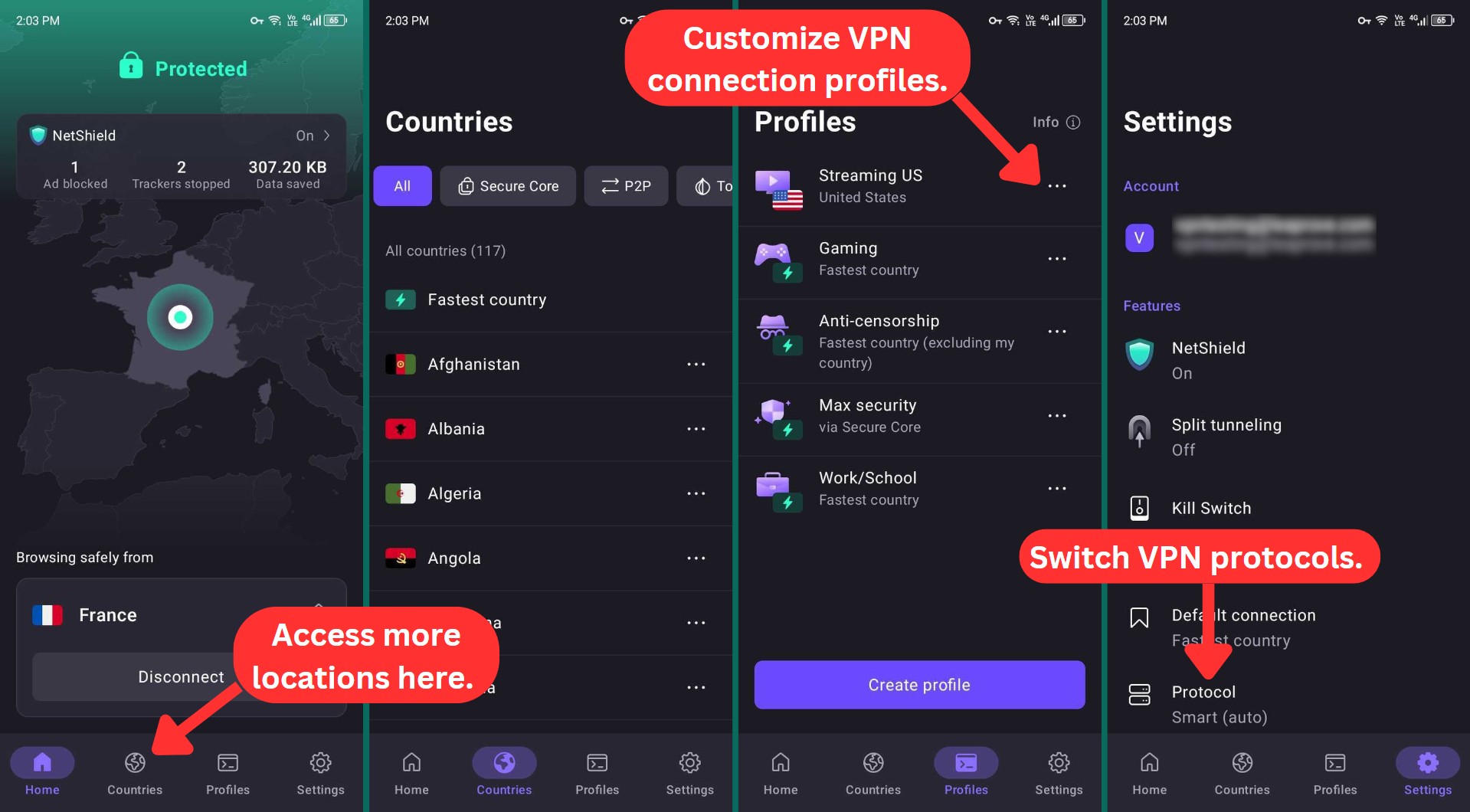
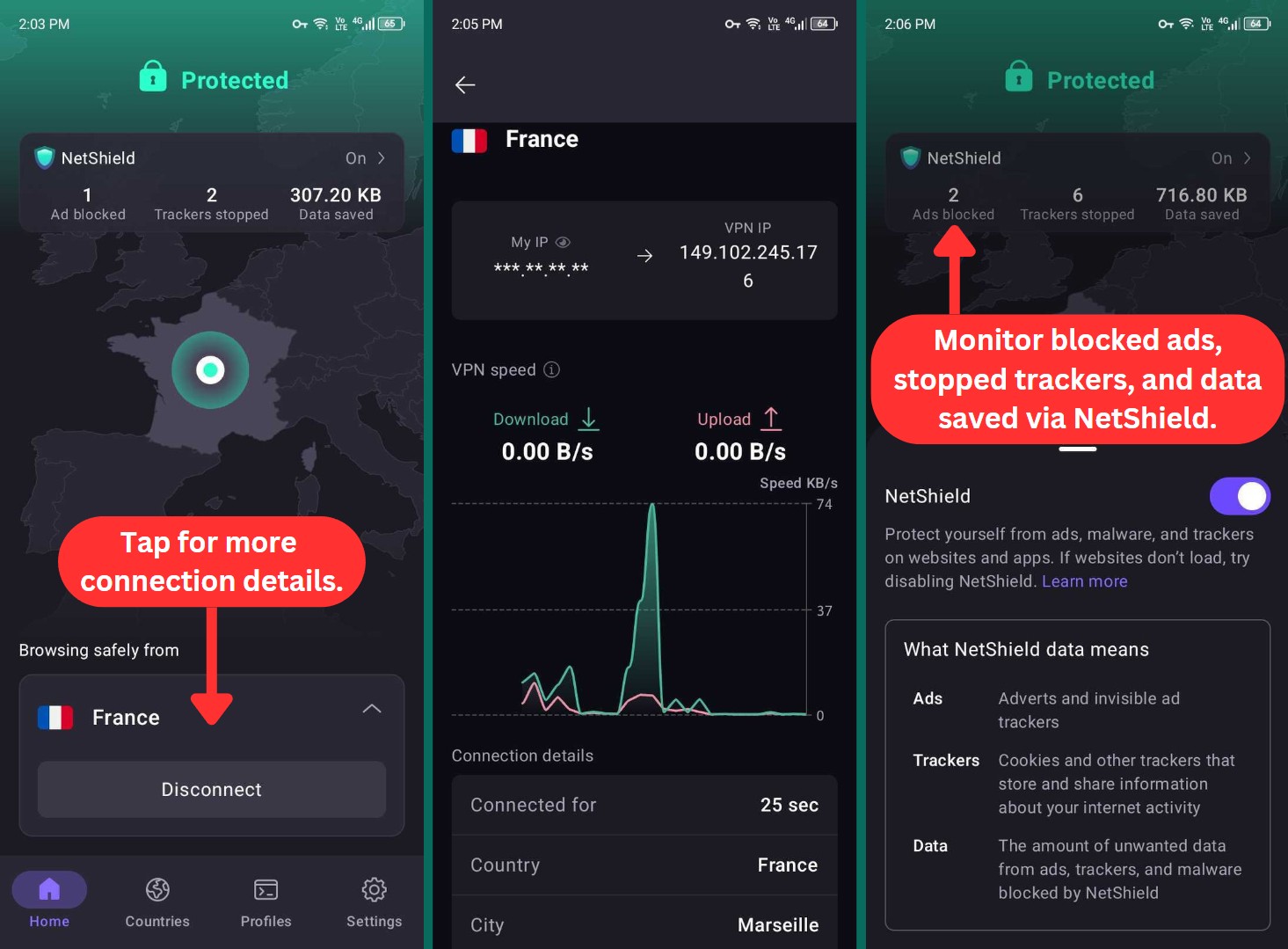
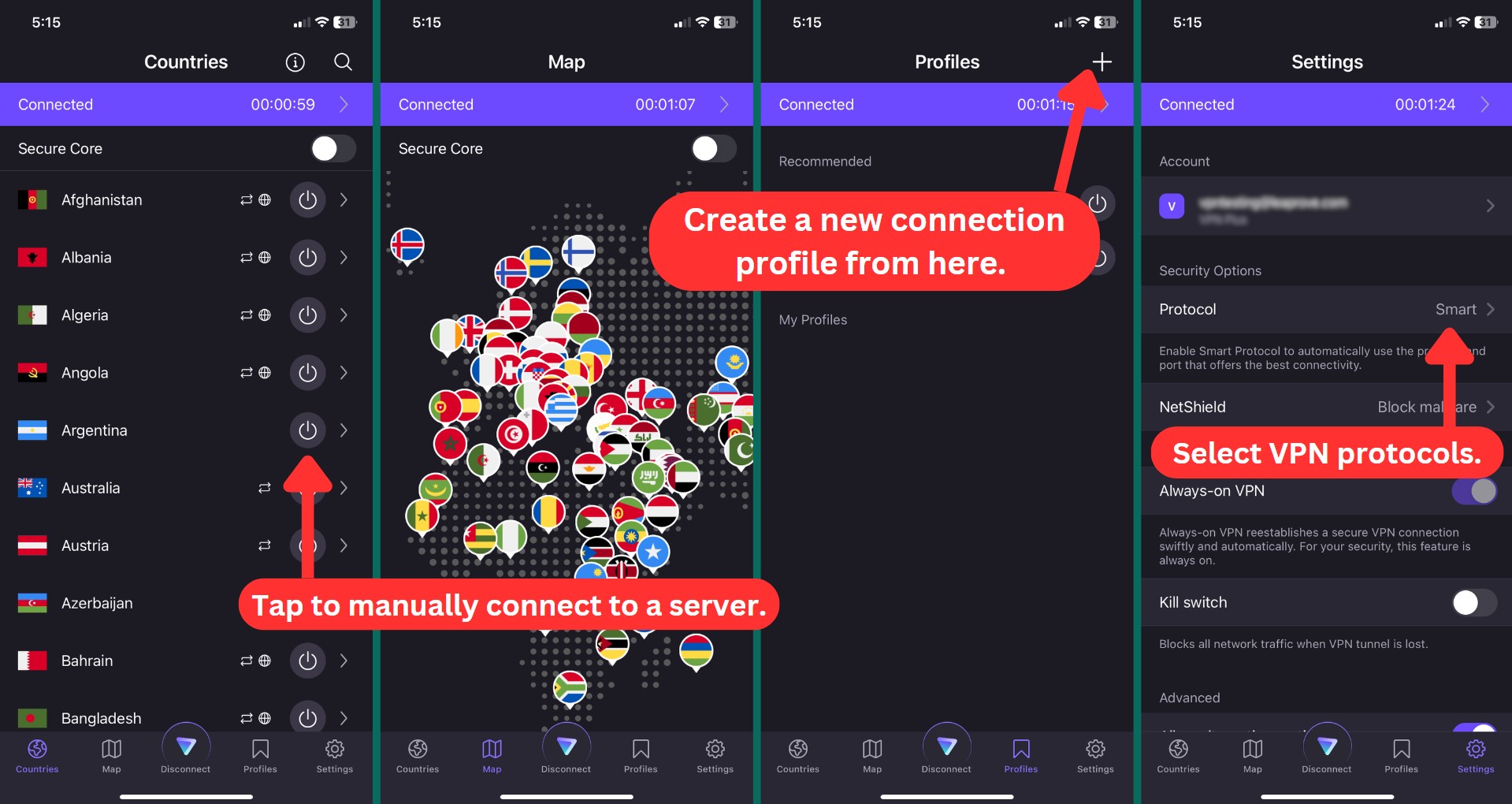
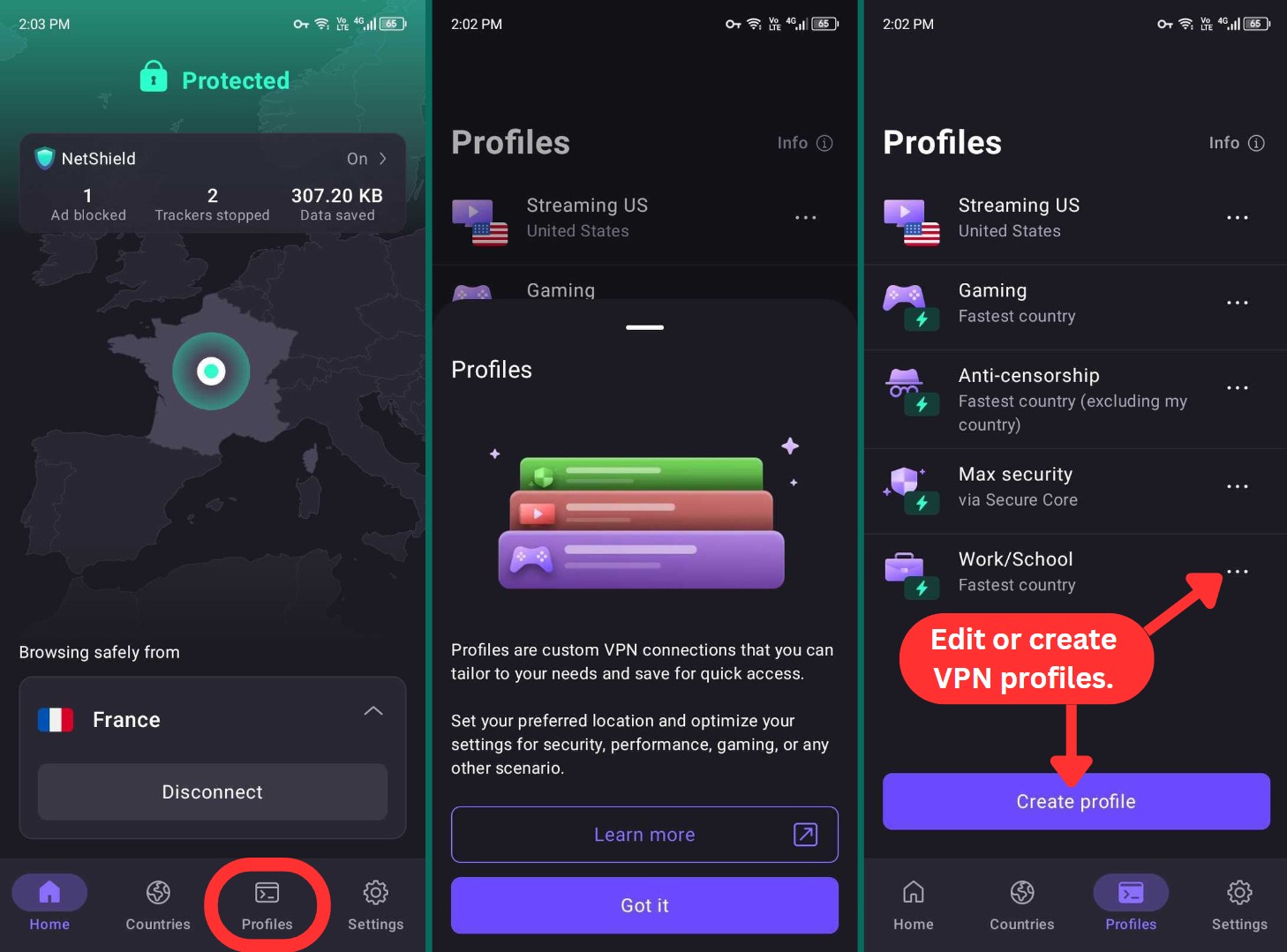
How Well Does Proton VPN Work on Mobile Platforms?
Proton VPN's mobile apps come with a similar design. That means you can expect a highly polished interface that's suitable even for complete beginners. Let's take a closer look at both Proton VPN's iOS and Android apps.
Everything you could possibly need is accessed using the app's bottom-placed menu, letting you connect to different VPN servers and fine-tune your user experience.
When you connect to a server on Android, you'll find information about your VPN protocol, IP address, server location, and other connection details. And when NetShield is enabled, you'll also see data on the number of blocked ads and stopped trackers.
Regarding the settings of Proton VPN on mobile devices, here's what you can tweak:
- Kill Switch (iOS & Android): This feature is easily accessible on iOS devices, but on the Android app, you'll need to access it through your phone's Settings app.
- Split Tunneling (Android): You'll have this feature on Android, but unfortunately, not on iOS devices.
- VPN Protocols (iOS & Android): This is where you can switch to your preferred VPN protocol.
- Profiles (iOS/iPadOS & Android): If you often use the same VPN settings, saving them as a profile makes reconnecting easier. You’ll also find this option on Windows and macOS.
- Alternative Routing (iOS & Android): The alternative routing feature allows you to use the VPN service even when server connections are blocked.
- Always-On VPN (iOS & Android): The iOS app has the always-on VPN feature enabled by default, while on Android, you need to manually activate it. Android devices can also use the kill switch feature to block all network connections if the VPN connection is lost.
- VPN Accelerator (iOS & Android): This feature is automatically enabled in all Proton VPN apps. It enhances the performance of all VPN protocols and is accessible to all users.
Proton VPN's latest Android update also introduces a 'Discreet' icon that lets you disguise the app as any other app on your phone. This feature is essential for users facing the threat of device inspections in countries like China and Myanmar. To use this feature, simply go to Settings > General > App icon.
All in all, Proton VPN is one of the rare VPNs with a highly polished UI design. It’s suitable both for beginners and advanced users, as it allows plenty of customization. Every option and feature is explained nicely, and there are helpful tooltips around the application's UI.
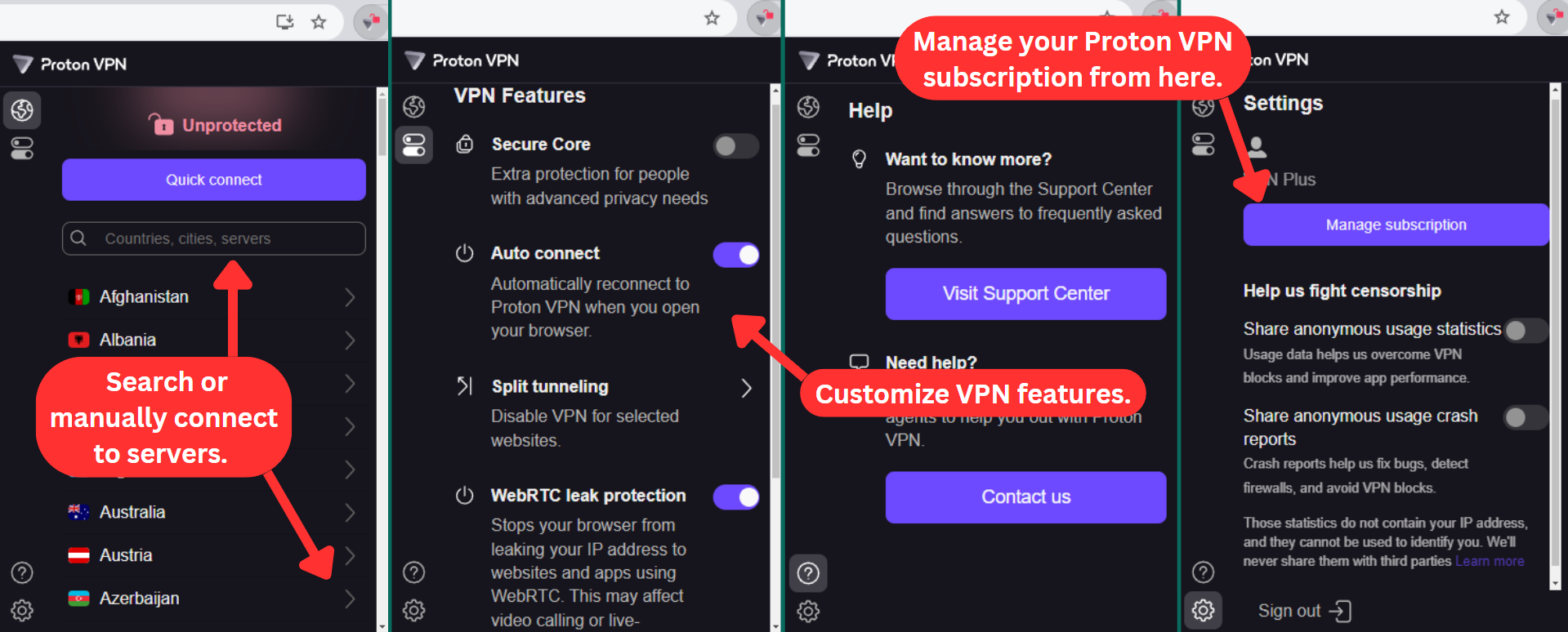
How Well Do Proton VPN’s Web Browser Extensions Work?
Proton VPN has recently introduced a Web browser extension that extends its compatibility beyond the Firefox and Chrome extensions. It's also available on Chromium-based browsers, such as Brave, Edge, Opera, and Vivaldi, as well as Firefox-based browsers like Waterfox and LibreWolf.
Until recently, these extensions were reserved for premium subscribers only. However, that's no longer the same. You get access to the Chrome and Firefox extensions even if you're a free user. In that case, Proton VPN will connect you to the nearest server automatically. You do get unlimited bandwidth and speed, though.
These extensions tend to offer the same set of features across all supported browsers. Also, what makes these extensions stand out is that they let you use all Proton VPN server locations. But remember, the extension only secures your browser traffic, so for complete protection on your computer or other devices, we still recommend using the full app.
If you click on the 'Features' icon, you can access the advanced features of these browser extensions.
- Secure Core: This feature is handy if you have advanced privacy requirements.
- Auto Connect: You can automatically reconnect to the VPN service whenever you open your browser.
- Split Tunneling: This allows you to disable the VPN for selected websites.
- WebRTC Leak Protection: While this feature might impact live streaming and video calls, it prevents your browser from unintentionally revealing your IP address to apps and websites that use WebRTC.
Media Streaming, Torrenting, and Gaming Support
Proton VPN works with most streaming platforms, offers a range of specialized P2P servers, and provides digital tools to enhance your online gameplay. Our Score: 9.5/10
One of the most popular uses of VPNs is their website-unblocking capability. That's especially useful when it comes to streaming, so let’s see which services work with Proton VPN.
Is Proton VPN Good for Streaming?
Yes. We had plenty of success unblocking websites, both mainstream and niche streaming platforms. In terms of accessing the US version of Netflix, you’re covered well. Plenty of servers offered by Proton VPN can make that happen. However, we recommend going for US-based servers dedicated to streaming to give you the best results.
Based on our experience, Proton VPN had no trouble unblocking the US-based streaming platforms listed in the table below.
You can also expand your streaming options with this VPN, as it unlocks a range of non-US streaming platforms for your enjoyment. Here are some notable examples.
Proton VPN may not be among the top VPNs for streaming, but it has come a long way. It does a solid job unblocking content and even getting around sports blackouts. We hope it keeps moving in the right direction.
Is Proton VPN Good for Torrenting?
Yes. You’ll be happy to know that Proton's P2P servers are optimized for secure and fast torrenting. We tested it by downloading a few public-domain movies using uTorrent, and everything ran smoothly with no connectivity issues. Just keep in mind that torrenting is only available with the paid 'Plus' plans.
One thing we found useful is port forwarding, which can help with both download and upload speeds when using P2P apps. Another nice touch is the 'Always-On' VPN feature on mobile. If your connection drops, it automatically reconnects, so you stay protected without having to do anything.
But what makes it a suitable VPN for torrenting is its unique Tor over VPN feature. It routes traffic through the Tor network, making it much harder for anyone to track your online activity while torrenting.
Is Proton VPN Good for Gaming?
Yes. In fact, it’s one of the best free gaming VPNs we recommend. Unlike most free VPNs, it doesn’t limit your data, so you can play as much as you want without hitting a cap. We've tried it with fast-paced games like Call of Duty: Warzone, Apex Legends, and Marvel Rivals, and while the free servers had higher ping, the connection was stable enough for casual gaming.
Proton VPN supports WireGuard, which helps keep latency low, especially on nearby servers. The 'VPN Accelerator' feature also makes a difference, boosting speeds even when connecting to long-distance servers.
That said, if you’re gaming on a paid plan, you’ll get much better performance (lower ping, less lag, and faster response times). But if you want to explore other options, check out our article on the best gaming VPN.
Security & Privacy
It’s clear that Proton VPN safeguards your private data in the best way possible. It also doesn't log your personal information, as proven by a recent independent audit. Our Score: 10/10
Let's not forget that the primary use of any VPN is to protect your privacy. To ensure Proton VPN delivers, we'll assess three key areas: VPN protocols, logging policy, and IP/DNS leaks. These factors directly impact how well your data is protected.
Proton VPN Protocols
While Proton VPN offers a range of VPN protocols, their availability varies depending on the device you're using. To provide you with a clear understanding, the table below will show you the protocols offered by Proton VPN.
- OpenVPN: Proton VPN uses strong VPN encryption with this protocol, creating new session keys for each connection. OpenVPN can run on Windows, Linux, and Android, offering both UDP and TCP options for better performance and security.
- WireGuard: This lightweight and open-source VPN protocol stands out for its speed compared to older protocols. It's available on Windows, macOS, iOS, and Android devices. It enhances security using the advanced ChaCha20 encryption cipher to safeguard your VPN connection.
- IKEv2: If you're a Mac user, you'll get this fast and secure protocol. It improves security through the automatic implementation of forward secrecy, achieved via the Diffie-Hellman key exchange process.
- Stealth: This is an advanced VPN protocol that beats most online barriers. It helps you access blocked sites and social media, even if your government tries to stop you. You can use Stealth on Windows, macOS, iOS, and Android with any Proton VPN plan, including the free one.
Does Proton VPN Keep Logs?
No, Proton VPN doesn't keep logs. It collects some data, just like any other VPN. However, it collects nothing that can identify what you do online.
As noted in Proton VPN's Privacy Policy, this VPN retains essential data (username, email, and billing information), which is deleted from their servers once you decide to no longer use this service. Then, once you start using its apps, certain anonymous and aggregate statistics can be logged.
In terms of data sharing, Proton VPN works with its parent company (Proton Technologies AG - Switzerland) to share data and provide customer support. That's because Proton VPN and Proton Mail use the same user database, letting you manage your subscriptions more easily.
All of Proton VPN's apps are also open-source, which means that they're available for inspection by just about anyone out there. Plus, Proton VPN's no-logs policy is backed by numerous independent external audits.
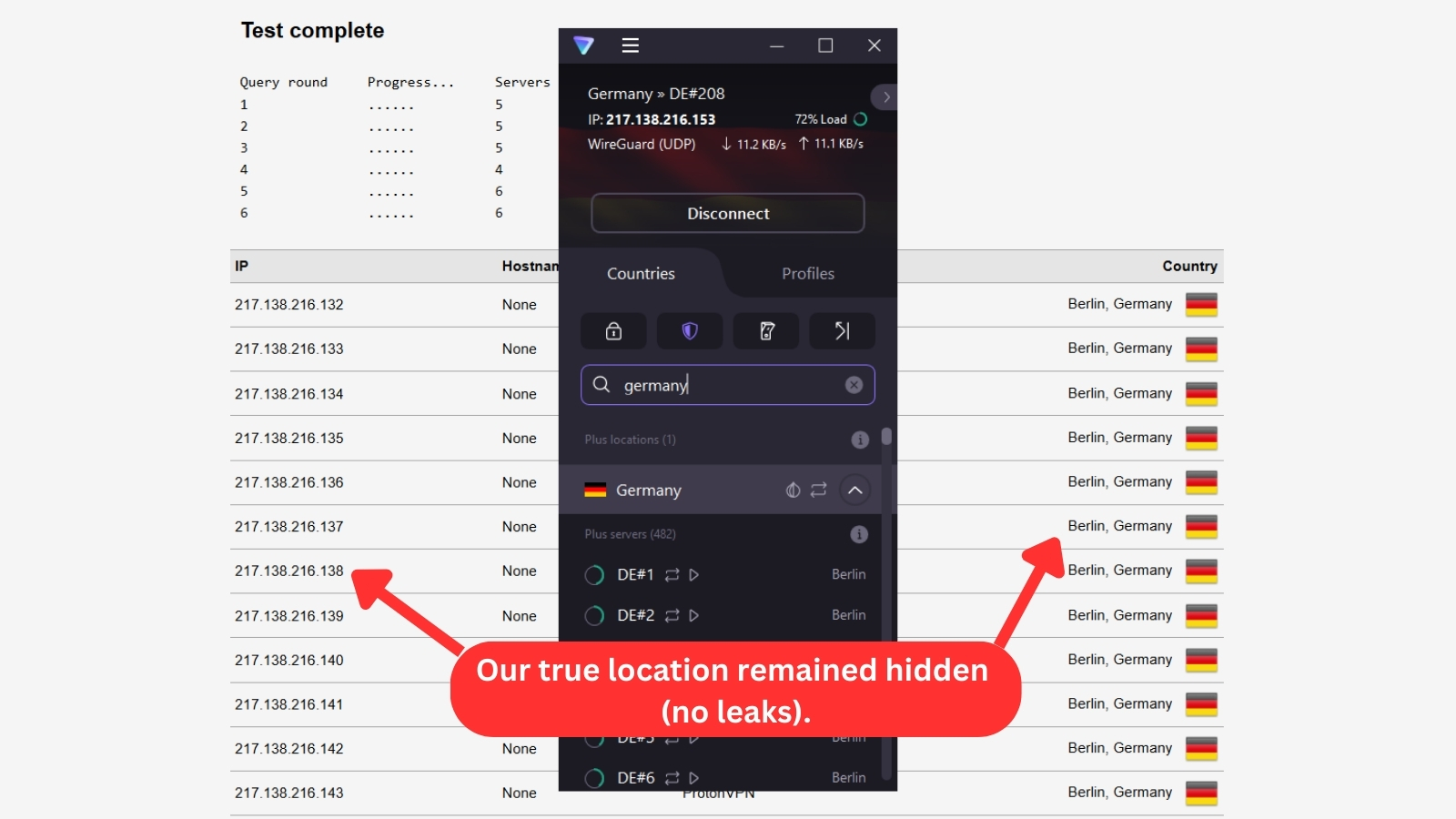
Does Proton VPN Leak/Expose Private Data?
No, Proton VPN doesn't leak any private data. We've also done a round of DNS and IP leak tests to ensure that there are no active VPN leaks.
As you can see, Proton VPN employs effective leak protection measures. Third parties on the Web can only see what Proton VPN is showing them, and that includes your virtual IP address, hostname, country of origin, and more.
Speed & Performance
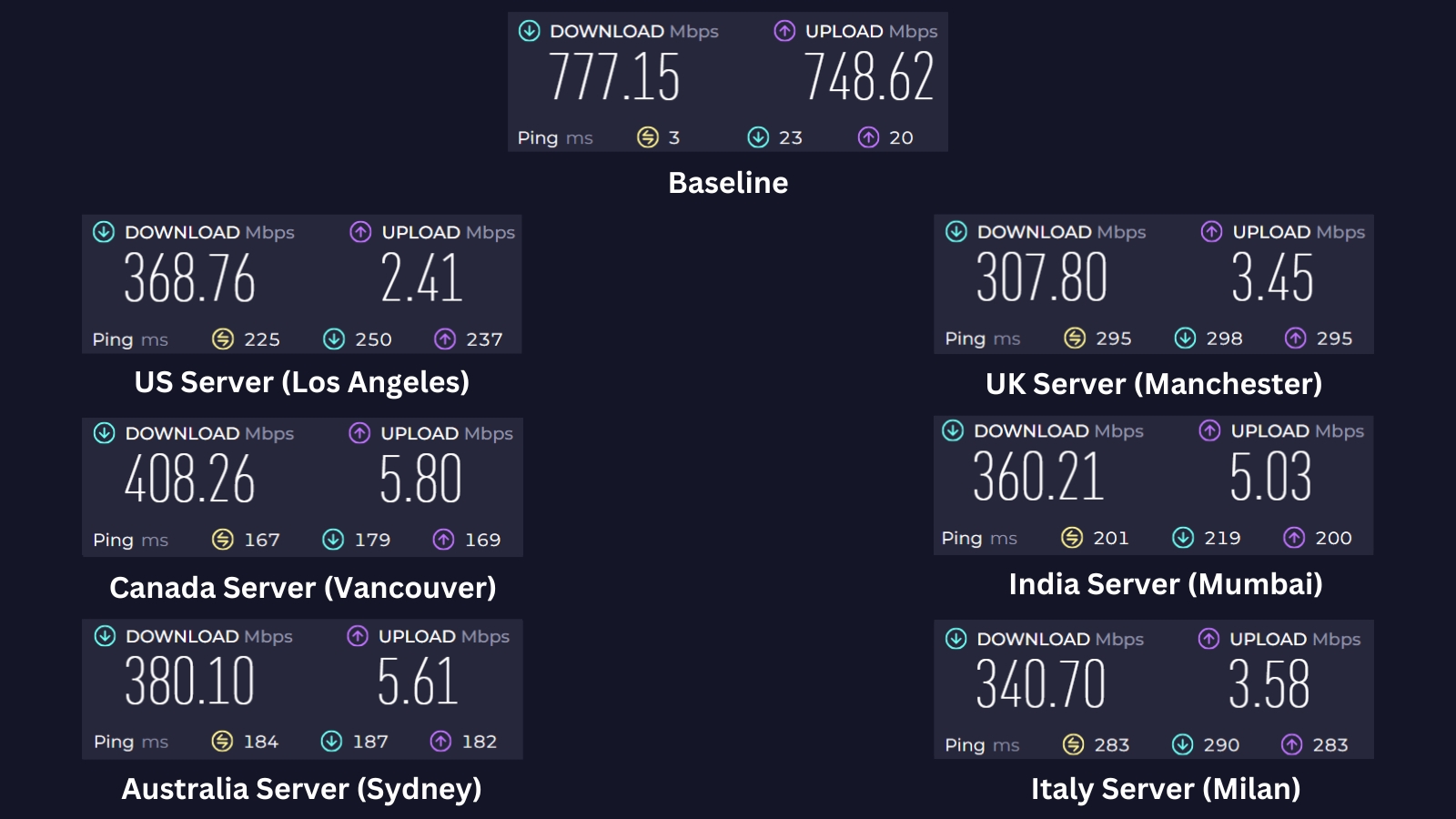
Proton VPN handled some locations better than others, with speed drops that made sense for the distance. Even with the slowdowns, most servers kept things running smoothly for regular online use. Our Score: 6/10
In this section, we're testing Proton VPN’s impact on connection speed from one of our Asian locations. Our 'naked' connection, without the VPN, has 777.15 Mbps for downloads and 748.62 Mbps for uploads on a 700 Mbps connection.
Next, we'll connect to different servers around the world and compare the results. Since VPNs tend to slow down your Web traffic by making connections travel longer routes, we want to see how well Proton handles this challenge by testing both nearby and remote servers.
Here are the results of our server tests:
- US Server (Los Angeles): Connecting to a distant US server brought download speeds down to 368.76 Mbps, cutting off 53% of the original speed. Despite the drop, this is a strong result for a long-distance connection. Proton VPN seems to handle transpacific traffic well, but performance may vary depending on network conditions.
- UK Server (Manchester): The UK server had the lowest download speed among all the servers we tested, delivering 307.8 Mbps with a 60% speed loss. One possible reason could be server congestion or inefficient routing between Asia and the UK. Though not the best result in this test, the speed is still good enough for 4K streaming and general browsing.
- Canada Server (Vancouver): Canada had the fastest download speed among the distant servers, which was unexpected given its distance from our location. It delivered 408.26 Mbps, with a 47% speed loss. Optimized routing through North America or lower congestion on this server might have contributed to its strong performance.
- India Server (Mumbai): Despite being relatively close to our location, the India server clocked in at 360.21 Mbps, with a 54% speed loss. This could be due to higher server load, as India’s servers are often in high demand. Even with the drop, its performance stayed strong, allowing for lag-free browsing and streaming.
- Australia Server (Sydney): The Australian server delivered 380.1 Mbps, dropping our download speed by 51%. Given the distance, that's still a good result, showing that Proton VPN’s network in the Asia-Pacific region is well-optimized.
- Italy Server (Milan): This server delivered downloads of 340.7 Mbps, showing a 56% speed drop. That’s expected for a long-distance European connection, but the speeds were still usable for most online activities. The lower performance might be due to network congestion or Proton VPN’s routing choices within Europe.
Proton VPN slowed down our Web connection by 53% on average, so it’s not among the fastest VPNs. Even so, speeds never dropped below 307 Mbps, which is more than enough for 4K streaming on multiple devices. If your connection is fast to begin with, performance shouldn’t be an issue.
We should also mention that Proton VPN drastically reduces your upload speed. Therefore, if you upload a lot of data frequently, you might want to look for a different VPN service.
Customer Support
Proton VPN offers live chat support, but it's only available for paying customers. If you're on the free plan and need immediate assistance, you'll need to submit a support ticket and wait for a response, which could take up to 24 hours. Our Score: 7/10
VPNs are incredibly complex applications that depend on an extensive network of servers. Therefore, you shouldn't be surprised if something goes wrong occasionally. That's why you should always go for a VPN service that offers reliable customer support and is ready to resolve your issues in a timely manner.
Here's what you can count on in terms of Proton VPN:
- Live Chat: This service is exclusively available for paying customers during weekdays. For non-urgent inquiries or questions on weekends, you can submit a support request on their website.
- Knowledge Base: Whether you're setting up the service, managing your account, or troubleshooting an issue, you'll likely find the answers you need in Proton VPN's knowledge base.
- Installation Guides: Proton VPN offers user-friendly installation guides with clear step-by-step instructions for various platforms. These guides ensure a smooth setup process regardless of your technical expertise.
- Frequently Asked Questions: There’s a whole range of frequently asked questions on Proton VPN's site. Those are related to using the VPN, accessing different types of content, and troubleshooting technical problems. This can be helpful in some situations, even though this customer support section isn’t the most comprehensive.
- Support Tickets: Finally, you can contact the company by filling out a form on its website. Explain your problem in detail and expect to receive a response within 24 hours.
Although Proton VPN doesn't offer free live chat for all, their active blog keeps you updated on VPN news and offers helpful tips. Its dedicated Subreddit also fosters a supportive community where you can connect with other users.
Plus, Proton VPN leverages a GitHub community for open-source development, allowing deeper collaboration and transparency for the technically inclined.
Pricing
Proton VPN's pricing has recently been lowered, increasing the VPN's overall value. It's now much more competitive, giving you plenty of subscription options. Our Score: 9/10
If you're looking for an affordable VPN for a short time or a long time, you might want to consider Proton VPN. This service has recently updated its plans and prices to make them more affordable and accessible to users. Here's everything you should know about Proton VPN's current pricing.
How Much Is Proton VPN?
Proton VPN starts at $3.59/month on its 2-year plan. Apart from that, it has three other plans for you to choose from: free, monthly, and 12 months.
The free plan has limited features, and the other three plans offer the same benefits at different prices. You can find out more about the free plan in the next section. In the table below, you'll find the prices for Proton VPN Plus plans.
- 1 Month Plan: For only $9.99/month, you can enjoy Proton VPN's streaming support, Tor over VPN, NetShield, and access to servers in 117 countries. Plus, you can connect up to 10 devices at the same time, along with having access to Proton Mail, a secure email service that protects your privacy and data. This plan is great for testing the service.
- 1-Year Plan: This plan is a steal at $3.99 per month, billed for one year at $47.88. You'll save 60% compared to the monthly plan and get all the same features. It's suitable for users who have already tried and tested the service and are willing to commit for the long haul.
- 2-Year Plan: If you want to get the most bang for your buck, this option is for you. It costs $3.59 per month, billed for the first two years at $86.16. You'll save 64% compared to the 1-month plan, and this plan includes everything from the 12-month plan and more.
No matter which plan you pick here, you'll get all its features. But the monthly plan isn't a great deal for its price. It costs more and only lets you use the standalone Proton VPN plan. Choosing the 2-year plan at a 64% discount can significantly lower your overall subscription cost.
If you want more than just a VPN, check out Proton Unlimited's deals. This bundle includes Proton Mail, Calendar, and Drive. Here are the prices for this all-inclusive package.
Proton lets you pay with PayPal or credit/debit cards, but if you want to stay anonymous, you'll need a different method. The service used to accept anonymous payments for new accounts, but now it only offers that option for upgrades. That means you have to sign up for a free account first and then use Bitcoin to get a premium subscription.
Alternatively, you can pay with cash or via bank transfer, but it's more complicated and non-refundable. We recommend reaching out to Proton VPN directly for detailed instructions on how to proceed with that.
Is Proton VPN Free?
Yes. In fact, it's one of the best free VPN services. However, it has limited features. While you won't need a credit card to sign up for the free version, you'll be restricted to medium-speed servers in just 5 countries and can only connect one device at a time. You also get low-priority customer support without access to live chat and advanced features found in the paid plans.
On the other hand, Proton VPN’s free trial lets you test out the VPN's paid features risk-free. Except for subscriptions paid via bank transfer or cash, all Proton Plus plans are fully refundable for 30 days, so you can try the premium plans with no risk. If you're satisfied with the service, you can subscribe to the 'Plus' plan and pay for the full experience.
This shows the differences between free, paid, and free trial VPNs - free versions are limited, paid plans give you access to everything, and free trials let you test premium features without any commitment.
Proton VPN Comparison with Other VPN Providers
In the crowded VPN market, Proton VPN stands out as a trustworthy choice thanks to its extensive privacy and security features. It offers competitive speeds, high-end encryption, and a zero-logs policy, making it a strong alternative to industry heavyweights like NordVPN and ExpressVPN.
We’ve created in-depth comparison articles for each provider to show how Proton VPN compares. Here are the links to these detailed comparisons.
Final Thoughts - Is Proton VPN Good?
Yes, Proton VPN is more than good - it's one of the rare VPNs with a special emphasis on protecting the overall security of its users. Its free tier offers a taste of its features, while the paid plans offer strong value with their advanced capabilities.
However, some limitations exist, such as the lack of uniform availability for features like port forwarding and split tunneling across all apps. Additionally, live chat support is restricted to premium plans.
Despite these drawbacks, we recommend subscribing to Proton VPN as it remains a compelling choice if you prioritize privacy and security, with the ability to unblock popular streaming services.
PROS
- Has a free version.
- Full data leak protection.
- Works on many devices.
- Ultra-fast performance.
- Offers obfuscation.
- Extensive server network.
- Block trackers, ads, and malware.
- Includes a double-hop feature.
- Supports port forwarding.
- Provides dedicated IPs (for business use).
CONS
- No live chat for free plans.
- No split tunneling on Mac & iOS.
- Cash payments are non-refundable.
| Review Summary Proton VPN comes with plenty of strong selling points that can easily persuade any individual into becoming a subscriber. We strongly recommend it! | 9 Overall Score | ||
| Background, Jurisdiction & Reputation | 10 | ||
| Supported Platforms & Devices | 10 | ||
| Installation & Initial Configuration | 10 | ||
| Prominent Features | 9 | ||
| Server Count & Infrastructure | 10 | ||
| UI/UX Design & Ease of Use | 9 | ||
| Media Streaming, Torrenting, and Gaming Support | 9.5 | ||
| Security & Privacy | 10 | ||
| Speed & Performance | 6 | ||
| Customer Support | 7 | ||
| Pricing | 9 | ||