How Hackers Use Coronavirus Panic to Their Advantage
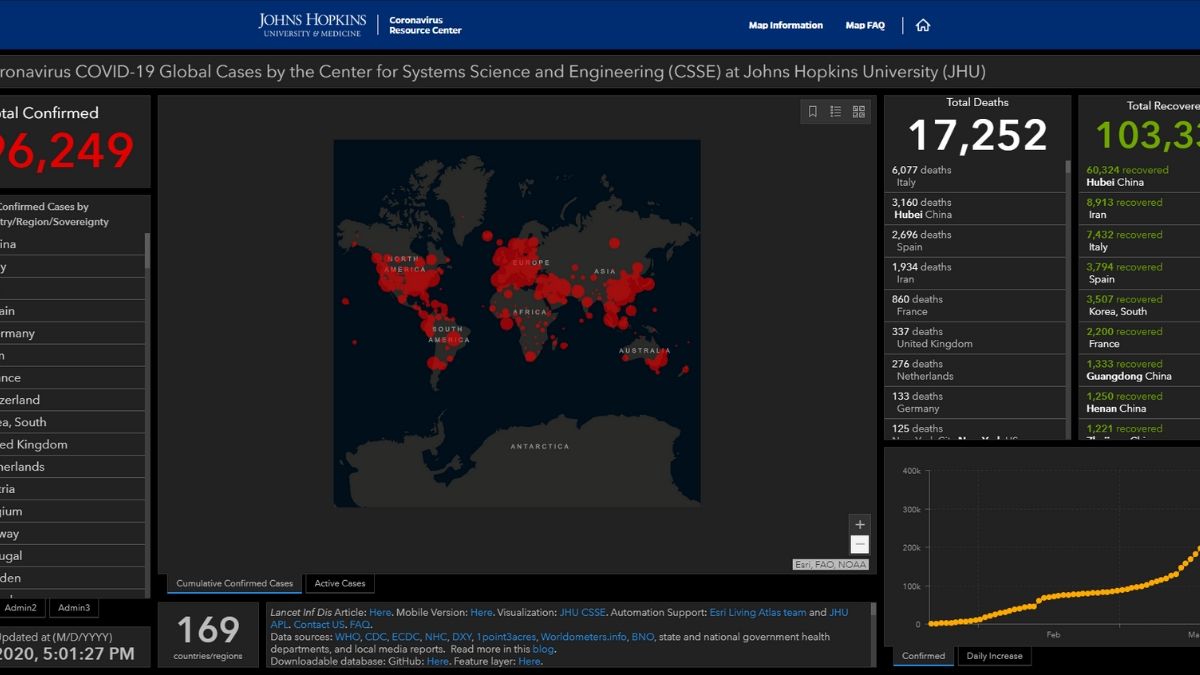
With nearly 400,000 confirmed cases and over 17,000 deaths (numbers that will likely increase soon), it's no surprise Coronavirus has caused a worldwide crisis. Yet even now, cybercriminals are looking for ways to exploit the virus for their gain.
In this quick article, we're going to take a look at how hackers use Coronavirus, and we'll also offer you some tips on how to protect yourself - both online and offline.
Here's How Hackers Use Coronavirus in Their Attacks
Cybercriminals are always crafty, but they're doing overtime during this pandemic. Here are the four types of cyberattacks they've been using so far:
1. Malicious Live Coronavirus Maps
Live Coronavirus maps are very popular right now since people use them to stay up to date with the pandemic 24/7.
Well, hackers noticed that and quickly took advantage of it. According to this article, they're using this legit map from John Hopkins University on malicious websites. Apparently, it all started with a Russian hacker selling digital Coronavirus infection kits online.
If you end up interacting with a malicious map, it can infect your computer with malware. What's more, the malware might even use your network to spread to other devices.
2. Fake Apps
Besides live maps, people have also started using tracking apps to receive updates about the latest Coronavirus trends and news. Unfortunately, hackers are one step ahead of everyone, so they started publishing malicious fake apps.
Take CovidLock, for example. It said it was a Coronavirus tracking app, but in reality, it was just ransomware. If you were to use it, it would lock your phone, and hold your data until you paid $100 ransom in Bitcoin.
As a general rule of thumb, don't download a tracking app that's new to the store, has vague descriptions with typos, and 5-star reviews with just a few words. It's best to just use the John Hopkins University live map we linked above since it works well on phones.
3. Phishing Attacks That Prey on Fear and Panic
Simply put, phishing is when a hacker tries to trick you into interacting with malicious files or links or revealing sensitive information by using fake messages through multiple channels (emails, instant messages, phone calls, etc.)
Scammers have been particularly active when it comes to Coronavirus-themed phishing. According to data, over 4,000 Coronavirus-related domains were registered globally since January.
Security experts estimate that at least 5% of those domains are malicious, and an additional 5% are suspicious. What's more, they say that the malicious rate for those domains is 50% higher than the one for the regular domains registered in the same period.
So what's the end goal here? Pretty simple - hackers set up fake websites where they try to harvest login credentials, bank account details, or credit card numbers from unsuspecting victims. To get people to land on those websites, they use phishing messages, which they either send from fake email addresses or legit addresses they took over.
How do hackers use Coronavirus in their phishing attacks, though? Well, here are the most common scenarios they make up:
- Fake vaccines - Some scammers send messages that claim to be from made-up doctors who are working on a Coronavirus vaccine. The emails contain a link to a free "cure review." If people click on it, hackers harvest their login credentials.
- Fake guidelines - Some phishing messages play on people's fears and try to convince them to download an attachment that is supposed to be a guideline from the WHO on how to avoid spreading Coronavirus. In reality, it's a malicious file that installs keyloggers on your device.
- Fear-inducing claims - Cybercriminals like to pretend they're legit health organizations (CDC, WHO, etc.) by using spoofing tools. They then send fake announcements ("Coronavirus outbreak in your city" or "The virus is now airborne") through email and try to convince people to access malicious links or download malware-infected files.
- Tax refund scams - Hackers try to convince people they can get an instant tax refund during this crisis if they access the link in the emails they send. If people click on the link, they're taken to a fake website where they're asked to type in their financial and tax information.
- Donation scams - A different take on Coronavirus phishing, these messages claim to be from the CDC and ask people to donate for the development of a vaccine. If that weren't shady enough, the scammers also ask people to send donations to a Bitcoin address. Safe to say, they'll likely never get their money back.
If you want to read more about examples of how hackers use Coronavirus-themed phishing attacks, check out this article from the BBC.
4. DDoS Attacks
DDoS (Distributed Denial of Service) attacks are a way to flood a network with unwanted requests and traffic until it's forced offline. Basically, it's a way to shut down your Internet access for a few hours or days.
Hackers have been more active with DDoS attacks recently. They tried to (unsuccessfully) target the US Health and Human Services Department. Also, they DDoS-ed a food delivery service in Germany right when people need it the most.
This trend will likely continue, and hackers will probably start targeting businesses as they move to the work-from-home model to cause downtime. As a regular Internet user, you probably won't get targeted. But you'll still feel the effects if cyber-criminals decide to start targeting ISPs.
How Can You Protect Yourself?
How hackers use Coronavirus in their attacks is pretty interesting, but also very scary. Things are already bad enough, and the last thing you need is to worry about or deal with cyber attacks. Luckily, there are things you can do to minimize your chances of becoming a victim:
Avoid Phishing Attack
Since phishing attacks are the go-to option for most hackers right now, you need to learn how to avoid it. Similarly, if you're an employer, you need to offer company-wide training.
Some must-know tips include:
- Always check the sender's email address. See if it's the same as the contact name they give you. Also, google the names used in the messages to see if the people really exist.
- Search parts of the message between quotes on Google. That way, Google will display exact matches for your search. You might find forums or Reddit threads where people are talking about said message and calling it a scam.
- Don't click on any links. Hover over them instead. You'll see if the domain address or destination link is shady (like "bit.ly/33Itb0S" instead of a regular URL).
- Don't download or open any attachments - especially if you see they have weird extensions (like .jpg for a Word document).
- Don't answer numbers you don't know. They might be vishing attempts.
- Always ask for a second opinion - your boss, a coworker, or the police. Also, you can contact the CDC or the WHO on Twitter or Facebook.
Also, you should consider installing extensions that might help protect you from phishing. uMatrix and uBlock Origin are open-source script blockers that can stop harmful scripts from stating up if you accidentally access a phishing page. Stanford's Anti-Phishing Browser Extensions are great too.
If you want a more in-depth look at how to deal with Coronavirus phishing messages, check out this guide from the Electronic Frontier Foundation.
Secure Your Devices
Since malware is the name of the game for most hackers, you need to protect your devices from it. The last thing you want is to accidentally connect to an unknown network, and a hacker to take over your phone or laptop. The best way to do that is with reliable antivirus software - like Malwarebytes or Bitdefender, for example.
You can also go the extra mile and secure your network, too. One smart way to do that is to get a secure router that offers malware protection. We have a list of recommendations.
Alternatively, you can check out software solutions like McAfee Secure Home Platform or BullGuard Premium Protection.
Also, and don't be confused if you see people referring to antivirus software as antimalware software. They're interchangeable terms since a virus is a type of malware.
Use VPNs When Working Remotely
A VPN is an online service that encrypts your traffic when you're online. It won't stop malware infections, but it will keep your data safe if:
- You accidentally connect to a fake hotspot.
- A hacker intercepts your connections on unsecured WiFi networks.
- Cybercriminals compromise remote connections to the company network
Besides that, it also hides your IP address, which can potentially help you keep your network safe from DDoS attacks.
VPN usage actually increased during this pandemic. If you want to read about that and find out what kind of VPN you should use for your business, check out our article.
As a side note, if you just started working from home, think you'll be doing it for a long time, and are willing to invest to get the best experience, here's a list of gadgets you should look into.
Get DDoS Protection
If you run a business, DDoS attacks are not just going to take you offline for a few hours. They can also cause damages anywhere between $120,000 to $2 million.
So, if you want to be 100% sure hackers won't DDoS your servers during this crisis at all, you should buy DDoS protection. Some of the best options include AWS Shield, Verisign DDoS Protection, and Cloudflare.
Start Using Password Managers
Since most hackers use phishing to steal passwords, you need a good way to protect them. That's what a password manager is for.
Basically, it's software that uses encryption to secure all your passwords in one place. What's more, it automatically fills in login fields for you, and it only does it on websites you whitelisted. It won't do that on phishing websites. In fact, most tools will even alert you you're on a shady site.
There are plenty of options on the market, so here's a guide to make things easier for you.
Will Things Get Better?
It's hard to say. Cyber-attacks have been on the rise before the whole Coronavirus crisis even started. So, even when the pandemic will be over, hackers will just find new ways to prey on unsuspecting victims.
That's why you always need to be proactive when it comes to online security. At the very least, you should use a password manager, antivirus software, and a VPN.
Have any extra information about how hackers use Coronavirus to exploit this crisis? Go ahead and tell us your thoughts, either here in the comments or on social media.