The No-Nonsense Guide to BitTorrent – Covering What is P2P, How it Works, and How to Use it!
Just like with other popular technologies, there are a lot of misconceptions about torrents. The biggest one is that torrents are illegal, which isn't actually true. In its essence, this file-sharing technology is legal and can be used to easily distribute large files. However, you still need to pay attention to what you're downloading. We are going to explain what is BitTorrent, how you can use it, and we'll clear any doubts you might be having. So, welcome to our BitTorrent Guide!
The Ultimate BitTorrent Guide - From A to Z!
In this comprehensive guide, we will explain how torrent file-sharing works - as this method has numerous characteristic elements that set it apart. Once we go deeper, we will discuss your role in BitTorrent file-sharing, the legality of it, and pretty much everything you've ever wanted to know.
How Downloading Files Work: The Basics
To really understand how torrents work, you first need to understand how 'normal' file downloads operate, so that’s where we’ll start.
How Do Normal Downloads Work?
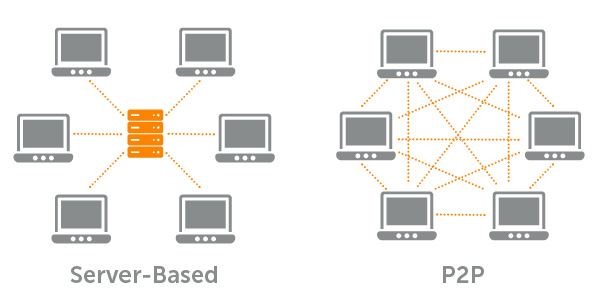
In general, files that you download from the Web live on a specific server. You can think of it as a computer that's always online. Therefore, you can access their storage and download the required file at all time.
You click on a link to initiate the download. Then, the server allocates you a slot and then starts to send the bits and bytes that make up your file to you over the Internet as packets of data. When they get to your computer, they get put back into the right order until the file is whole again. Download complete!
There are minor variations on this basic method of providing files. For example, there may be several servers all over the world in what’s known as a CDN or content distribution network. When you request a file, you might be redirected to a server that has a copy closer to your location. That makes it all run faster. You might also be redirected if the first servers that get the request are too busy serving other users.
What Makes BitTorrent Different?
BitTorrent is the most well-known example of peer-to-peer technology - often shortened to simply 'P2P'. In networking lingo, a peer is another computer that’s just a regular old client on the network like you.
When information is exchanged between peers that’s (you guessed it) a peer-to-peer transaction. Almost nothing on the Internet works this way. Even when you do appear to send something to someone else, there is always a server that mediates that interaction. For example, emails go to an email server before reaching their destination. Skype calls also route through their servers first. The list goes on and on.
With BitTorrent, the information does not reside on a central server. There is no file server, just a swarm of peer computers that have the same files and can share it with others. When you download a file by using torrents, the individual bit and bytes are coming from the hard drives of other people like yourself from all over the world. It’s actually quite beautiful when you think about it.
This also means that files shared across BitTorrent are very resistant to being lost. As long as there is at least one complete copy of the file’s data in the swarm of computers, the network can continue to provide it.
How Does BitTorrent Work - Seeders, Leechers & More
While we have covered the broad technical details of how torrents work above, here we’re going to look at it on a more technical level. The key terms you’ll encounter in the torrenting world will be explained and the process of communication per the protocol’s rules will be outlined. We’ll also talk about how the different elements of the BitTorrent system come together so that the magic can happen.
What is a Tracker?
A torrent tracker is the closest thing BitTorrent has to a central server. The tracker is a computer that does not host the files that are being shared, but tracks who all the peers are. It also notes which files are on which peer computer, how complete they are and so on.
In other words, the tracker is like someone who introduces you to another person so that you can have a chat. The tracker itself is only involved every now and then, usually to help peers first find each other and then to request periodic updates on the state of each peer.
Trackers have begun to seriously fall out of favor in exchange for new methods that don’t need a tracker at all. We’ll discuss those in just a little while. Before that, let’s look at the types of tracker you can get.
Public and Private Trackers
Popular torrent site The Pirate Bay is an example of a public tracker. Well at least until it started focusing on trackerless technologies. Why do we say it’s public? It’s actually a pretty simple reason. Anyone who wants to use a tracker for their torrent is free to use the one provided by the Pirate Bay. They don’t discriminate.
In the case of the private tracker, you need to apply for permission before using it. Usually, you need to register with the owner of the tracker and then request access. There are usually conditions that you have to comply with in order to become a member of that tracker.
Private trackers have become a way for the file-sharing community to keep out nosy authorities and organizations. Whether it actually achieves that goal is another story entirely. Private trackers are, however, a good way to make blazing-fast torrents. Often, the people on a private tracker promise to seed extensively and have dedicated bandwidth for torrenting in one form or another. Of course, none of this matters if no one is sharing files that you want. The only way to fix that is by joining a private tracker group that trades in the sort of content that you are interested in.
It’s in the private sphere where tracker technology is still popular. Since it allows for control over who gets to be in the swarm and who doesn’t. If there’s no tracker, how does it all work? Let’s look at trackerless torrenting.
Trackerless Torrenting
Several technologies have come to the fore that make the need for a central torrent tracker obsolete. There are three that really matter: DHT, PEX and Magnet links.
- 'DHT' refers to distributed hash tables. These tables allow your client to find other peers in the swarm who are downloading the same files as you. The key point of DHT technology is that it can achieve this without talking to any sort of central computer, like a tracker.
- 'PEX' or Peer Exchange is yet another protocol that is used to boost the abilities of the BitTorrent protocol. The way that PEX works is both simple and a stroke of genius. Basically, your client will look for other peers connected to more peers. This is how your you can easily join a huge swarm and download files. In this way, any one client can quickly find peers to share data with, as long as they can find at least one peer that has connections to other peers.
- 'Magnet' links are a special string of characters that are created by running a traditional torrent file through a special process. This process, known as hashing, returns a unique pattern of data that’s like a fingerprint of the torrent file. Instead of downloading the torrent file, you just open the magnet link using your client. The client can then search the DHT network for the right hash value. If it finds a peer on the DHT network that’s downloading the same file as you, it can then request the torrent file itself and then join the swarm. No tracker needed.
These three technologies can’t replace trackers individually, but if you combine the three of them, we can safely say goodbye to trackers.
What is a Peer?
Although we have briefly defined network peers above, in the context of BitTorrent - any device that runs a torrent client program is a peer. In physical terms, a peer is any device that runs a torrent client. It could be a home computer, a virtual machine on a server somewhere or even an embedded device. As long as the device can run a torrent client, it can act as a peer.
What Are Seeding and Leeching?
In the BitTorrent parlance, a seed is a peer that has a complete copy of the file in question and has left that torrent active. As long as there is at least one active seed in the torrent swarm it is possible for the file to be shared. As peers complete their downloads, they’ll start seeding the file back to the swarm as long as the peer’s user does not stop the torrent. Learn more about how P2P seeding works.
A leech is basically a client that has taken more than they’ve given. Once your seed ratio is greater than one (in other words you’ve given at least one full copy of the data back) you aren’t a leech. Many people don’t provide a full copy back before leaving the swarm. This is usually because such people are on metered accounts or they have limited upstream bandwidth, such as on ADSL lines. Leeching isn’t bad per se, but trackers might limit the download speeds of clients that have a ration that’s not generous enough.
The Legality of BitTorrent
Due to the nature of BitTorrent, it has become a very popular way to trade files that are illegal in some way. These often included video games and software packages that have had their copy protection removed. Although with the shift to software as a service (SaaS), the latter is less common now.
Music, TV shows, films and even books are made available via torrents - a fact that has sent the various media industries into fits over the years. Content creators are convinced that piracy via torrents is hurting their profits, but it’s difficult to actually prove this. After all, just because someone pirates your movie does not mean that you have lost a sale. Recently, it has come to light that in the case of video games at least there is no sign of hurt sales and piracy might actually have a net positive effect on the games industry.
Despite these general observations about piracy via BitTorrent, you can imagine that powerful players are keen to paint torrent technology as being inherently illegal and immoral.
The truth is that BitTorrent technology is legal. As long as you use it for legal purposes, you have nothing to worry about. However, since the technology has such a reputation, many ISPs will monitor your data for P2P activity. Some might block it outright, while others will throttle the speed down to some ridiculously low level.
Legitimate Uses of BitTorrent
All the hoopla around piracy can sometimes make us forget that at its core, torrent technology is powerful and revolutionary. So while it may not make it into the news much, it should come as no surprise that plenty of legal uses have been put into place for the BitTorrent technology.
Software Updates
OK, strictly speaking, it’s not Bittorent proper, but the P2P system that Microsoft uses to share updates is definitely inspired by this pioneering protocol. It’s not just Windows either. Popular games such as League of Legends also makes use of P2P technology to distribute updates without overloading their central servers.
Digital Distribution
We are almost past the era of physical media. People are moving towards buying their content in digital form and then just downloading or streaming it. That’s great for consumers, but hosting all that content and providing bandwidth so that millions of people can download is not a cheap endeavor. It’s okay if you’re Netflix, Steam or Sony. Smaller companies, however, either have to sell through someone bigger or rely on P2P technology to help them spread the cost of bandwidth.
How To Download Torrents & Engage in P2P Traffic?
OK, enough about the mechanics of torrent technology. Let’s see how you can actually use torrents yourself. We’ll look at the tools you need to torrent, how to make your own torrent and of course how to download the torrents of others.
What Are Torrent Clients?
Torrent clients are the software programs that you open torrents with. It’s here where you can monitor downloads and make certain decisions about things like bandwidth allocation. In other words, having a torrent client is an essential prerequisite before diving into P2P file-sharing.
To get started, we recommend taking a look at our overview of the best torrent clients for Windows, as well as the best clients for MacOS. This is where you'll get to see brief overviews of the most popular options that will help you get the job done, including download links as well. Then, you can also download torrents on Android, and there are some Web-based torrent clients for iOS. As you can see, every popular platform is covered.
Finding Torrent Files Online
When you go to a site that hosts torrents, you can get the torrent into your client either by downloading the torrent file yourself or clicking on the magnet link, which should automatically open in your BitTorrent client. Therefore, you need to know the best torrent sites out there. However, please be aware of what you're downloading since you want to stick to what's legal. To download torrents without any limits, take a look at the best legal torrent repositories. Finally, you can also use torrent search engines if you don't want to stick to a single repository.
Creating Your Own Torrent
While most people who use torrents are more interested in downloading files than providing their own, there are plenty of reasons to create your own torrent.
For one thing, file hosting and distribution can be expensive and complex to manage. If you have one computer that acts as a seed, then you can serve your files to anyone on the Internet. Also, it’s common practice these days for small sites to offer a direct download link and a torrent link for their files. Charity organization Humble Bundle, for example, offers torrents as an alternative download option. Open-source software providers, such as Canonical with Ubuntu Linux also use BitTorrent to reduce their file hosting bills.
Creating your own torrent is pretty easy and all you need is access to a torrent client like uTorrent. Then, check our article on how to create your own torrent files.
If you only want to share the file with specific people, you can simply send them the torrent file or magnet link directly. If you want to make the torrent public, then you need to upload it to your site of choice. You can then post a link to it from your own site or wherever else you might need it. Remember to keep seeding your file at least until there are a healthy number of alternate seeds in the swarm.
Privacy Concerns of Torrents
Peers that are part of a BitTorrent swarm all reveal their IP addresses when they connect. Usually, your BitTorrent client will show you a list of all the peers you are connected to along with their IP addresses. This means that law enforcement or media lawyers can record all the IP addresses of the people who are currently sharing a particular file or files. There have been many cases where ISPs will send letters to people if their IP is linked to illegal torrenting. Depending on the country you live in, there may be a number of warnings or you may be taken to court rather quickly. It’s possible to be saddled with hefty fines or worse.
Even though some courts have found that an IP address is not enough to link a specific person to an illegal activity, it’s better to play it safe. The most straightforward way to do that is by hiding your IP address from the swarm. If you can do that, other peers can’t see where you are or which ISP you’re with.
There are two good ways of doing this. One is to use a VPN and the other is to use a seedbox. Let’s see what each option has to offer.
What is a VPN?
The acronym 'VPN' is short for Virtual Private Network. It’s a technology that helps keep your Internet activity private from your ISP and any other curious parties who’d like to know what you are up to online.
Like BitTorrent, a VPN also uses special protocols that describe how your computer should communicate with other devices. However, in this case, the protocol tells your computer how to speak with the VPN server in such a way that only the two of them can understand each other. This is called a network tunnel and uses special encoding methods known as VPN encryption to keep it all hush-hush.
Why Use a VPN with BitTorrent?
VPNs have neatly achieved two important goals when it comes to torrent privacy. First of all, they hide your IP address. Anyone on the other end of the connection, such as the other peers in the swarm, only see the IP of the VPN server. That server can be almost anywhere in the world. This would make it pretty hard for anyone to track it back to you!
You encrypt all your network traffic with a VPN. Which means the service provider has no idea what information is traveling between you and the VPN server. That means they can’t intercept your torrent downloads to check its contents. They also can’t throttle down the speeds of your torrent because they simply don’t know what is or isn’t a torrent.
The VPN Learning Curve
VPNs are powerful Internet privacy tools that apply much more widely than just BitTorrent. They do require a little homework on your part, however, if you want to make the most of them.
We have explained the main points you should consider in our VPN Buyer’s Guide. We also have a running list of the very best VPN options that you can look at to help find the right service. You should also know that, depending on where you live, there may be legal issues with VPNs. For most people, however, that’s not the case. You should also be aware of the pros and cons of VPNs. It’s not a perfect technology by any means, so you need to use it with enough knowledge of the limitations.
What is a Seedbox?
Seedboxes are an interesting way to use torrenting technology. It combines torrents with traditional downloading to give you the best of both worlds. At least in some cases.
A seedbox is a (usually) paid server. In most cases, it’s a virtual machine running on a large server. You pay a monthly fee and for that, you get a dedicated amount of storage space and bandwidth. The seedbox usually has a Web interface which gives you access to a torrent client and a few other related tools.
Seedboxes offers various ways to download your files, but using an SFTP client or another type of secured, encrypted file transfer protocol. This means that the contents of the files you are downloading can’t be seen by your ISP or anyone else.
Why is it Called a Seedbox?
That’s actually an important point. A seedbox lets you seed as much as you want (or have paid for) without affecting your local upstream bandwidth. It will keep seeding as long as your subscription is paid and you are under your quota limit (if any). For people who are using private trackers, this means you can get some truly amazing download speeds to the seedbox. If you are putting files up that you want to distribute, then once again a seedbox is an excellent solution. At least until there are enough whole copies of your files out there.
Why Use a Seedbox?
There are quite a few good reasons to use a seedbox instead of torrenting directly. Chief among them is the improved anonymity you get. Only the seedbox has its IP exposed, so your home connection is never listed among the peers on the torrent file.
The connectivity of dedicated seedboxes also tends to be much better than the average home connection. Large torrents often download to the seedbox in minutes or even seconds. Which means your files are safe and sound quickly.
As we said above, you also get shielded from your ISP. Although they can see your sending and receiving information from a Seedbox, they can’t see what it is. Seedboxes are also a good way to get around ISPs that throttle P2P traffic. Since you receive the file through a common protocol such as SFTP, you should get the full speed you are paying for.
A Note On Torrent Client Encryption and Proxies
Seedboxes and VPNs are not the only two methods that can help keep your torrent activity under wraps. Many people use proxies and the built-in encryption protocols of their torrent clients towards the same purpose.
This is certainly better than doing nothing at all, but it is far less secure than a VPN solution. A proxy just passes your information on. It doesn’t obscure any part of your traffic from anyone. While the encryption protocol of your torrent client may help to mask the torrent data from your ISP (which can prevent throttling), it’s not an obfuscation of your torrent’s contents. You need a VPN or encrypted transfer from a seedbox to stop everyone from seeing what you are downloading.
Final Thoughts
As you’ve seen, BitTorrent technology is pretty awesome. It’s also perfectly legal and is used for many legitimate uses. Because so many people have used BitTorrent for illegal purposes, the technology itself carries a stigma it really doesn’t deserve. None of that should be a reason for you to avoid responsible torrent use. Ultimately, you can benefit from torrent technology without getting on the wrong side of the authorities.
In case you found this article to be useful, why not share it online? Also, don't forget to follow us on Facebook and Twitter to get the latest information first. Thanks!