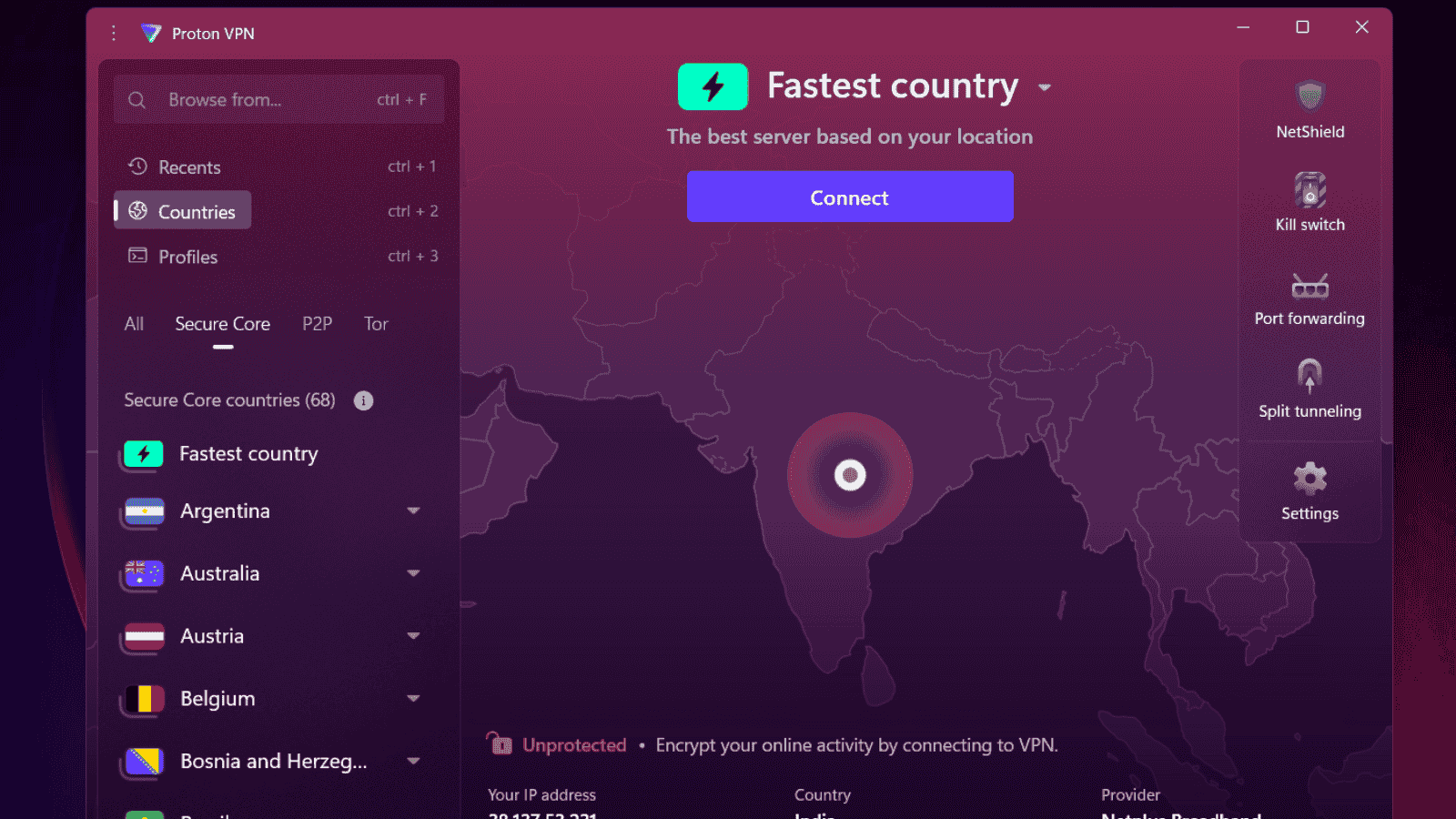
[Updated] NordVPN and ProtonVPN Found to Contain Privilege Escalation Bug
- A privilege escalation bug was found in NordVPN and ProtonVPN.
- The bug allowed malicious code to run with administrator privileges.
- The latest versions of NordVPN and ProtonVPN seem to have addressed this vulnerability.
Update 14/9/2018 — NordVPN reached out to us to clarify that the service is immune to CVE-2018-4010. The vulnerability had apparently been fixed and end-user clients were updated much before it was made public. Also, even if the client has not been updated, for the said vulnerability to take effect, it would require physical access to the PC, which is highly unlikely. NordVPN also assured that they are running an independent security audit. In short, if you are running the most up to date version of NordVPN, everything should be fine. More details can be found here.
A privilege escalation bug was recently discovered in popular VPN clients NordVPN and ProtonVPN in a patch that prevented arbitrary code from running with administrator privileges. The bug was discovered by Paul Rascagneres of Cisco Talos who found it in the most recent versions of the two VPN clients. The bug has since been fixed in the latest versions. Both clients use OpenVPN to create a secure tunnel to the VPN servers so the programs need to be run with administrator rights, which automatically gives the bug elevated privileges.
The bug allows the OpenVPN configuration file to be altered to contain malicious code that can be passed on to the service and executed under elevated rights in Windows. OpenVPN allows configuration files to run with the service and changes to this configuration file could allow malicious code to seep through. In fact, NordVPN and ProtonVPN addressed a previous vulnerability reported earlier by Fabius Watson of VerSprite Security that allowed the configuration file to contain parameters such as "plugin" or "script-security". Both these VPN software also implemented checks for the presence of parameters such as "up" and "down".
Despite addressing the vulnerability, Rascagneres found out that simply encapsulating the parameters in quotes can basically override the protection and allow privilege escalation. He demonstrated this by using the ProtonVPN service to open notepad.exe. The bugs are currently tracked as CVE-2018-3952 for ProtonVPN and CVE-2018-4010 for NordVPN.
ProtonVPN 1.5.1 and NordVPN 6.14.28.0 seem to have addressed this vulnerability. According to Rascagneres, both services have used different approaches to patch the bug. ProtonVPN placed the OpenVPN configuration file in the installation directory thereby preventing standard users from modifying it while NordVPN used an XML model to generate a non-editable OpenVPN configuration file. Users are recommended to check for updates and ensure that the latest versions of these VPN clients are installed.
What do you think about the bug finding in these two popular VPN software? Let us know in the comments below. Also, to get instant tech updates, follow TechNadu’s Facebook page, and Twitter handle.